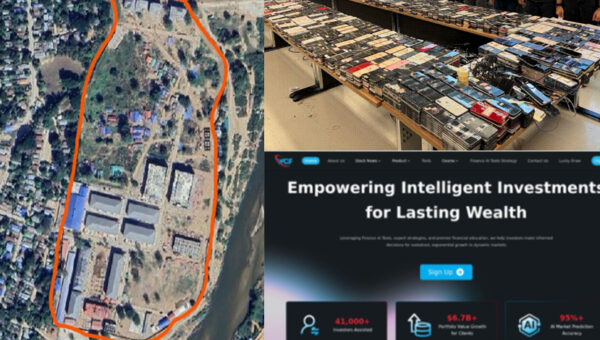
Global Crackdown Arrests 276, Shuts 9 Crypto Scam Centers, Seizes $701M
A coordinated international operation involving U.S. and Chinese authorities has arrested at least 276 suspects and shut down nine scam centers used for cryptocurrency investment…