Chatting with @Hacksplained about Bug Bounties and Infosec Jobs

Source link
Related Articles
All Mix →ZAP 2.12 살펴보기 ⚡️
Table of Contents UI Network Core to Addon Permanent Database Scan Rule Improve and Bugfix API False Positive New Deprecated Conclusion References 드디어 ZAP 2.12…
Reverse Engineering the Tapo C260 and Tapo Discovery Protocol v2
Earlier in 2025, I participated in the SPIRITCYBER IoT hardware hacking contest organised by the Cyber Security Agency of Singapore with YesWeHack. Among several devices,…
Pär Stålberg, Ottoboni: “As an agency, you don’t want a site you have built to get hacked”
Ottoboni is a Swedish web agency with an impressive list of customers including some of the country’s largest companies and government authorities. Today, the agency…
Nothing In, Nothing Out
High quality intellectual output comes from high-quality intellectual input. People who don’t consume ideas tend not to have any. And if they do have some,…
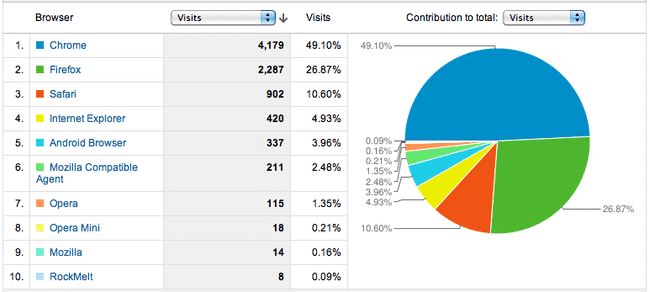
Interesting Web Data from a Day on the Front Page of Hacker News
I spent yesterday on the front page of Hacker News for my git primer, which resulted in over 12K page views and some fascinating insight…