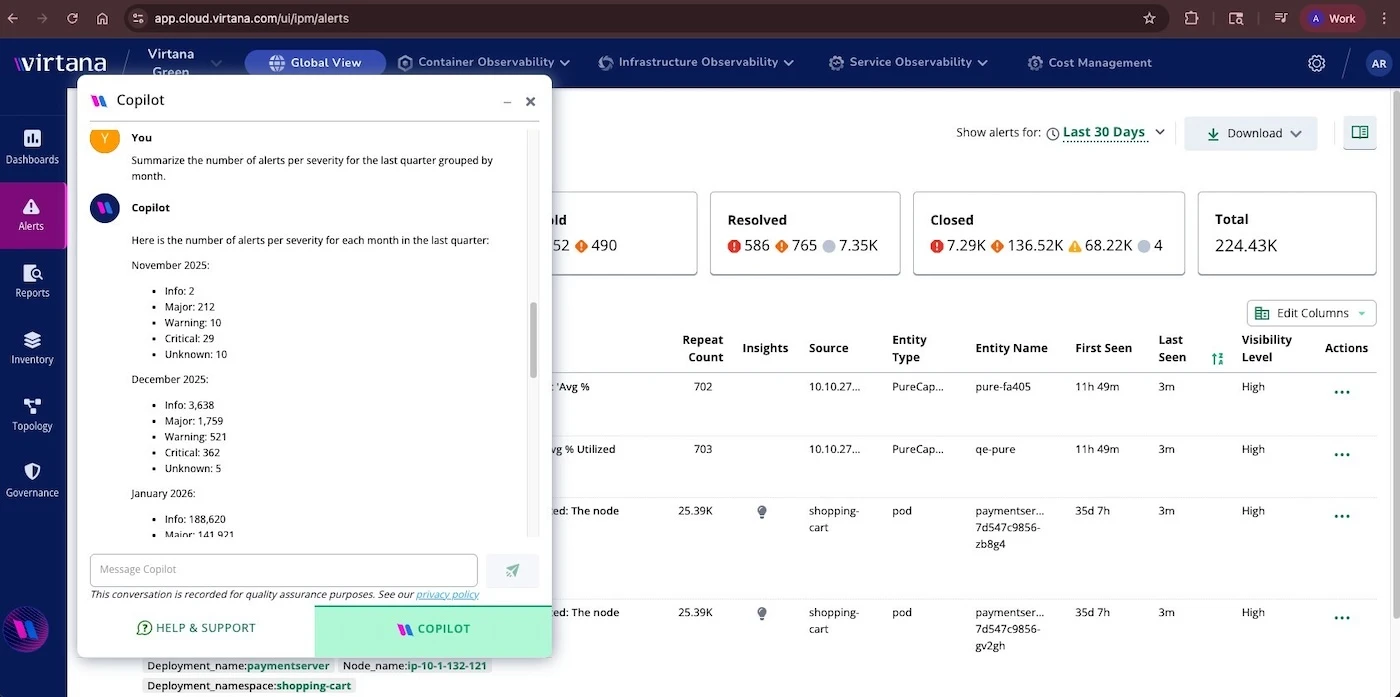
Microsoft reveals critical Windows Admin Center vulnerability (CVE-2026-26119)
Microsoft has disclosed a privilege-escalation vulnerability in Windows Admin Center (WAC), a browser-based platform widely used by IT administrators and infrastructure teams to manage Windows…