Beyond CVE, China’s dual vulnerability databases, CNVD and CNNVD, show that vulnerability disclosure is not a single, global, unified process but a set of parallel systems with different rules, incentives, and timelines.
China runs two national vulnerability databases: CNNVD, operated under the Ministry of State Security, and CNVD, operated by CNCERT as a defender‑focused coordination platform.
While both catalog software and hardware flaws use their own IDs, schemas, and categorizations instead of fully adopting Western standards such as CWE and CPE.
CNNVD closely shadows CVE and NVD and historically has contained slightly more entries than US‑maintained datasets over certain time ranges, while CNVD is smaller and more uneven in its coverage.
Both systems include a CVE field, but they do not systematically cross‑reference each other, which complicates correlation and automation work for defenders.
China also regulates vulnerability handling via the “Provisions on the Management of Network Product Security Vulnerabilities” issued in July 2021 and in force since September 2021.
The regulation forces vendors and operators to report vulnerabilities to authorities, patch them promptly, and retain logs, while imposing conditions on public disclosure.
Both CNNVD and CNVD require account creation, email verification, and logins to access data.

It explicitly restricts publishing exploit code, forbids exaggerating severity, and requires coordination with state agencies, a sharp contrast to the more voluntary, researcher‑led disclosure norms common around CVE and NVD.
China’s Parallel CVE Systems
While XML is not my preferred document based data format, it can be parsed like any other. However, errors in the entries in both databases mean that simply asking your favorite XML engine to parse the data.
