A long-running Chrome extension malware campaign has silently hijacked more than 500,000 VKontakte (VK) accounts, forcing users into attacker-controlled groups, resetting their settings every 30 days, and abusing VK’s own infrastructure as command-and-control.
What appeared to be harmless VK customization tools were in reality a tightly maintained malware project operated by a single threat actor using the GitHub.
The investigation began when a browser risk engine detected a Chrome extension injecting Yandex display ad scripts into every page, a behavior commonly associated with monetization but not necessarily indicative of a full compromise.
Pivoting on the same Yandex display framework and tracking code led researchers to an extension called “VK Styles Themes for vk.com,” boasting around 400,000 installations and positive reviews while claiming to enhance VK’s user interface simply.
Inside the extension, analysts found a dynamically computed Yandex metric ID: ‘R-A-‘ + 843079 * 2, which evaluates to R-A-1686158, a trick used to evade static string-based detection by scanners and store reviewers.
This ID became the key to mapping a broader network of five related extensions, together reaching approximately 502,000 installations, two of which have since been removed from the Chrome Web Store.
One of the most popular entries in this network, VK Styles, was removed on February 6 after the activity came to light.
Running deeper analysis on the VK Styles codebase, researchers uncovered a multi-stage architecture.
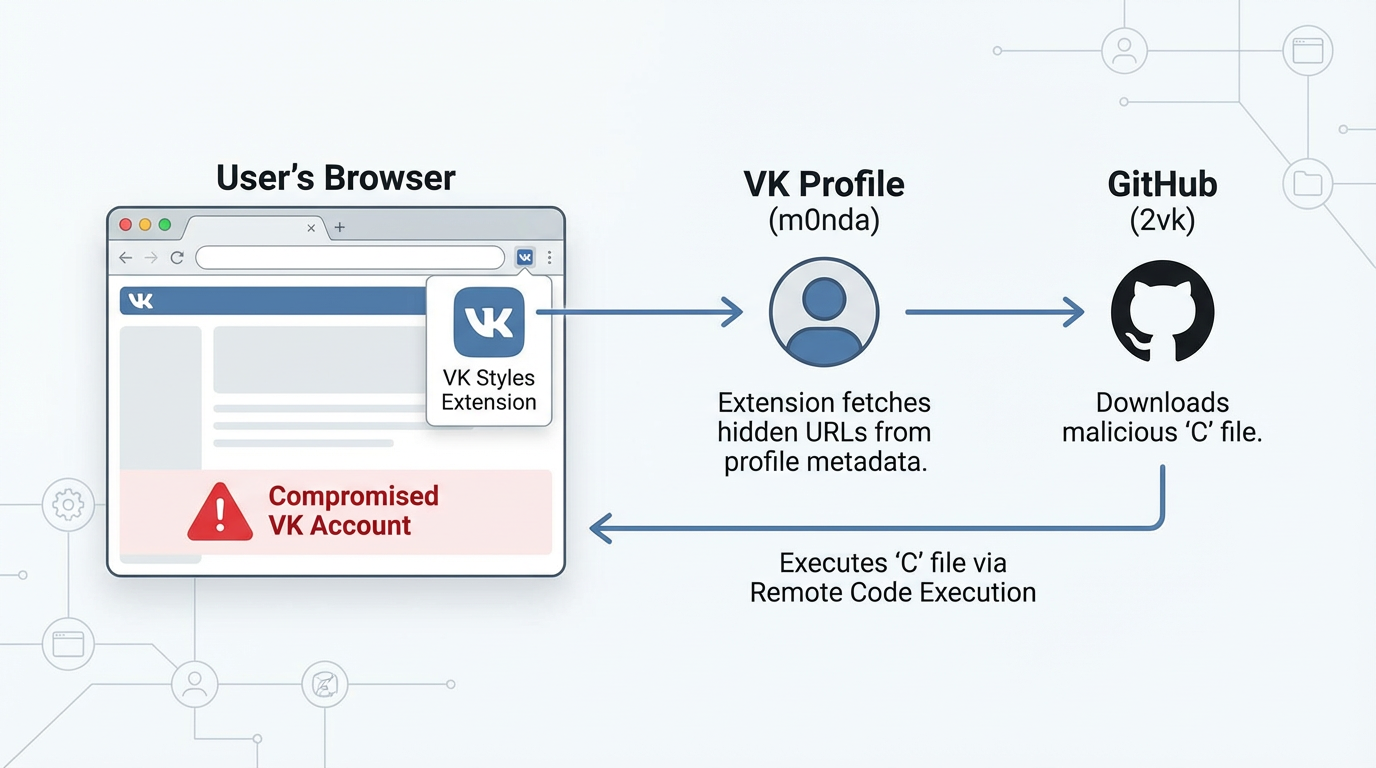
Two seemingly innocuous code fragments allowed arbitrary strings to be executed, and a call chain eventually pointed to a VK profile at vk.com/m0nda, which the extension used as a covert control hub.

