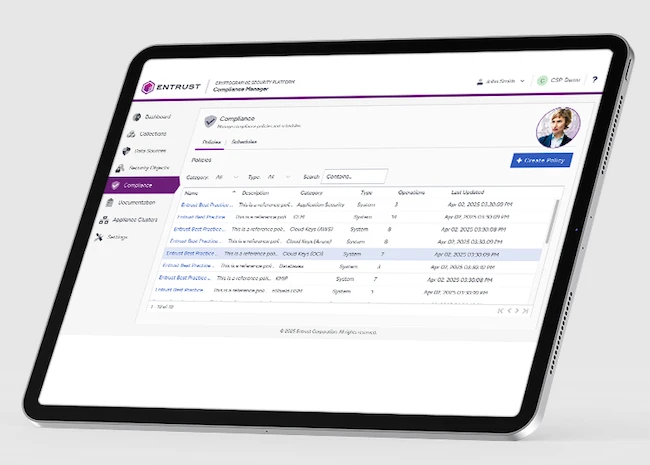
Entrust Cryptographic Security Platform provides visibility into cryptographic risk posture
Entrust announced the Entrust Cryptographic Security Platform, a unified, end-to-end cryptographic security management solution for keys, secrets, and certificates. Cyberattacks on data security and identity…