CISA issued this year’s first emergency directive ordering Federal Civilian Executive Branch (FCEB) agencies to immediately mitigate two Ivanti Connect Secure and Ivanti Policy Secure zero-day flaws in response to widespread and active exploitation by multiple threat actors.
This is an expected development, given that vulnerable Ivanti appliances are now targeted in extensive attacks chaining the CVE-2023-46805 authentication bypass and the CVE-2024-21887 command injection vulnerabilities since December, and the vendor has yet to release security patches.
“CISA has determined these conditions pose an unacceptable risk to Federal Civilian Executive Branch (FCEB) agencies and require emergency action,” the cybersecurity agency said on Friday.
“This determination is based on widespread exploitation of vulnerabilities by multiple threat actors, the prevalence of the affected products in the federal enterprise, the high potential for a compromise of agency information systems, the impact of a successful compromise, and the complexity of the proposed mitigations.”
ED 24-01 required actions
As instructed by emergency directive ED 24-01, federal agencies now must promptly implement Ivanti’s publicly disclosed mitigation measures to block attack attempts.
The agencies are also required to use Ivanti’s External Integrity Checker Tool and:
- Immediately report indications of compromise to CISA through central@cisa.dhs.gov
- Remove compromised products from agency networks. Initiate incident analysis, preserve data from the compromised devices through the creation of forensic hard drive images, and hunt for indications of further compromise.
- Bring a compromised product back into service, reset the device with the affected Ivanti solution software to factory default settings and remove the attack vector by applying Ivanti’s mitigations.
To fully restore impacted appliances and bring them back into service, they have to follow Ivanti’s recovery instructions and then:
- Revoke and reissue any stored certificates.
- Reset the admin enable password.
- Reset stored API keys.
- Reset the password of any local user defined on the gateway, including service accounts used for auth server configuration(s).
- Apply updates that address the two vulnerabilities referenced in this Directive to the affected products as they become available and no later than 48 hours following their release by Ivanti.
- One week after the issuance of this Directive, report to CISA (using the provided template) a complete inventory of all instances of Ivanti Connect Secure and Ivanti Policy Secure products on agency networks, including details on actions taken and results.
Threat monitoring service Shadowserver currently tracks more than 16,200 ICS VPN appliances exposed online, over 4,700 in the United States (Shodan also sees almost 17,000 Internet-exposed Ivanti ICS devices).
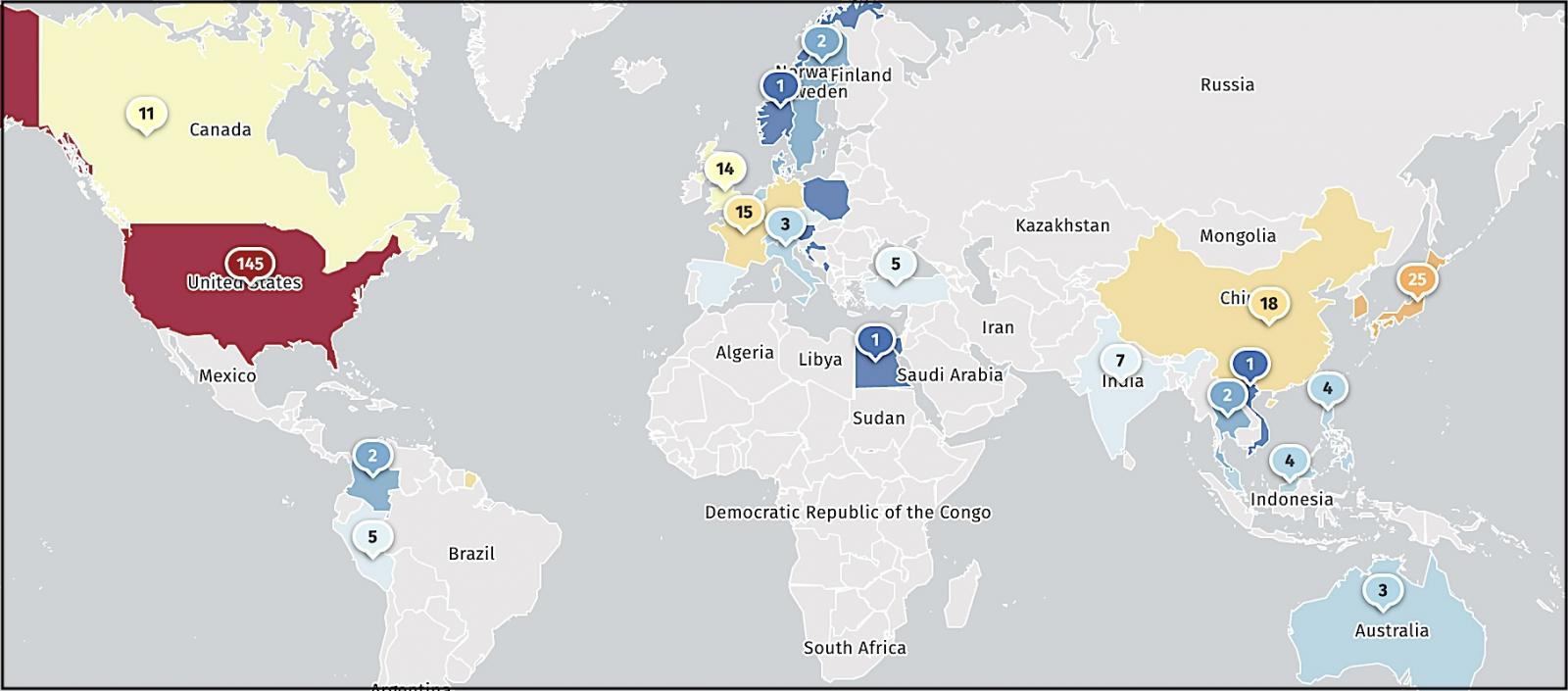
Shadowserver is also monitoring the number of compromised Ivanti Connect Secure VPN instances worldwide, with more than 420 hacked devices spotted on January 18.
Actively exploited to drop crypto-miners, malware
Threat intelligence company Volexity says that one of the attackers (a suspected Chinese state-backed threat actor tracked as UTA0178 and UNC5221) has already backdoored over 2,100 Ivanti appliances using a GIFTEDVISITOR webshell variant.
Mandiant found five custom malware strains deployed on breached customers’ systems with the end goal of stealing credentials, deploying webshells, and additional malicious payloads.
The threat actor has been harvesting and stealing account and session data and more info from compromised networks.
Victims discovered so far include government and military departments worldwide, national telecom companies, defense contractors, technology companies, banking, finance, and accounting organizations, worldwide consulting outfits, and aerospace, aviation, and engineering firms.
They vary greatly in size and range from small businesses to some of the largest organizations worldwide, including multiple Fortune 500 companies from various industry sectors.
Attackers have also been seen by Volexity and GreyNoise deploying XMRig cryptocurrency miners and Rust-based malware payloads still waiting for analysis.