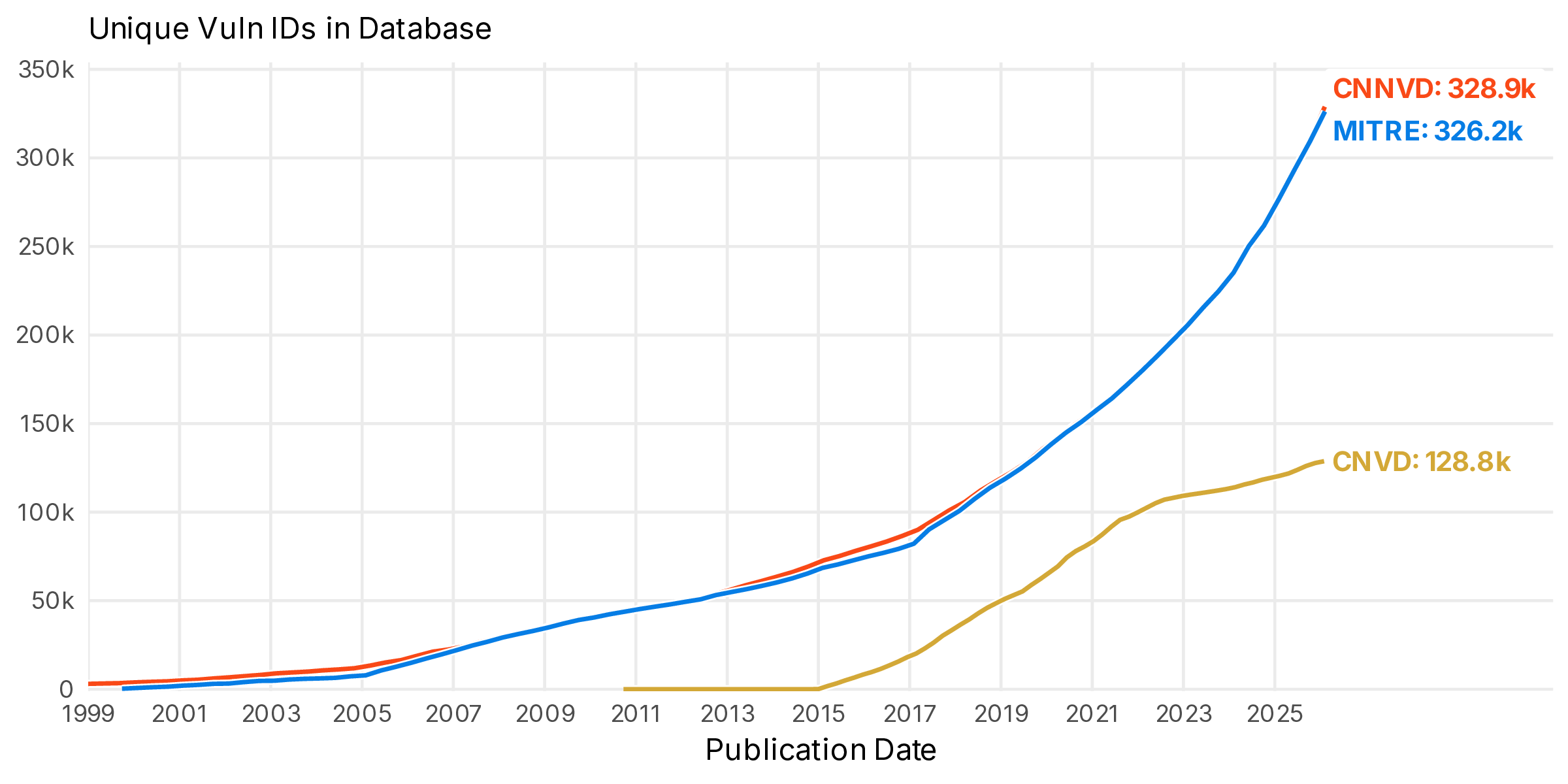
Studies comparing the databases show that CNNVD has only a relatively small subset of entries without a CVE mapping, on the order of ten thousand out of well over a hundred thousand total vulnerabilities.
Where CVE and NVD provide richer structured data CVSS, CWE, and more mature affected‑product modeling the Chinese databases tend to provide simpler categorical severity and free‑text descriptions.
Under the surface, however, a small but important set of vulnerabilities appears in CNNVD and CNVD well before they are recorded as published in CVE or NVD, sometimes by several months.
There are two other structured and easily analyzable fields in CNVD: the open and submission times. These are, presumably, when the vulnerability was first submitted to the database and when it was finally published.
In a few cases, researchers have identified Chinese entries that either never gained a corresponding public CVE or that relate to products and vendors with little presence in Western markets, suggesting that some exposures tracked in China remain under‑represented in Western datasets.
These quality problems, combined with manual web‑based exports modern APIs, make large‑scale ingestion and correlation harder than with NVD, even when the underlying vulnerability set is similar.
What 2026 Might Look Like
The 2021 Chinese regulations have influenced what gets published and when, especially around entries that lack CVE mappings.
At the same time, hygiene issues are visible on the Chinese side as well. Analyses report malformed or mismatched CVE identifiers, inconsistent dates, and missing or misaligned severity scores in CNVD and CNNVD feeds.
