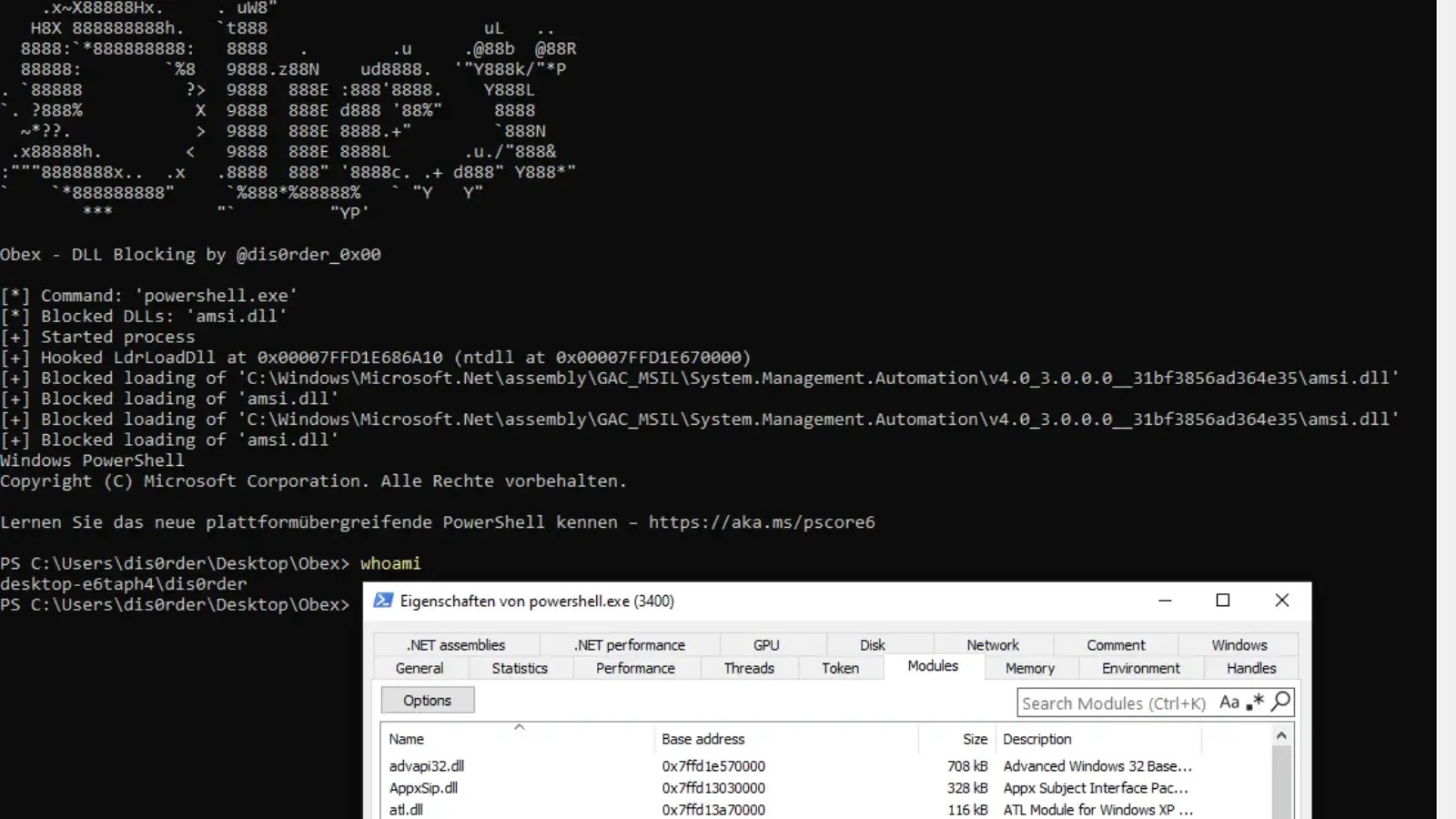
New Obex Tools Blocks Runtime Loading of EDR Dynamic Libraries
Obex, a newly released proof-of-concept utility by security researcher dis0rder0x00, demonstrates a simple but effective user-mode method to stop unwanted security and monitoring modules from…