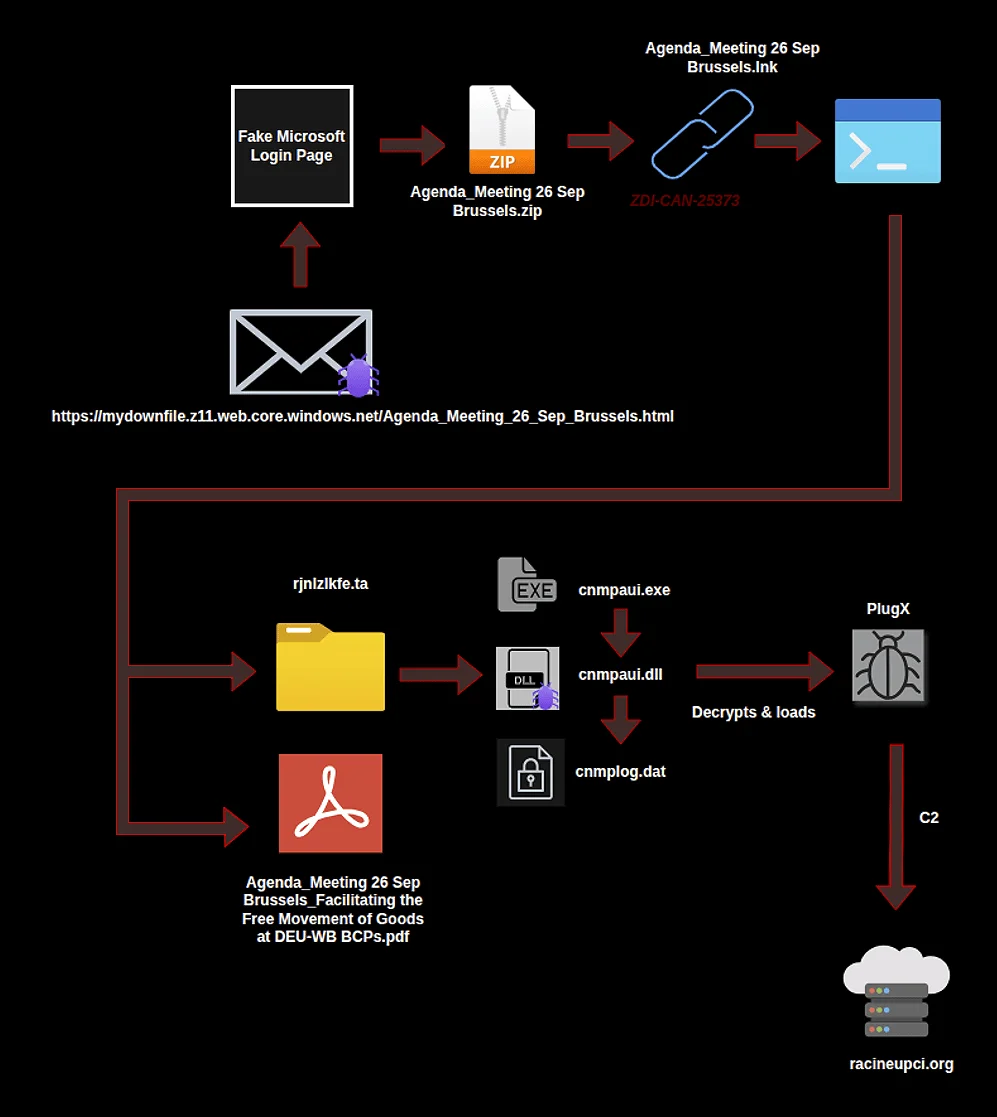
Cyber-espionage campaign mirroring Sandworm TTPs hit Russian and Belarusian military
A spear-phishing campaign aimed to compromise Russian and Belarusian military personnel by using military-themed documents as a lure has been flagged by Cyble and Seqrite…