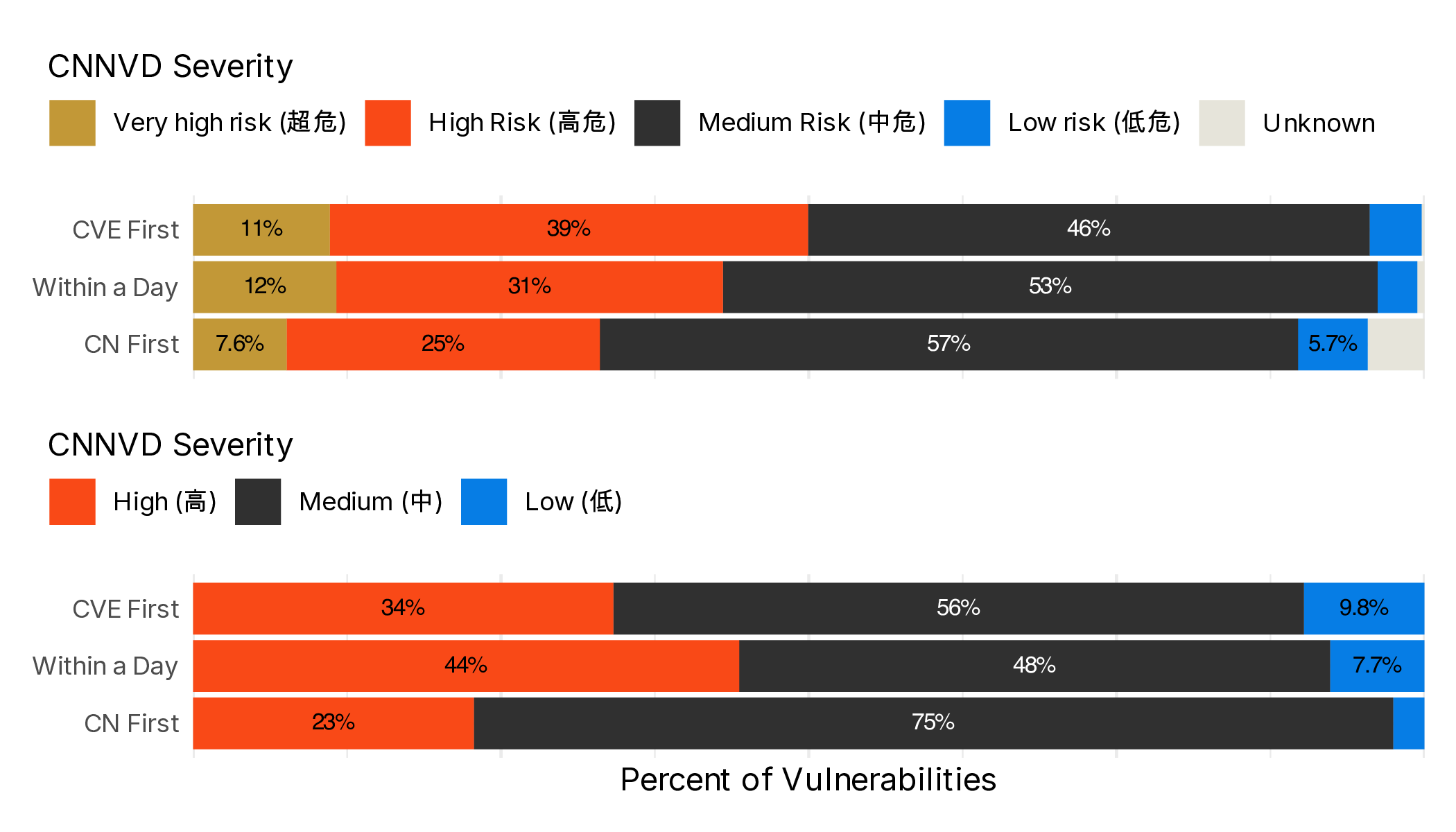
Researchers have observed shifts in the rate at which non‑CVE vulnerabilities are exposed in CNVD and CNNVD around and after the policy date, with some evidence that CNNVD in particular slowed publication of non‑mapped vulnerabilities for a period before increasing output again more recently.
This pattern is consistent with a tightening of state control over what vulnerability information becomes public, and when, rather than a purely organic evolution of a community‑driven database.
For defenders and analysts heading into 2026, the lesson is twofold. First, relying solely on CVE and NVD risks missing context, timing differences, and region‑specific exposures that show up first or only in foreign national databases such as CNNVD and CNVD.
Second, despite recent strains on the NVD and the CVE program standardized , Western infrastructure still offers more machine‑readable, and transparent data than what is officially exposed from China, especially around CVSS, CWE, and derived frameworks like KEV lists and probabilistic exploit scoring.
In a world of competing disclosure regimes, the real advantage goes to teams that can fuse these disparate feeds, normalize their quirks, and reason about the gaps between them.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.






