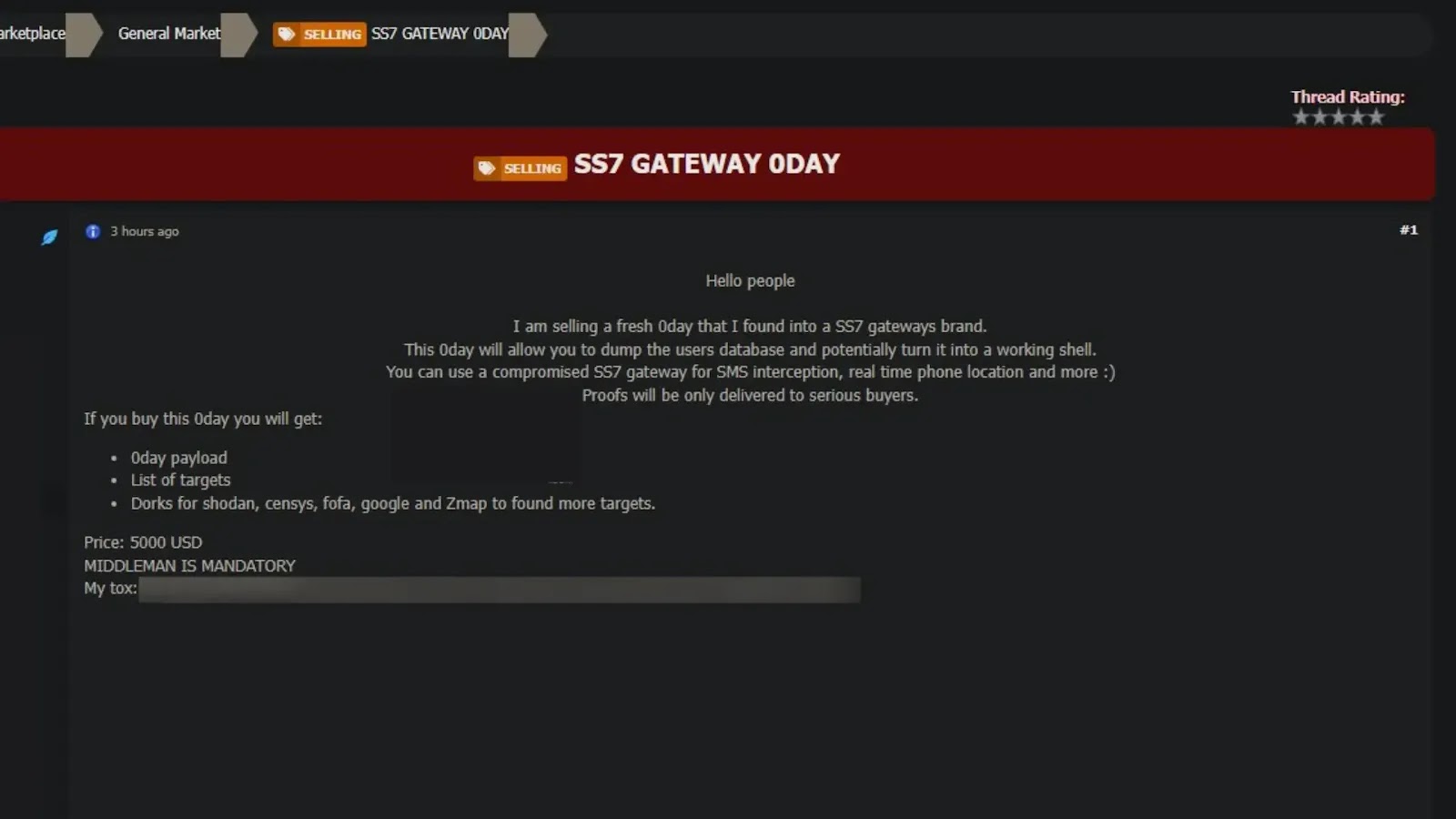
884,000 Credit Card Details Stolen from 13 Million Global User Clicks
The Darcula group has orchestrated a massive phishing-as-a-service (PhaaS) operation, dubbed Magic Cat, compromising an estimated 884,000 credit card details from over 13 million user…