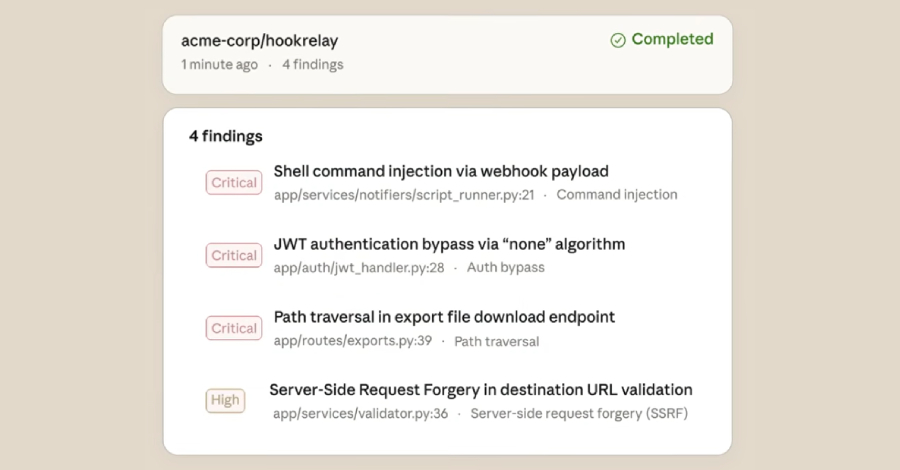
APT28 Targeted European Entities Using Webhook-Based Macro Malware
Ravie LakshmananFeb 23, 2026Malware / Threat Intelligence The Russia-linked state-sponsored threat actor tracked as APT28 has been attributed to a new campaign targeting specific entities…