Threat actors are actively distributing the PureLog Stealer through a sophisticated, multi-stage attack campaign disguised as legal copyright violation notices.
This information-stealing malware is engineered to silently harvest sensitive data, including browser credentials, browser extensions, cryptocurrency wallets, and detailed system information.
The campaign selectively targets organizations within the healthcare, government, hospitality, and education sectors across Germany, Canada, the United States, and Australia.
Attackers utilize localized phishing emails and Google Ads malvertising infrastructure, matching the exact language of the targeted region to significantly increase the probability of successful user execution.
To combat this distribution method, security platforms have deployed specialized detection models that monitor suspicious executable downloads originating from URLs containing targeted advertising tracking parameters.
The Multi-Stage Infection Chain
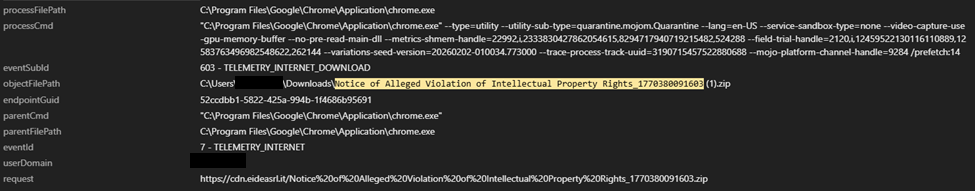
According to Trend Micro, the attack sequence initiates when a victim manually executes a malicious file disguised as a legal intellectual property document.
To avoid raising immediate suspicion, the malware immediately opens a benign decoy PDF file while the actual malicious operations execute silently in the background.
The malware then leverages the system command-line tool curl, utilizing a custom “curl/meow_meow” user-agent string, to download an encrypted payload that is deceptively disguised as an invoice PDF.
Instead of storing the decryption password locally within the initial executable, the malware dynamically retrieves this key from a remote command-and-control server.
This remote key retrieval tactic prevents security analysts from easily extracting the payload without active network access and allows operators to closely control payload access.
Once the password is successfully obtained, the malware extracts the encrypted payload using a renamed WinRAR application that masks itself as a standard PNG image file.
Advanced Evasion and Loader Capabilities
Following the initial extraction, the malware securely deletes the staging files and shifts its operations into a public Windows directory to mimic legitimate system behavior.
It subsequently executes a fileless Python loader. This loader is cleverly renamed as a standard Windows service host component and runs an obfuscated Python script deceptively labeled as a PDF instruction manual.
This Python loader possesses powerful capabilities strictly designed to bypass modern security measures.
It actively patches the Antimalware Scan Interface directly in memory to disable security scanning.
The loader establishes registry persistence under the current user to ensure the malware automatically runs upon every system login.
Additionally, it conducts thorough system fingerprinting by enumerating installed antivirus products and captures full-screen images of the desktop, constructing the image files entirely in memory before exfiltrating the gathered intelligence.
In its final deployment stage, the Python script concurrently launches two identical .NET loaders to provide built-in operational redundancy.
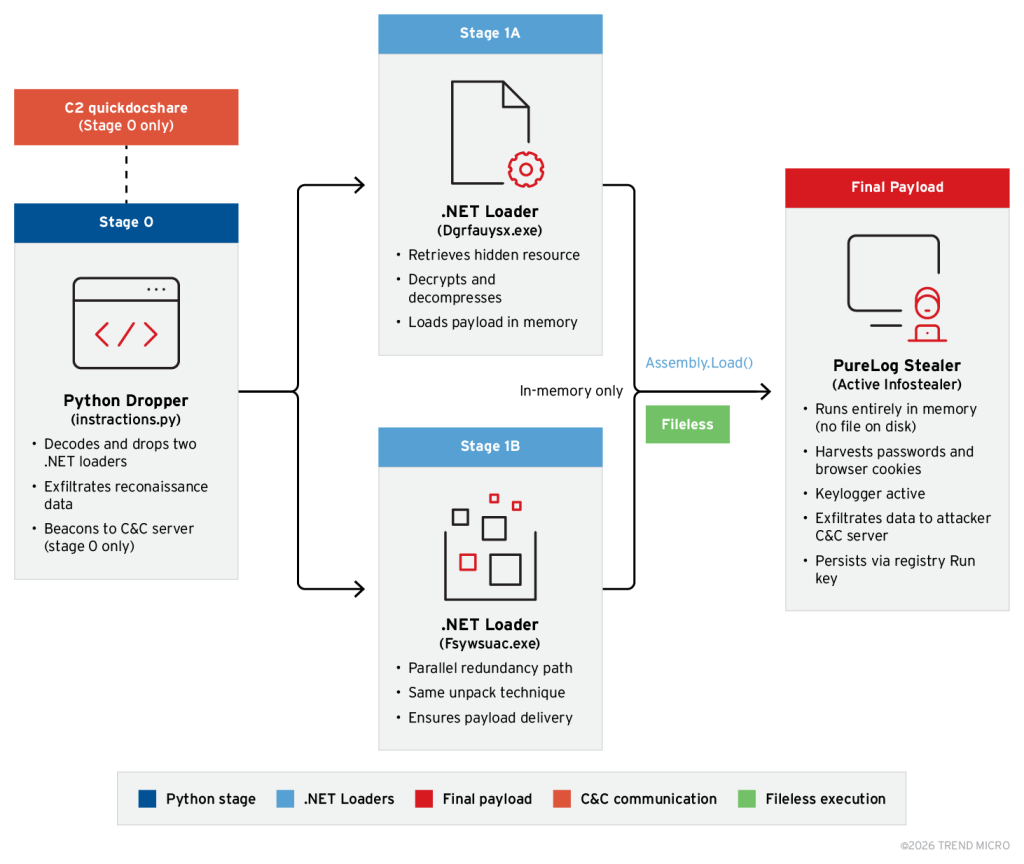
These distinct loaders are heavily protected by ConfuserEx, an advanced obfuscator that fragments the application control flow to deliberately hinder static analysis.
The loaders utilize Triple-DES encryption and GZip compression algorithms to successfully decrypt the ultimate payload.
The PureLog Stealer is then reflectively loaded directly into the system memory.
By executing completely within the managed memory heap and writing no operational files to the physical hard drive, the malware successfully evades traditional endpoint detection tools that monitor standard file creation events.
Indicators of Compromise (IOCs)
| Indicator Type | Value | Description |
|---|---|---|
| SHA-256 | 35efc4b75a1d70c38513b4dfe549da417aaa476bf7e9ebd00265aaa8c7295870 | Malicious ZIP Archive Lure |
| SHA-256 | 1539dab6099d860add8330bf2a008a4b6dc05c71f7b4439aebf431e034e5b6ff | Malicious Executable Lure |
| SHA-256 | ac591adea9a2305f9be6ae430996afd9b7432116f381b638014a0886a99c6287 | Shellcode Loader (urlmon.dll) |
| Domain | quickdocshare[.]com | Payload Hosting & Key Retrieval |
| Domain | logs[.]bestshopingday[.]com | PureLog Stealer C&C Infrastructure |
| IP Address | 166.0.184.127 | PureLog Stealer C&C Server |
| IP Address | 64.40.154.96 | Outbound Connection Target |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.





