Hackers are abusing ClickFix commands and booby-trapping DMG installers to deliver a new macOS stealer called notnullOSX, built to loot high-value crypto wallets from Mac users.
The story starts with 0xFFF, a malware developer who abruptly quit a major Russian-speaking hacking forum in 2023 after claiming he was being investigated and accusing the forum of cooperating with law enforcement.
The promise was simple and ruthless: a hand-targeted stealer focused on macOS users with crypto holdings above 10,000 USD.
In August 2024, he resurfaced under the alias alh1mik, posting an apology on Telegram and offering a new, exclusive macOS stealer to regain his status.
By early 2026, that offer became reality as notnullOSX, a Go-based modular implant distributed through custom lures, a gated affiliate panel, and a dedicated operator ecosystem.
Initial lure: fake protected Google Docs
The notnullOSX infection flow begins with a fake “protected” Google document reported by researcher @g0njxa on X.
Victims see an error claiming that encryption failed due to an outdated “Google API Connector,” and they are presented with two ways to “fix” it both leading to the same malware.
Operators don’t cast a wide net: before a lure is generated, they submit a target profile in an affiliate panel that includes social media links, past communication, the crypto wallet address, and where it was found.
The panel explicitly enforces a minimum threshold wallets under 10,000 USD are rejected, keeping the campaign focused on high-value victims.
The campaign runs two parallel social-engineering chains that converge on the same implant.
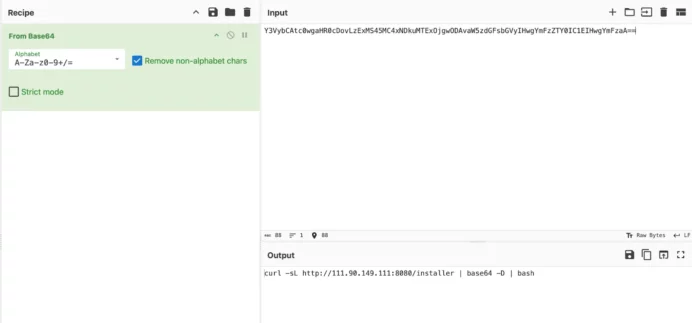
- ClickFix chain: The victim is told to open Terminal and paste a base64-encoded command that silently pulls a bash installer from attacker infrastructure.
The script downloads a Mach-O payload, removes Gatekeeper’s quarantine flag, hides it inside a minimal .app bundle, and adds a LaunchAgent for persistence.
The user is then guided step-by-step to grant the fake app Full Disk Access in System Settings, effectively handing it broad TCC-gated access to Messages, Notes, Safari data, and more without further prompts.
- DMG chain: A malicious disk image instead shows a Finder window with Install.sh, README.txt, and a Terminal alias.
Opening the alias launches Terminal from the mounted DMG, while the README instructs the user to run the base64-encoded “installer” script, which decodes to the same infection logic as the ClickFix path.
In both cases, there is no exploit; the victim is persuaded to run and authorize the malware themselves, bypassing many traditional detection points.
WallSpace disguise and YouTube traffic
Moonlock Lab observed notnullOSX being distributed under the name WallSpace.app, imitating a legitimate macOS live wallpaper application.
The download path tells a different story. Navigating to wallpapermacos[.]com/download/ triggers a Cloudflare malware warning.
![Cloudflare flags wallpapermacos[.]com/download/ as suspected malware (Source : moonlock).](https://moonlock.com/2026/04/Warning-on-wallpapermacos-679x464.webp)
A polished website at wallpapermacos[.]com advertised free live wallpapers and guided visitors to a “Download Free” flow, while the download path triggered security warnings and malware flags during investigation.
A second domain, wallspaceapp[.]com, remained live and even ranked at the top of Google Search results for WallSpace-related queries, hosting a classic ClickFix page with a base64 command, copy button, and numbered Terminal instructions.
Traffic was funneled from a seemingly benign YouTube channel created in 2015 but recently repurposed to host a single WallSpace video that rapidly accumulated tens of thousands of views, a pattern consistent with a hijacked and boosted channel used as a distribution funnel.

The main notnullOSX payload is a large, multi-architecture Mach-O binary that only a minority of antivirus engines currently flag, often with misleading labels like “adware” or “potentially unwanted.”
Once installed and granted Full Disk Access, it operates as a modular stealer: individual components are downloaded from a legitimate CDN, staged in /tmp, and executed to harvest specific data categories.
Confirmed modules include SystemInfo, iMessageGrab, AppleNotesGrab, SafariCookiesGrab, CryptoWalletsGrab, BrowserHistoryGrab, BrowserGrab, FirefoxGrab, CredsGrab, TelegramGrab, and ReplaceApp, covering everything from chat history and browser cookies to crypto wallets, SSH keys, cloud credentials, and Telegram sessions.
A standout feature, ReplaceApp, is designed to swap legitimate applications potentially hardware wallet managers with trojanized clones while preserving the original icon, enabling theft of seed phrases during setup.
Unlike typical smash-and-grab stealers, notnullOSX maintains a persistent, TLS-encrypted WebSocket-like channel to its command-and-control via Firebase Realtime Database, using server-sent events for inbound commands and JSON posts for outbound results.
Moonlock Lab telemetry recorded first in-the-wild detections of notnullOSX on March 30, 2026, affecting users in Vietnam, Taiwan, and Spain, confirming that the campaign is active rather than theoretical.
For defenders, this case underscores three critical points: socially engineered Terminal commands are now a mainstream delivery technique on macOS, Full Disk Access prompts must be treated as high-risk events, and high-value crypto users remain prime targets for sophisticated, modular stealers with long-term roadmaps.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.