Darcula allows tech-illiterate crooks to create, deploy DIY phishing kits targeting any brand
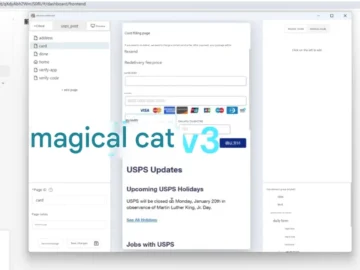
A new, improved version of Darcula, a cat-themed phishing-as-a-service (PhaaS) platform aimed at serving Chinese-speaking criminals, will be released this month and will allow malicious…