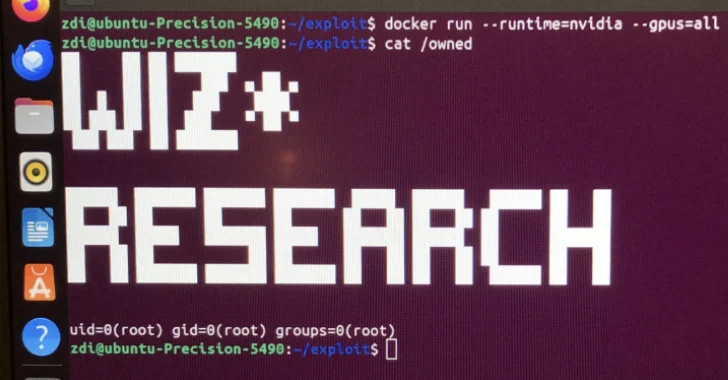
Critical NVIDIA Container Toolkit Flaw Allows Privilege Escalation on AI Cloud Services
Jul 18, 2025Ravie LakshmananCloud Security / AI Security Cybersecurity researchers have disclosed a critical container escape vulnerability in the NVIDIA Container Toolkit that could pose…