A ransomware threat actor calling itself Coinbase Cartel has quickly become one to watch, not because it locks files, but because it often doesn’t.
First seen in September 2025, the group claimed 14 victims in that single month and later appeared in Bitdefender’s Top 10 ransomware groups for both September and December 2025.
Coinbase Cartel fits a broader shift Bitdefender and others have been tracking: data exfiltration-first extortion.
In these attacks, criminals steal sensitive data and then threaten to publish it unless the victim pays.
By skipping encryption, the operation can be quieter and faster, while still creating strong leverage: “Pay to keep your data private, or we leak it.” That tradecraft also reduces the obvious disruption that often triggers rapid incident response.
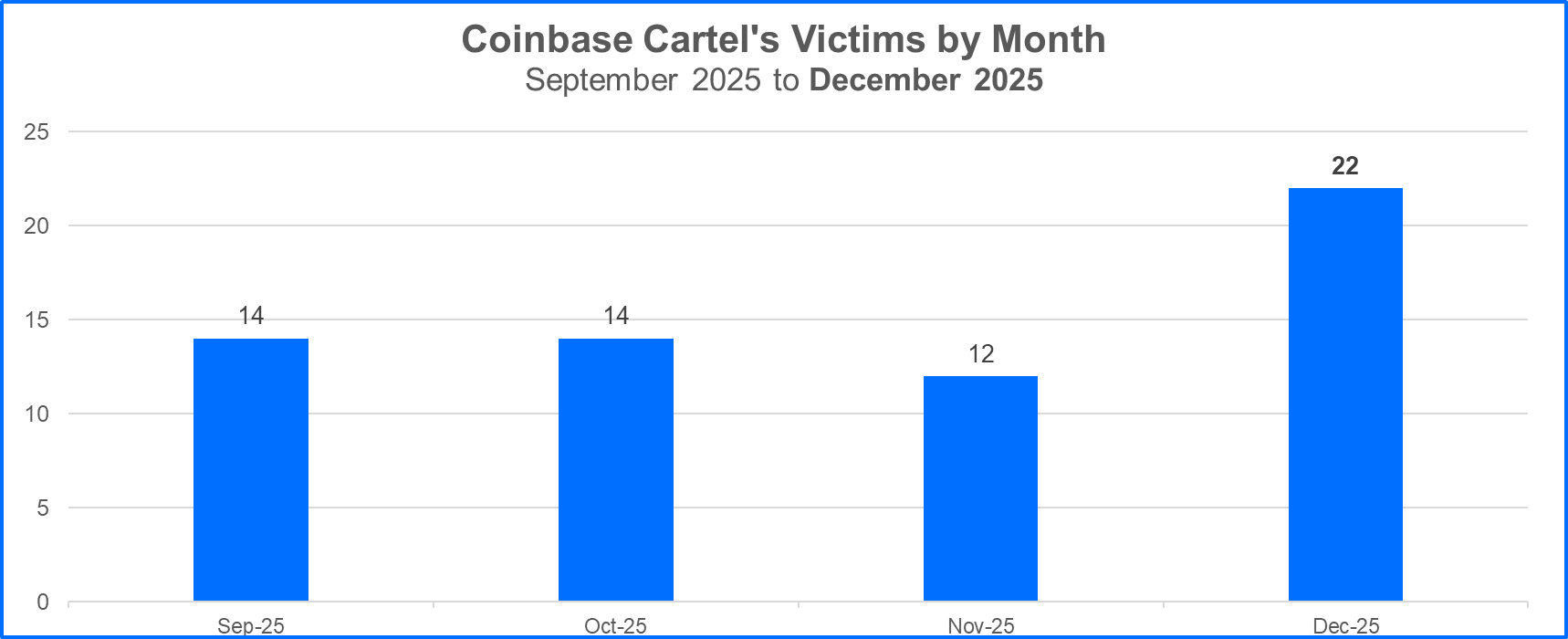
In just its first few months, Coinbase Cartel noted more than 60 victims, signaling a fast ramp-up and a clear focus on speed and pressure.
Victimology points to organizations with higher profit margins and bigger balance sheets. The group targets companies ranging from the “millions in revenue” tier to massive enterprises worth hundreds of billions of dollars.
