Cloud Hacking: Web3.0 Approach

Source link
Related Articles
All Mix →Companies Are Just a Graph of Algorithms
Table of Contents Transparency is AI fuel Expect the consultants The transparency / optimization pitch Continuous optimization Transparency opens the door for optimization But my…
AI is a Gift to Transparency
Table of Contents Transparency applications Summary Notes We’re about to be able to collect—and ask questions of—any corpus of data Created/Updated: April 23, 2023 GPT-based…
PortSwigger at Black Hat & DEF CON 33
Table of Contents Las Vegas. August. Protocols are getting torn apart. HTTP/1.1 must die. New research and tooling to fight ongoing risk DEF CON Workshop:…
InsertScript: Multiple PDF Vulnerabilities – Text and Pictures on Steroids
/*UPDATE */ @irsdl brought two import links to my attention: 2010 formcalc: http://t.co/6OfGLa9Cu1 2013 XXE + SOP Bypass: http://t.co/VZMSVg3HtN It seems like Adobe knew about the SOP issue…
One More Thing to Check for SSO – Flickr ATO – Ron Chan
Table of Contents Main Takeaway Like this: Related I have something that is worth sharing when you are testing for SSO system. Hope you can…
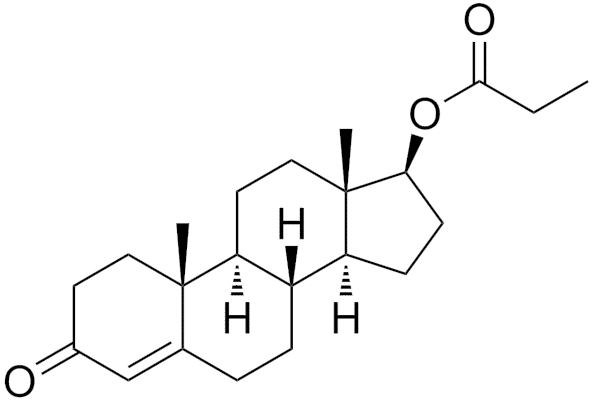
An Elegant Explanation for Why Famous Men Constantly Get Caught Cheating
Testosterone does two things to men: 1) it makes them horny, and 2) it makes them more likely to take risks. Famous people (politicians, athletes,…