By pulling and executing data from that profile, the extension effectively turned a normal social account into live C2 infrastructure.
Chrome Extension Malware Attack
The attacker hid the next-stage configuration inside HTML meta tags on the VK profile, including an encoded description field such as: 4000 :: G2vk.github.io/-/ V1.0.250.69 Yan.yandex.ru/system/context.js Ayastatic.net/partner-code-bundles/ :.
Decoding this reveals three key endpoints: a GitHub Pages site at https://2vk.github.io/-/, a Yandex advertising script, and additional ad-bundle hosting at Yandex’s static infrastructure, along with a version marker.
This design means the extension never hardcodes URLs; instead, it fetches the VK profile, parses the meta tags, and then downloads the next-stage payload from GitHub, giving the attacker flexible, profile-driven configuration that is difficult to block without disrupting legitimate VK traffic.
On GitHub, under the account “2vk,” the repository named “-” hosts a JavaScript file simply called C, which holds the core obfuscated payload injected into every VK page visited by victims.
Koi’s research noted this campaign, active since at least June 2025 and still evolving as of January 2026, highlights how browser extensions, social networks, and developer platforms can be chained into resilient malware supply chains.
Commit history from June 2025 through January 2026 shows deliberate evolution: initial versions established CSRF cookie manipulation and basic VK API wrappers, later updates introduced auto-subscription logic with a 75% probability per session, a 30‑day configuration reset cycle, and eventually donation tracking via the VK Donut API feature gating based on payment status.
Exposing the 500K User Breach
Recent commits focus on reducing detection surface, including removing more than 100 lines of IntersectionObserver code and refining selectors while continuing version bumps.
Functionally, the malware performs five main categories of malicious behavior once fully deployed.
First, it auto-subscribes users to VK group -168874636, which redirects to the VK Styles community (vk.com/2style), using a 3-in-4 probability every time a victim visits VK, turning compromised accounts into a growth engine for the attacker’s own group that now boasts over 1.4 million followers.
With high privileges, silent auto-updates, and limited marketplace vetting, malicious extensions like VK Styles can quietly transform normal social accounts into C2 servers and everyday users into unwitting distribution nodes.
Second, it enforces a 30‑day reset mechanism that changes feed sorting, forces a default message theme, and overwrites user preferences, ensuring continued control even if victims attempt to fix settings.
Third, the code manipulates VK’s CSRF protection cookie remixsec_redir, undermining a core security control designed to validate sensitive actions and making extension-driven requests appear legitimate to VK’s backend.
Fourth, the malware tracks donation status via VK Donut, selectively unlocking or restricting features based on whether the victim has paid, effectively turning hijacked accounts into a monetization channel rather than simply a botnet.
Finally, the multi-stage architecture, driven by VK profile metadata and GitHub-hosted payloads, allows the attacker to update behavior in real time without changing the extension package itself; auto-updating extensions then propagate new malicious logic instantly to more than half a million users.
IOCs
| Extension ID | Install Count |
|---|---|
| ceibjdigmfbbgcpkkdpmjokkokklodmc | 400,000 |
| mflibpdjoodmoppignjhciadahapkoch | 80,000 |
| lgakkahjfibfgmacigibnhcgepajgfdb | 20,000 |
| bndkfmmbidllaiccmpnbdonijmicaafn | 2,000 |
| pcdgkgbadeggbnodegejccjffnoakcoh | 2,000 |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.






