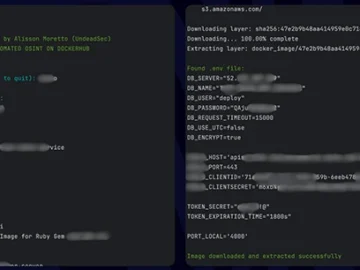
DockerSpy: Search for images on Docker Hub, extract sensitive information
DockerSpy scans Docker Hub for images and retrieves sensitive information, including authentication secrets, private keys, and other confidential data. “DockerSpy was created to address the…