Image: Midjourney
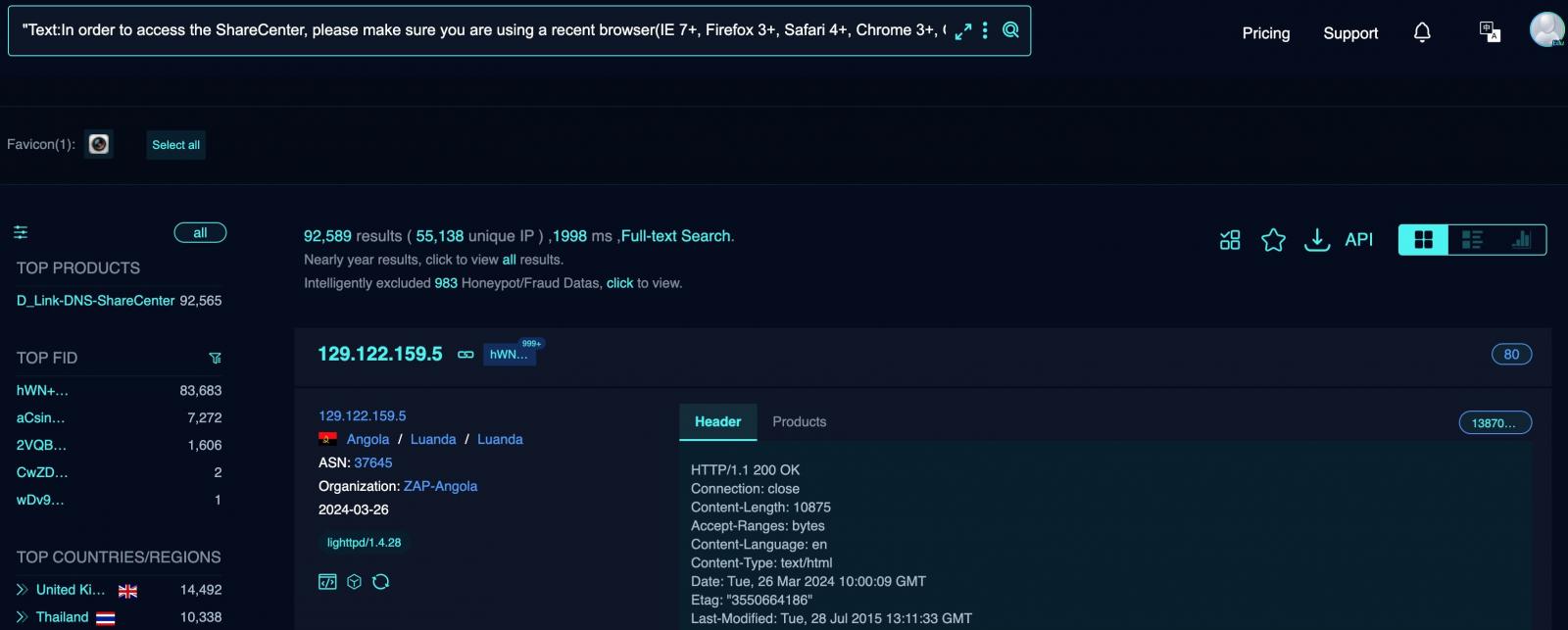
Attackers are now actively targeting over 92,000 end-of-life D-Link Network Attached Storage (NAS) devices exposed online and unpatched against a critical remote code execution (RCE) zero-day flaw.
As BleepingComputer first reported on Saturday, this security vulnerability (CVE-2024-3273) is the result of a backdoor facilitated through a hardcoded account (username “messagebus” with an empty password) and a command injection issue via the “system” parameter.
Threat actors are now chaining these two security flaws to deploy a variant of the Mirai malware (skid.x86). Mirai variants are usually designed to add infected devices to a botnet that can be used in large-scale distributed denial-of-service (DDoS) attacks.
These attacks started on Monday, as observed by cybersecurity firm GreyNoise and threat monitoring platform ShadowServer. Two weeks earlier, security researcher Netsecfish disclosed the vulnerability after D-Link informed them that these end-of-life devices would not be patched.
“The described vulnerability affects multiple D-Link NAS devices, including models DNS-340L, DNS-320L, DNS-327L, and DNS-325, among others,” Netsecfish explains.
“Successful exploitation of this vulnerability could allow an attacker to execute arbitrary commands on the system, potentially leading to unauthorized access to sensitive information, modification of system configurations, or denial of service conditions.”
When asked whether security updates would be released to patch this zero-day vulnerability, D-Link also told BleepingComputer that they no longer supported these end-of-life (EOL) NAS devices.
“All D-Link Network Attached storage has been End of Life and of Service Life for many years [and] the resources associated with these products have ceased their development and are no longer supported,” a D-Linkspokesperson told BleepingComputer.
“D-Link recommends retiring these products and replacing them with products that receive firmware updates.”
| Model | End of Service Life | Fixed Firmware | Conclusion |
| DNS-320L | 05/31/2020: Link | Not Available | Retire & Replace |
| DNS-325 | 09/01/2017: Link | Not Available | Retire & Replace |
| DNS-327L | 05/31/2020: Link | Not Available | Retire & Replace |
| DNS-340L | 07/31/2019: Link | Not Available | Retire & Replace |
The spokesperson added that these NAS devices do not have automatic online updating or alert delivery capabilities, making it impossible to notify the owners of these ongoing attacks.
After the disclosure, D-Link released a security advisory on Thursday to notify owners about the security vulnerability and advise them to retire or replace the affected devices as soon as possible.
It also created a support page for legacy devices, warning owners to apply the latest security and firmware updates available through the legacy support website, although that wouldn’t protect their devices from attackers.
“If US consumers continue to use these devices against D-Link’s recommendation, please make sure the device has the last known firmware,” D-Link warned.
What D-Link didn’t say is that NAS devices shouldn’t be exposed online since they are commonly targeted in ransomware attacks to steal or encrypt data.
In recent months, other D-Link devices (some of them also end-of-life) have been targeted by several Mirai-based DDoS botnets (one of them tracked as IZ1H9). Their owners are continuously working on expanding their capabilities, adding new exploits and targets to attack.