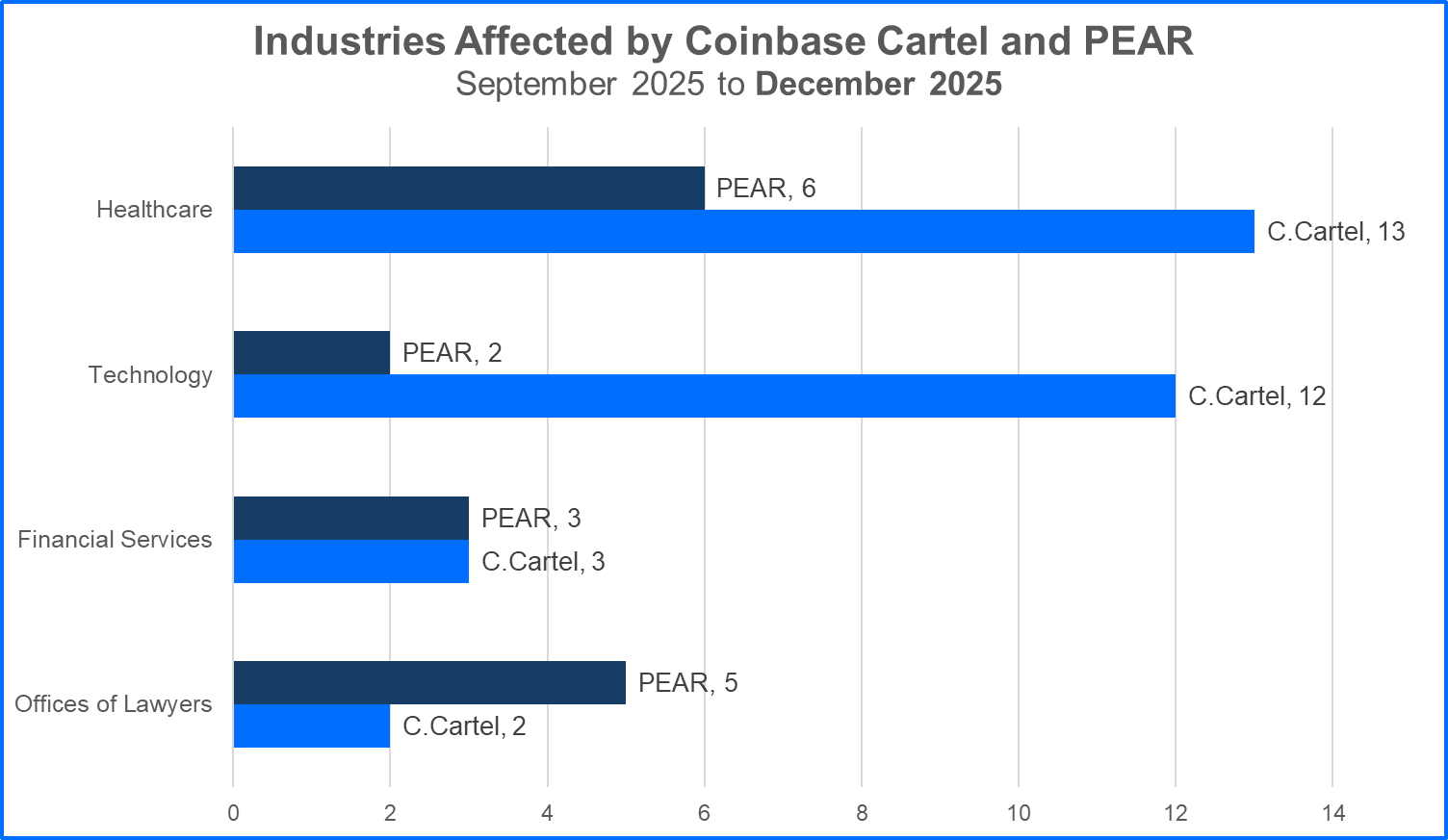
Healthcare, technology, and transportation account for the largest share of victims so far; together, they represented more than 50% of Coinbase Cartel’s 2025 victim claims, suggesting a preference for sectors where downtime, trust, and regulatory exposure increase the odds of payment.
New Data-First Extortion Model
One unusual pattern stands out: many impacted healthcare organizations were reportedly based in the United Arab Emirates, including a cluster of 10 healthcare victims claimed in a single month.
