A highly sophisticated China-linked threat actor, identified as UAT-9244, has been actively targeting critical telecommunications infrastructure across South America since 2024.
Security researchers assess with high confidence that UAT-9244 exhibits close operational overlap with known espionage groups such as FamousSparrow and Tropic Trooper.
To maintain a strong foothold in victim networks, the hackers deploy a unique three-stage malware arsenal.
According to new research from Cisco Talos, this advanced persistent threat (APT) group uses a combination of Windows and Linux malware to infiltrate endpoints and network edge devices.
The Three-Pronged Malware Arsenal
UAT-9244 relies on three distinct malware implants to compromise different parts of a target’s infrastructure.
The primary implant, “TernDoor,” is a custom Windows backdoor and a newly discovered variant of the older CrowDoor malware.
TernDoor uses dynamic-link library (DLL) side-loading to bypass security defenses. The attackers execute a benign file named “wsprint.exe,” which unknowingly loads a malicious loader that decrypts the final payload.
TernDoor allows the attackers to execute arbitrary remote commands, manage files, and gather sensitive system data.
It also deploys an embedded, AES-encrypted Windows driver (WSPrint.sys) capable of suspending or terminating security processes to evade detection.
Interestingly, TernDoor features a single command-line switch, -u, which allows the attackers to seamlessly uninstall the malware and erase their tracks.
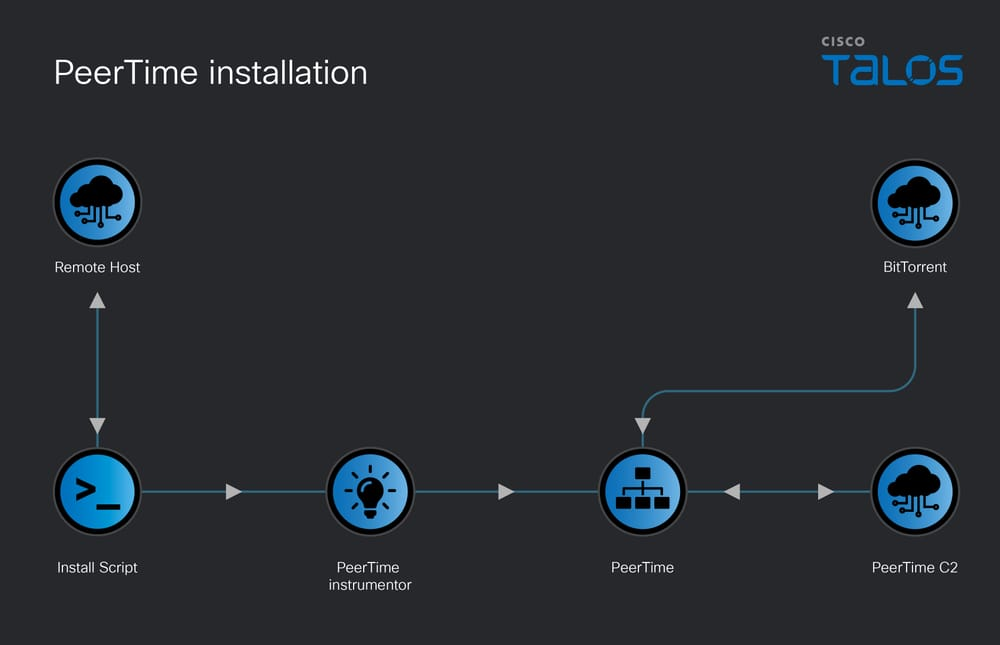
The second implant is “PeerTime,” an ELF-based backdoor designed specifically for Linux and embedded systems across various architectures, including ARM and MIPS.
Also tracked as “angrypeer,” PeerTime uniquely leverages the BitTorrent peer-to-peer protocol to communicate with its command and control (C2) servers.
It downloads additional payloads from infected peers and uses the BusyBox utility to copy them into place across the network.
The final tool in this campaign is “BruteEntry,” a GoLang-based brute-force scanner.
BruteEntry is typically installed on compromised network edge devices, effectively transforming them into Operational Relay Boxes (ORBs).
