The Clop ransomware gang is expected to earn between $75-100 million from extorting victims of their massive MOVEit data theft campaign.
In a new report released today, Coveware explains that the number of victims paying ransoms has fallen to a record low of 34%, causing ransomware gangs to switch strategies to make their attacks more profitable.
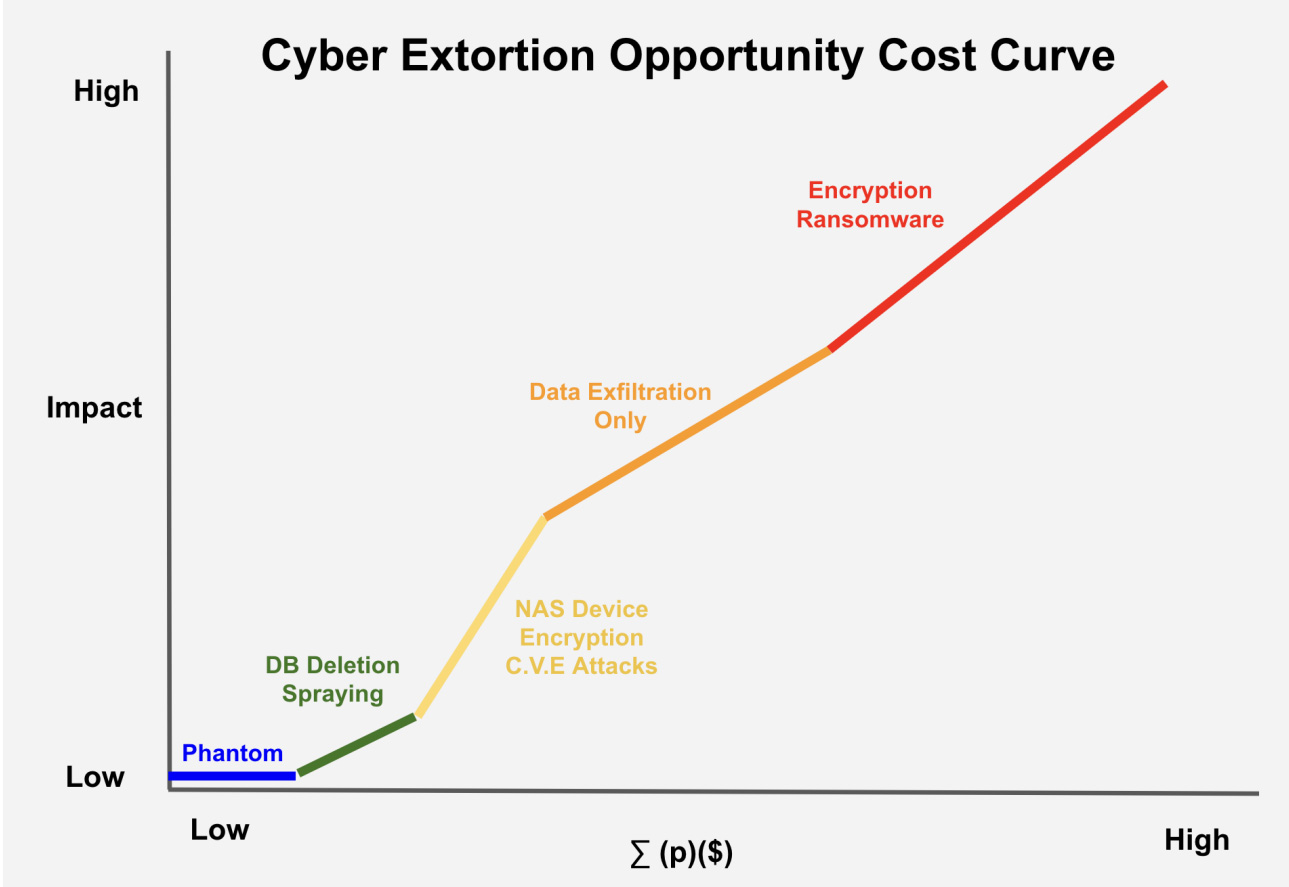
Coveware explains that different extortion attacks have varying opportunity costs reflected by the amount of effort and investments required to conduct an attack compared to the expected ransom demand.
The relationship between the impact on a victim and the threat actor’s costs (time, effort, and investment) to conduct the attack is depicted in the chart below. The vertical axis represents the impact on the victim, while the horizontal axis illustrates the threat actor’s costs.
Source: BleepingComputer
The chart shows that extortion attacks with the lowest complexity and automation have the least impact on victims and cost to the attackers.
This is reflected in the ransom demands, with phantom attacks (social engineering), DB wiping with ransoms, and NAS encryption attacks like Qlocker, having generally low ransom demands due to automation and lack of complexity in the attacks.
For attacks like these, the ransom demands typically range between a few hundred dollars to thousands of dollars, with the threat actors hoping that a large volume of payments will make up for the low ransom prices.
However, more complicated and time-consuming attacks with more significant impact generate far greater ransom demands, usually in the millions.
Clop changes tactics as payments drop
On May 27th, the Clop ransomware gang began widespread data-theft attacks exploiting a zero-day vulnerability in the MOVEit Transfer secure file transfer platform.
These attacks are expected to impact hundreds of companies worldwide, with many having already notified their affected customers over the past two months.
However, Coveware says that extortion attacks focusing only on data theft have decreased payments over time, with victims rather disclosing the attacks and issuing data breach notifications than paying the threat actors.
“DXF-only attacks do not cause material business disruption like encryption impact but can cause brand damage and create notice obligations,” explains Coveware’s report.
