A threat actor has allegedly exfiltrated approximately 100 GB of personally identifiable information (PII) from Crunchyroll, the Sony-owned anime streaming giant, after gaining access through a compromised employee at the platform’s outsourcing partner, Telus.
The breach, which reportedly occurred on March 12, 2026, has not been publicly acknowledged by Crunchyroll as of this writing.
According to the threat actor, who contacted Cyber Digest, the intrusion was made possible after an employee at Telus Crunchyroll’s business process outsourcing (BPO) partner executed malware on their workstation.
This infection provided the attacker with a foothold into Crunchyroll’s internal environment, enabling lateral movement into sensitive customer-facing systems, including the company’s ticketing infrastructure.
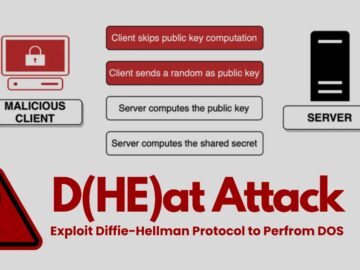
This attack vector aligns with a broader pattern observed in the Telus Digital incident confirmed on March 12, 2026, in which threat actors claimed to have stolen data from Telus and numerous companies that rely on the firm for BPO services such as customer support, AI data operations, and content moderation.
Because BPO providers handle authentication and billing tools across multiple client environments, they remain attractive high-value targets for threat actors seeking to maximize breach scope through a single intrusion.
Data Exfiltration by Attackers
Cyber Digest analyzed a sample of the exfiltrated data provided by the threat actor, which contained highly sensitive categories of customer information, including:
- IP addresses
- Email addresses
- Credit card details
- Customer analytics data (PII)
The threat actor claims a total of 100 GB of data was pulled from Crunchyroll’s customer analytics environment and ticketing system. The nature of the exposed data poses significant risks of identity theft, financial fraud, and targeted phishing campaigns for affected subscribers.
The threat actor stated that Crunchyroll detected and revoked their access approximately 24 hours after the initial breach on March 12, 2026. Despite the relatively short access window, the volume of data exfiltrated suggests the attacker had pre-planned the operation and moved quickly once inside.
Perhaps more alarmingly, the threat actor told Cyber Digest that Crunchyroll has continued to ignore all communications regarding the incident and has made no public disclosure to affected customers.
This silence is particularly concerning given that Crunchyroll was already subject to a class-action lawsuit in early 2026 over alleged unauthorized sharing of user viewing data with third-party marketing platforms.
Crunchyroll has not responded to requests for comment at the time of publication. Cyber Security News will continue monitoring this developing story.
Follow us on Google News, LinkedIn, and X for daily cybersecurity updates. Contact us to feature your stories.