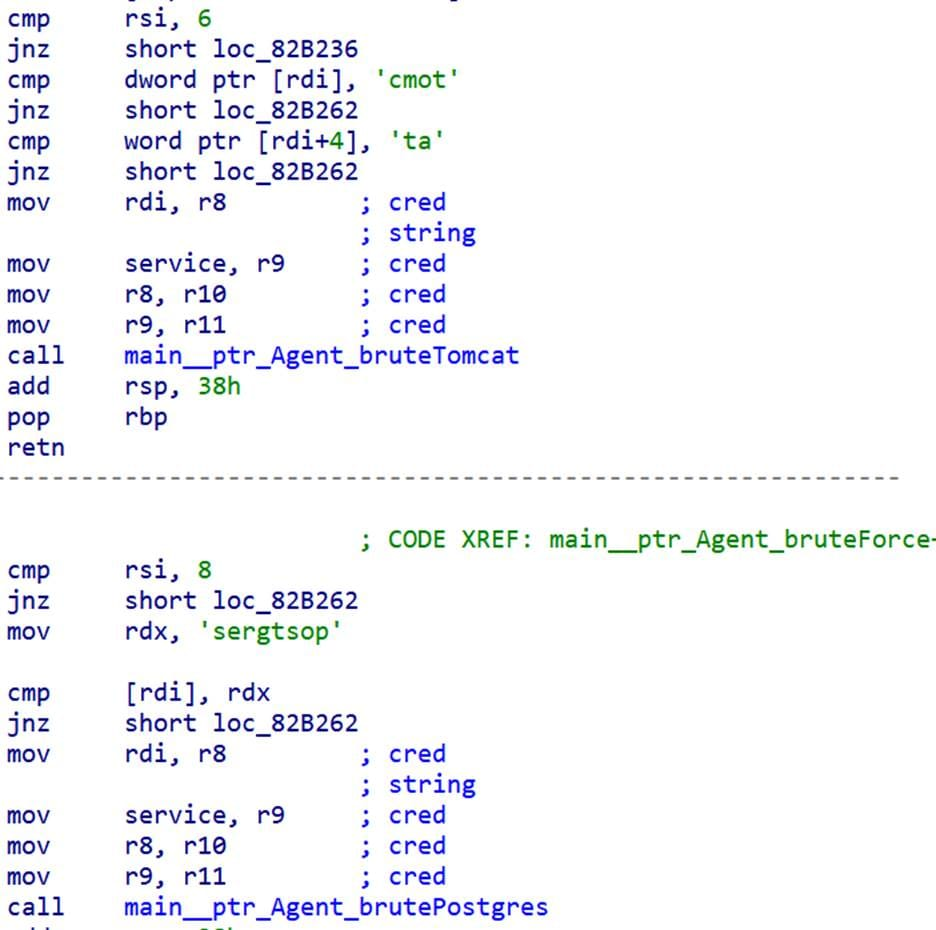
These proxy nodes receive target lists from the C2 server and perform mass automated scanning against SSH, Postgres, and Tomcat servers to breach further systems.
Technical Operations and Network Evasion
The threat actors use specific deployment mechanisms to ensure their malware remains hidden and persistent.
For Windows systems infected with TernDoor, UAT-9244 establishes persistence by creating hidden scheduled tasks or modifying Registry Run keys.
The malware creates an automated task using the following command:
textschtasks /create /tn WSPrint /tr "C:ProgramDataWSPrintWSPrint.exe" /ru "SYSTEM" /sc onstart /F
On Linux environments, the attackers use custom shell scripts containing simplified Chinese debug strings to deploy PeerTime.
The malware specifically checks for the presence of container environments and executes the loader through Docker if available:
bashdocker
For the BruteEntry scanner, the malware registers the newly infected host with the C2 server, providing its IP address and hostname.
It then requests batches of up to 1,000 vulnerable IP addresses to attack. BruteEntry reports any successful intrusions back to the command server using a structured JSON format to confirm the compromised targets:
json{"batch":[
{"task_id": 12345, "success": true, "note": "Cracked by agent | Version v1.0"}
]}
By combining the Windows-focused TernDoor backdoor, the BitTorrent-driven PeerTime network, and the mass-scanning proxy capabilities of BruteEntry, UAT-9244 has built a highly effective and stealthy infrastructure for compromising telecommunication environments.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.