Cryptojacking Campaign Exploits DevOps APIs Using Off-the-Shelf Tools from GitHub
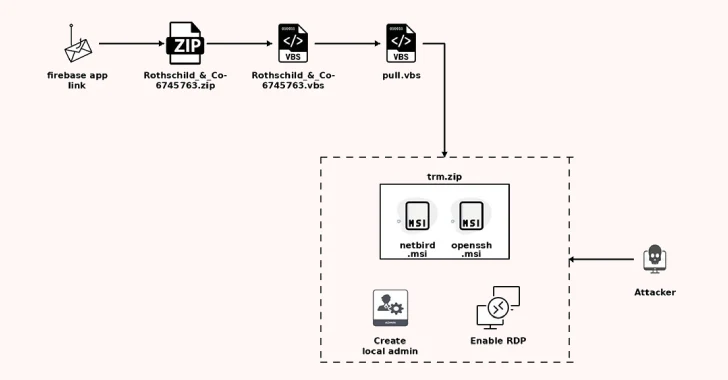
Cybersecurity researchers have discovered a new cryptojacking campaign that’s targeting publicly accessible DevOps web servers such as those associated with Docker, Gitea, and HashiCorp Consul…