A previously unknown APT group, tracked as Carderbee, was behind a supply chain attack against Hong Kong organizations.
Symantec Threat Hunter Team reported that a previously unknown APT group, tracked as Carderbee, used a malware-laced version of the legitimate Cobra DocGuard software to carry out a supply chain attack aimed at organizations in Hong Kong. The group attempted to infect target organizations with the Korplug backdoor (aka PlugX).
The attackers signed malware with a legitimate Microsoft certificate.
Cobra DocGuard Client is software produced by a Chinese firm EsafeNet, it is used to protect, encrypt, and decrypt software. EsafeNet is owned by Chinese information security firm NSFOCUS.
In September 2022, ESET researchers first documented a malicious update to the Cobra DocGuard Client that was used to compromise a gambling company in Hong Kong.
The attack was attributed to the China-linked APT group Lucky Mouse (aka Emissary Panda, APT27 and Threat Group 3390).
In the recent attacks, the APT group infected 100 computers in the impacted organizations, but researchers pointed out that the Cobra DocGuard Client application was installed on roughly 2,000 endpoints, suggesting that the attackers focused on high-value targets.
At this time, the experts have yet to determine the exact attack chain to conduct the supply chain attack.
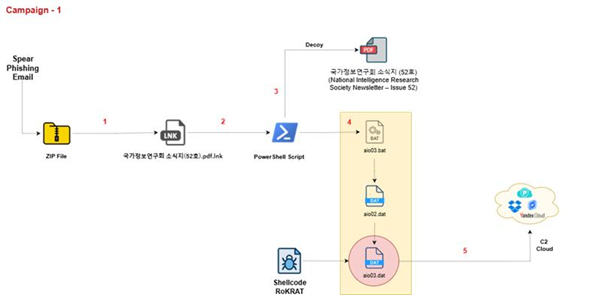
“The malicious software was delivered to the following location on infected computers, which is what indicates that a supply chain attack or malicious configuration involving Cobra DocGuard is how the attackers compromised affected computers:
“csidl_system_driveprogram filesesafenetcobra docguard clientupdate”
‘” reads the report published by Syamtec.
The researchers observed attackers downloading multiple distinct malware families via this method. In one interesting case, the threat actors deployed a downloader that was digitala ly signed certificate from Microsoft, called Microsoft Windows Hardware Compatibility Publisher. This downloader was used to install the Korplug backdoor on the infected systems.
“The downloader attempted to download a file named update.zip from the following location: http://cdn.stream-amazon[.]com/update.zip.” continues the report. “The update.zip file is a zlib compressed archive file. It decompresses and executes a file named content.dll. This file is not saved on disk. It acts as a dropper and contains x64 and x86 drivers, which are dropped depending on the system environment. The dropper creates services and registry entries. The dropped drivers read encrypted data from the registry, decrypt it, and inject it into svchost.exe. The injected payload is the Korplug backdoor. “
The Korplug implant employed in the attacks enabled the attackers to execute commands via cmd, enumerate files, check running processes, download files, open firewall ports, act as a keylogger.
“It seems clear that the attackers behind this activity are patient and skilled actors. They leverage both a supply chain attack and signed malware to carry out their activity in an attempt to stay under the radar. The fact that they appear to only deploy their payload on a handful of the computers they gain access to also points to a certain amount of planning and reconnaissance on behalf of the attackers behind this activity.” concludes the report. “Software supply chain attacks remain a major issue for organizations in all sectors, with multiple high-profile supply chain attacks occurring in the last 12 months, including the MOVEit, X_Trader, and 3CX attacks.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, Carderbee)