CVE-2023-33538 under attack for a year, but exploitation still unsuccessful

Hackers have targeted CVE-2023-33538 flaw in old TP-Link routers for a year, but no successful exploitation has been seen so far.
Hackers have been trying for over a year to exploit a serious flaw, tracked as CVE-2023-33538 (CVSS score of 8.8), in outdated TP-Link routers, but so far without success.
The vulnerability is a command injection vulnerability in the /userRpm/WlanNetworkRpm component that impacts several TP-Link router models (TL-TL-WR940N v2 and v4, TL-WR740N v1 and v2, and TL-WR841N v8 and v10 router models).
CISA added the issue to the KeV catalog in June 2025 and ordered federal agencies to fix the vulnerabilities by July 7, 2025.
CVE-2023-33538, disclosed in June 2023, lies in the /userRpm/WlanNetworkRpm endpoint, where the ssid1 parameter is not properly sanitized. Attackers can exploit this via crafted HTTP requests to inject commands and potentially execute arbitrary code on the device. Proof-of-concept exploits were briefly shared online and remain accessible through web archives.
“Our telemetry systems detected active, large-scale exploitation attempts for CVE-2023-33538 around the time of the addition to the KEV catalog in June 2025.” reads the advisory published by Palo Alto Networks. “We observed multiple exploitation attempts”

The researchers observed attackers sending HTTP GET requests to the /userRpm/WlanNetworkRpm.htm endpoint, trying to abuse the ssid parameter to run multiple commands. They first downloaded a malicious ELF binary named arm7 from a remote server into /tmp, then changed its permissions to make it executable, and finally ran it with a specific argument.
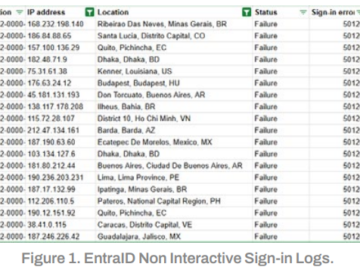
The activity resembles botnet behavior, often linked to Mirai-like malware. The requests also used Basic Authentication with the default credentials admin:admin, encoded in Base64.
“The arm7 binary found in our telemetry appears to be a Mirai variant. It is similar to the one used in the Condi IoT botnet, with multiple examples of the string condi in the file’s code.” continues the report.
The arm7 bot binary connects to its C2 server and listens for commands sent through a network socket. It stores incoming data in a buffer and checks it for specific byte patterns that act as instructions.
Each pattern triggers a different action. The malware can reply with a status message, start or stop operations, activate a lockdown mode, or launch an embedded HTTP server. It can also download updated malware versions depending on the command received.
When an update is triggered, the binary calls an internal update function that removes old files, contacts a hard-coded C2 server (51.38.137[.]113), and downloads fresh binaries for multiple CPU architectures. The malware cycles through several variants to stay compatible with different devices.
The C2 infrastructure is tied to a known malicious host also linked to Mirai-like botnet activity.
If instructed, the malware turns the infected device into a web server. It randomly selects a port, starts an HTTP service, and listens for connections. In this mode, it can distribute malware binaries to other infected devices, helping the botnet spread.
Overall, arm7 acts both as a command-driven bot and a distribution node, constantly updating itself and helping propagate the malware across new systems.
Palo Alto Networks published a detailed analysis of the exploit for CVE-2023-33538 on a TP-Link router to better understand the reason for the failure.
The vulnerability sits in the router’s web interface, specifically in how it handles the ssid1 parameter from the /userRpm/WlanNetworkRpm.htm endpoint. When the system processes this input, it does not clean or validate it properly. That mistake allows an attacker to inject system commands that later get passed to a shell and executed.
The execution flow is long but simple in idea. The router takes the HTTP request, extracts the SSID value, stores it in configuration structures, and compares it with previous settings. When it detects changes, it builds a system command like iwconfig and inserts the SSID value directly into it. The system then runs this command through a shell, which opens the door for code execution.
The experts reproduced the issue by emulating the firmware and logging into the router’s admin panel. They also found that the device requires authentication, so attackers cannot exploit it without valid credentials. The system uses default or weak login setups in many cases, which increases the risk.
Palo Alto Networks also saw important limitations in the environment. The router runs a restricted BusyBox shell with very few tools, so attackers cannot easily download or run advanced utilities. This limits the impact of the exploit in practice.
In summary, the vulnerability is real and allows command injection through ssid1, but successful attacks depend on authentication and the very limited system environment.
“Neither the public PoC for CVE-2023-33538 nor the attack attempts observed in our telemetry would successfully compromise the TP-Link router environment we analyzed. However, our deep dive into the firmware and its emulation reveals a significant gap between the theoretical vulnerability and its practical, real-world application.” concludes the report.
“The attacks seen in the wild were flawed on multiple levels:
- They were unauthenticated
- They targeted the incorrect parameter (ssid instead of ssid1)
- They relied on the wget utility, which is not present in the firmware’s limited BusyBox environment
This demonstrates a common attack pattern of scanning and probing with incomplete or inaccurate exploit code, resulting in noisy but ultimately ineffective attacks.”
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, TP-Link)