“The probability of a ransom being paid is less than 50%, but the ($) of a ransom demand on DXF only attacks is relatively high.”
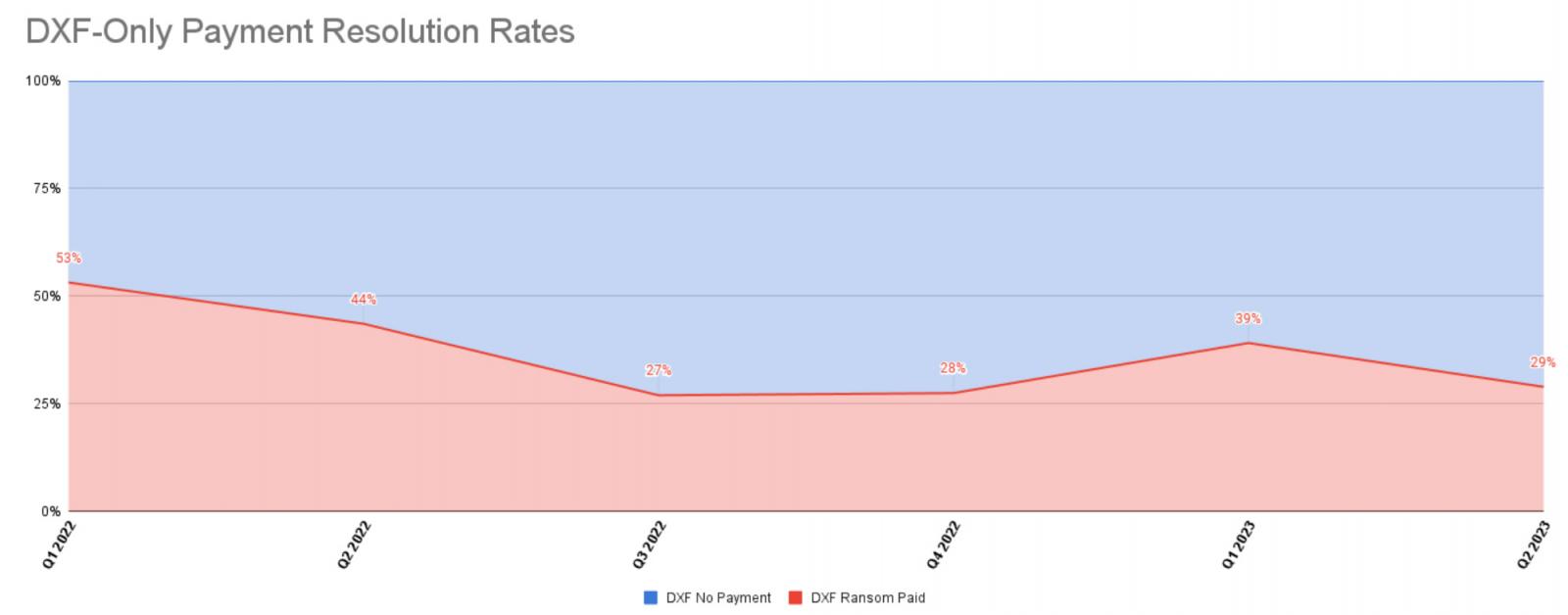
Source: Coveware
Coveware says that Clop has changed its extortion strategy by demanding far more significant ransom demands than previously seen in data exfiltration attacks, hoping that a few large payments will overcome the overall decline.
According to Coveware’s estimation, only a few MOVEit data-theft victims are likely to pay. Nevertheless, Clop is still expected to amass an impressive $75-100 million solely from these payments, given the substantial ransom demands.
“It is likely that the CloP group may earn $75-100 million dollars just from the MOVEit campaign, with that sum coming from just a small handful of victims that succumbed to very high payments,” explains Coveware.
“This is a dangerous and staggering sum of money for one, relatively small group to possess.”
Coveware CEO Bill Siegel told BleepingComputer that Clop’s success in these attacks is significantly greater than their recent GoAnywhere data theft attacks, where the threat actors only breached 130 victims and received only a few ransom payments.
Siegel believes that Clop’s 2021 Accellion FTA data-theft attacks were successful because victims were not as well educated on the pros and cons of paying to prevent the leak of data. Furthermore, there was a lot more media attention on individual breaches in 2021, with the media now becoming numb to these types of attacks.
“Today, victims are much better educated on the pros and cons of these situations (with the cons very clearly outweighing the pros in most situations),” Siegel told BleepingComputer.
“So while Accellion was a pretty big financial success as a higher % of victims paid out of a pretty small pool of victims, GoAnywhere seemed to be an almost total flop out of another small pool of victims.”
“MOVEit had at least 10x more direct victims than both of these attacks, so CloP was able to focus on just the very largest and most likely to consider paying, even with well over 90% victims not even bothering to engage in a negotiation, let alone paying.”
Ransomware affiliates shift to new operations
In addition to the changing tactics of data-theft attacks, Coveware has also seen a shift when it comes to ransomware encryption attacks.
Coveware says there has been a dramatic reduction in Ransomware-as-a-Service operations targeting small enterprises, as getting ransom payments has become much more challenging.
As a result, smaller ransomware operations such as Dharma and Phobos have seen a decrease of nearly 37% in attacks in 2023.
Instead, Coveware has observed a shift among more affiliates within these groups, as they transition to the new 8base ransomware operation which uses the Phobos encryptor to target enterprises in larger-scale attacks.
A recent VMware report linked 8base to RansomHouse, a ransomware operation known for targeting larger organizations and allowing affiliates to demand bigger ransoms.