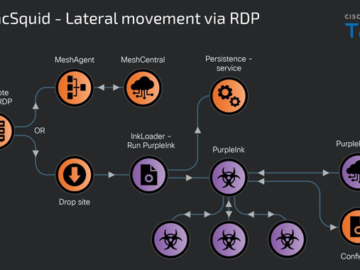
Russian Hackers Target Europe with HeadLace Malware and Credential Harvesting
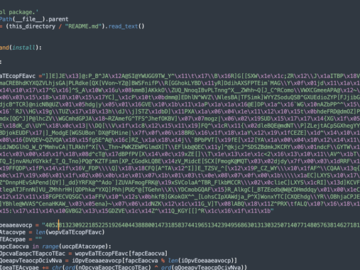
May 31, 2024NewsroomCyber Attack / Credential Harvesting The Russian GRU-backed threat actor APT28 has been attributed as behind a series of campaigns targeting networks across…