IntelOwl: Open-source threat intelligence management
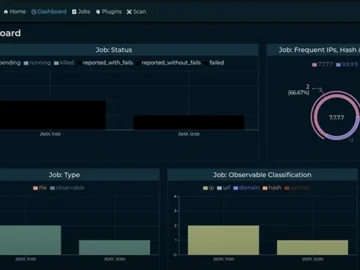
IntelOwl is an open-source solution designed for large-scale threat intelligence management. It integrates numerous online analyzers and advanced malware analysis tools, providing comprehensive insights in…