CharlieKirk Grabber is a Python-based Windows infostealer that focuses on rapid “smash‑and‑grab” credential theft and data exfiltration rather than long-term system control or destructive behavior.
It targets browser‑stored passwords, Wi‑Fi keys, Discord tokens, and gaming sessions, then exfiltrates the collected data via third‑party file hosting and encrypted Discord or Telegram channels.
| File Name | CharlieKirk.exe |
| File Size | 19.58 MB |
| File Type | Executables |
| Signed | Not Signed |
| MD5 Hash | 598adf7491ff46f6b88d83841609b5cc |
| SHA 256 | f56afcdfd07386ecc127aa237c1a045332e4cc5822a9bcc77994d8882f074dd1 |
| First seen wild | Feb 2026 |
Executed under the logged‑in user context, the binary immediately initializes environment variables, prepares a working directory, and launches multiple data collection threads to minimize execution time and user visibility.
This multithreaded model mirrors other modern Python stealers that emphasize speed and automation for large‑scale credential harvesting.
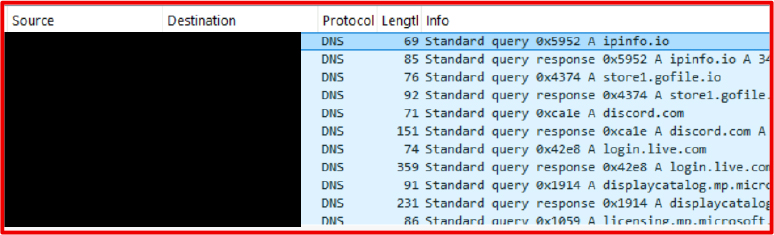
On startup, CharlieKirk Grabber profiles the host using native commands such as SYSTEMINFO and WHOAMI, capturing username, hostname, hardware UUID, OS details, and network configuration, and then queries an external IP information service to obtain the public IP, ISP, location, and time zone.
According to the report, the malware operates as a smash-and-grab threat, focusing on immediate data theft rather than persistence or long-term system control.
All profiling output is written into local files within a temporary directory, laying the groundwork for later consolidation and exfiltration.
CharlieKirk Grabber Malware
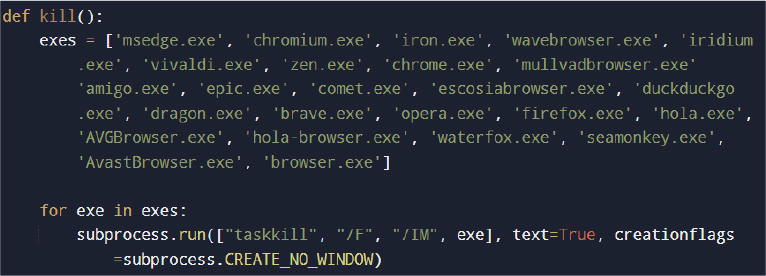
To access locked browser databases, the malware forcibly terminates active browser processes using TASKKILL and other Windows utilities, suppressing visible windows with CREATE_NO_WINDOW to remain unobtrusive.
The malware attempts to establish persistence by copying its executable to a specified directory and creating a scheduled task configured to execute at user logon.
It then enumerates multiple Chromium‑based browsers, extracts the master key from each Local State file, and uses AES‑GCM decryption to recover saved logins, cookies, autofill data, and history from SQLite databases such as Login Data, Cookies, Web Data, and History.
Firefox and other Gecko‑based browsers are targeted via NSS, where encrypted entries in logins.json are decrypted using PK11SDR_Decrypt to expose stored passwords and related data.
Beyond browser stores, CharlieKirk Grabber abuses NETSH to list Wi‑Fi profiles and parse the Key Content field in cleartext, enabling theft of wireless network passwords.
It hunts for Discord authentication tokens across standard storage paths, decrypts them using the same Chromium master key technique, and validates tokens against Discord APIs to extract account metadata such as username, email, phone, MFA status, and Nitro subscription details.
The malware also targets gaming ecosystems by collecting Minecraft session files and Steam session data, enabling account hijacking even without password reuse. Finally, it captures a desktop screenshot using Python imaging libraries and adds this to the staged data set.
Mitigations
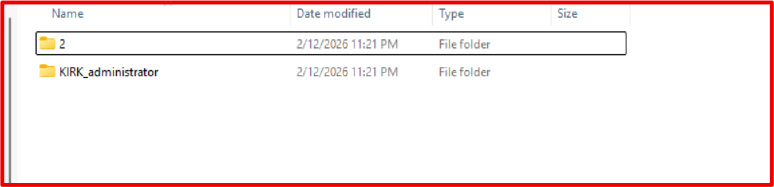
All harvested artifacts are staged under a temporary directory (for example KIRK_administrator under %LOCALAPPDATA%Temp), then compressed into a single ZIP archive for efficient transfer.
The archive is uploaded to a file‑hosting service such as GoFile, which returns a public download link frequently abused by commodity stealers for log trafficking.
That link is then sent to attacker‑controlled infrastructure via Discord webhooks or Telegram bots over HTTPS, leveraging trusted platforms and encrypted channels to blend with legitimate traffic.
After successful exfiltration, the malware deletes the temporary directory and archive, reducing forensic artifacts and aligning with “collect‑and‑pack” patterns seen across infostealer families.
CharlieKirk Grabber uses several defense‑evasion techniques but no sophisticated anti‑analysis capabilities.
It attempts UAC elevation using IsUserAnAdmin(), and when running with administrative rights, it invokes PowerShell to add Microsoft Defender exclusions via Add‑MpPreference, reducing the chance of on‑access detection.
It also creates a scheduled task via schtasks /sc onlogon to maintain persistence when configured, though its primary design remains fast data theft rather than long‑term footholds.
Behaviorally, it relies heavily on LOLBins (TASKKILL, NETSH, SYSTEMINFO, CMD, POWERSHELL) for discovery and credential access, mapping to ATT&CK techniques such as T1082 System Information Discovery, T1555.003 Credentials from Web Browsers, T1560 Archive Collected Data, T1562.001 Impair Defenses, and T1567.002 Exfiltration to Cloud Storage.
Defenders should monitor for abnormal patterns of forced browser process termination followed by intensive access to browser SQLite files and rapid ZIP archive creation within %TEMP% or %LOCALAPPDATA%.
Network monitoring should focus on unusual HTTPS connections to Discord webhooks, Telegram Bot APIs, and file‑sharing services like GoFile, especially in environments where such services are not business critical.
Strategic controls include enforcing MFA, limiting browser password storage, blocking unsanctioned file‑hosting platforms, and adopting Zero Trust principles to reduce the blast radius of stolen credentials.
At the endpoint level, organizations should enable EDR detections for netsh wlan show profile key=clear, suspicious PowerShell execution modifying Defender preferences, and execution of unsigned binaries from user‑writable paths such as %TEMP%, %APPDATA%, and %LOCALAPPDATA%.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.