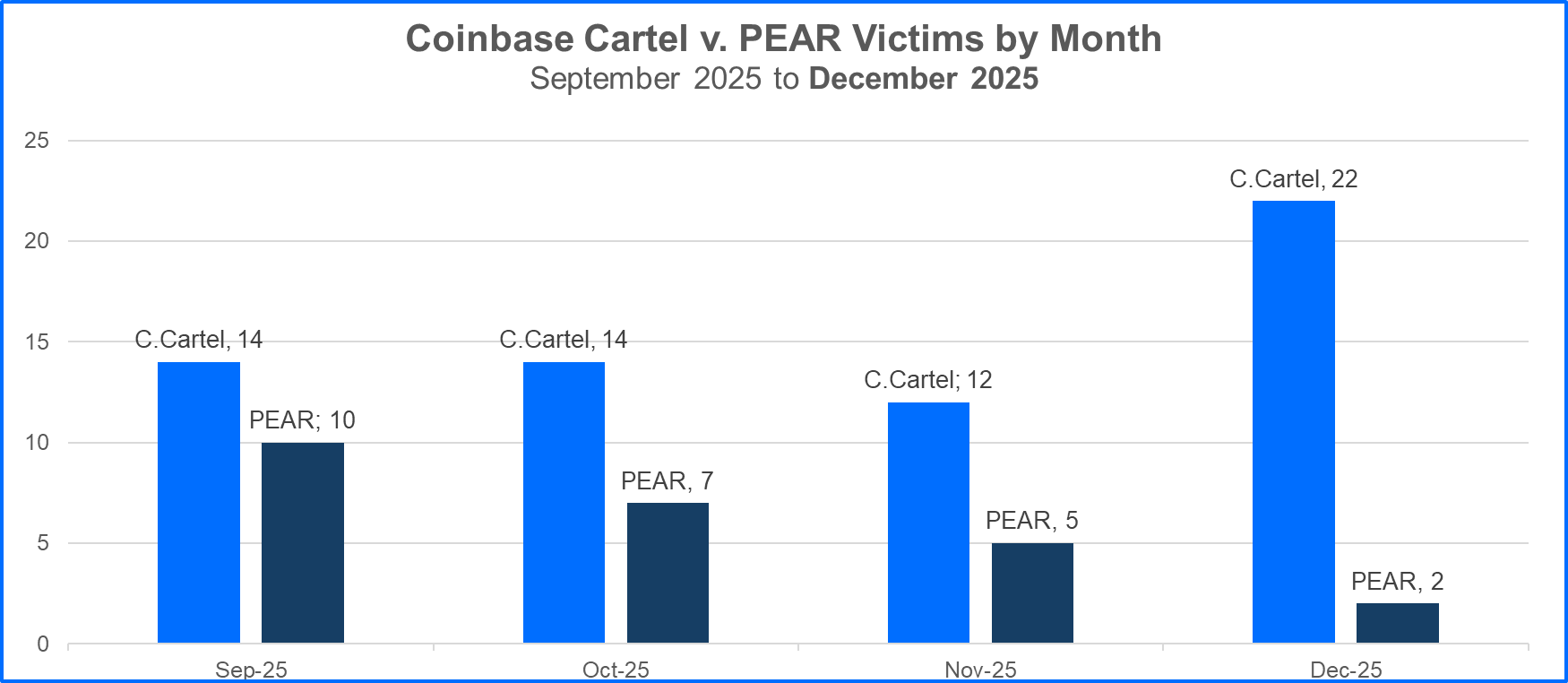
PEAR has avoided using encryptors and focused on data theft to drive ransom demands, much like Coinbase Cartel. And PEAR claimed more than 45 victims over the last half of 2025.
Healthcare data can include personally identifiable information and protected health information, which can enable identity fraud and cause serious reputational damage.
Still, that level of geographic concentration raises questions about whether motivations are strictly financial or influenced by geopolitics.
For initial access, Coinbase Cartel uses familiar pathways social engineering, help from initial access brokers, and stolen or exposed credentials.
Once inside, operators aim to obtain admin-level control, change system-wide settings, and tamper with logs to reduce detection.
The goal is to locate and exfiltrate valuable data efficiently. Example: a single compromised admin account can let attackers copy HR files, customer records, and contracts to external storage in hours, then exit before teams notice the pattern.
After exfiltration, the group posts victim names on a data leak site and initiates negotiation. Victims are told to respond within 48 hours through a designated chat interface, then have up to 10 days to pay or request changes to the demand. Payment is requested in Bitcoin.
The leak site includes pages such as HOME, AUCTIONS (apparently planned but not yet populated), PARTNERSHIPS, and CONTACTS an ecosystem built to monetize stolen data.
Mitigations
Coinbase Cartel also claims it is not operating a typical ransomware-as-a-service model, while still recruiting and collaborating.
In addition, when looking at the industries impacted by both Coinbase Cartel and PEAR, Coinbase Cartel’s breaches have affected a wider range of industries (17 in total compared to PEAR’s 13).
In one underground post, the group sought exploitation development services, including zero-day exploits, citing a budget exceeding $2 million.
Some researchers have hypothesized a possible connection to ShinyHunters, but no definitive link has been validated.
Despite branding itself a “cartel,” there is no clear evidence it exerts sustained control over other groups in the way historical “ransomware cartels” have.
Defenders should treat this as a reminder that backups alone are not enough when the threat is exposure.
Prioritize MFA (especially for admin accounts), strict least privilege, fast patching, tested backups, data inventory and access auditing, threat intelligence, and MDR plus attack-surface reduction to catch living-off-the-land behavior early.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.