Cloud Hacking: Web3.0 Approach

Source link
Related Articles
All Mix →Cloud Security Alliance Webinar Recap: Avoid the Breach with Shopify’s Andrew Dunbar
In this Cloud Security Alliance (CSA) fireside chat, Shopify’s VP of Security Engineering and IT sat down with HackerOne’s Luke Tucker to talk about how…
Scaling Security: From Startup to Unicorn
Building a small company’s security team is a unique challenge. Budgets are tight. Hiring is difficult. And security typically rests on the shoulders of one…
Remote Code execution at ws1.aholdusa.com — Compromising logins of Ahold Delhaize USA employees for >3.5 years (or even 18 years?) | by Jonathan Bouman | Dec, 2023
DiscussionUsually I put the discussion part of the report at the bottom of the write-up. But today it’s different. As this critical CVSS 10 bug…
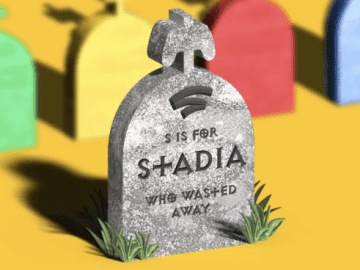
Stadia is Google’s Product Strategy
Google refuses to invest in solid product strategy and UI/UX, and the results are becoming predictable Created/Updated: October 2, 2022 Few things in tech were…
Hacker Herding – Bug Bounty Tips from Sky Betting & Gaming
UK-based Sky Betting & Gaming recently launched their own bug bounty program and shared some tips in a blog post: Hacker Herding – Ten Lessons…
The Security Vendors Startups like Lob Can’t Live Without
Source: https://twitter.com/arkadiyt/status/1144842849135079424 We love hearing that customers can’t live without us. Who doesn’t? It’s especially gratifying coming from a repeat customer like Arkadiy. Arkadiy’s…