Cybercriminals abused Atlassian Cloud’s trusted infrastructure to run a burst of highly automated spam campaigns that redirected victims to fraudulent investment schemes and online casinos, highlighting the growing risk of SaaS-powered email abuse.
By riding on Atlassian Jira Cloud’s strong domain reputation and built-in email authentication, the attackers were able to bypass many traditional email security controls and exploit user trust in legitimate collaboration workflows.
Instead of compromising Atlassian infrastructure, the actors created disposable Jira Cloud instances using free or trial accounts that resolved to shared Atlassian-hosted IP space, allowing them to blend seamlessly with normal tenant traffic.
Recipients who interacted with the emails were funneled through intermediary redirect infrastructure, including commercial email delivery platforms, before being dropped onto final landing pages promoting dubious investments and online casinos, a pattern consistent with broader TDS‑driven scam operations.
The offending instances did not rely on custom domains that matched spoofed organisations, indicating that the actors trusted the inherent legitimacy of Atlassian-generated emails rather than investing in convincing domain impersonation.
To drive clicks and monetise traffic, the attackers wired their links through Keitaro, a legitimate Traffic Distribution System (TDS) commonly used in affiliate and advertising ecosystems but also known to be abused in gambling and crypto-fraud schemes.
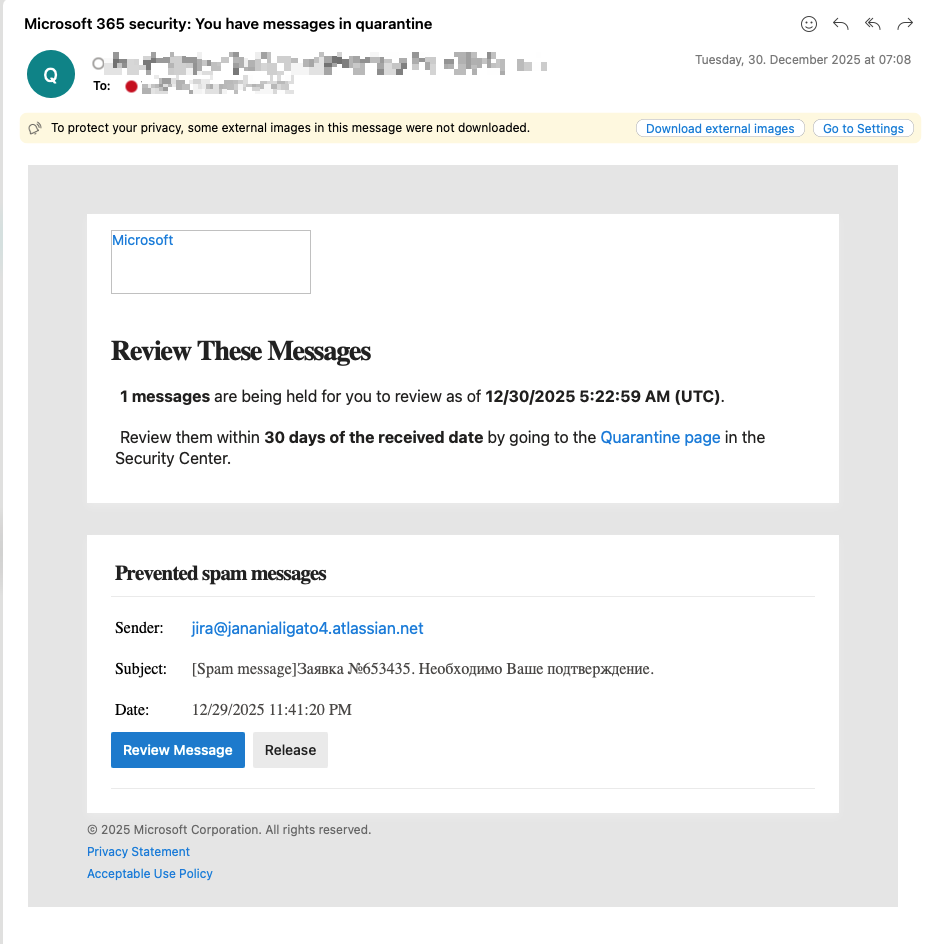
The campaigns leveraged Atlassian Jira Cloud and its connected email system to send large volumes of spam-like notifications from authentic-looking atlassian.net addresses between late December 2025 and late January 2026.
This combination of reputable SaaS mail, third‑party delivery services, and Keitaro-based routing gave the campaigns multiple layers of plausible legitimacy while obscuring the true origin of the scams.
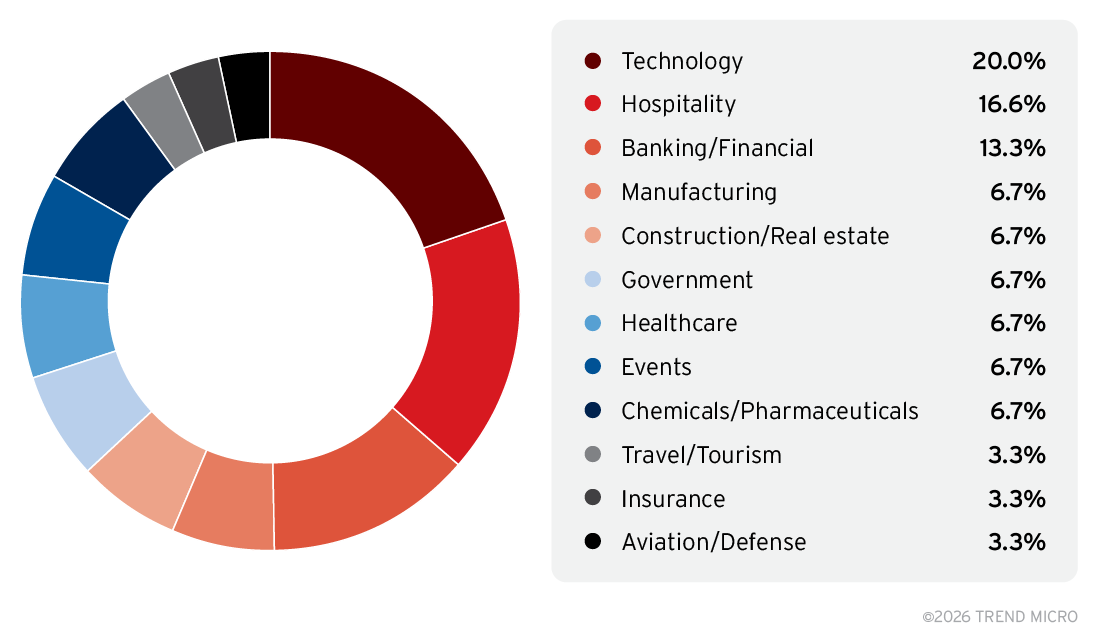
Targeting, Delivery Tactics, and Impact
The operations were not limited to generic spam blasts; instead, they showed deliberate targeting by language, geography, and sector, including government and large corporate environments with heavy collaboration-tool usage.
Messages were localised for English, French, German, Italian, Portuguese, and Russian speakers, with some lures explicitly tailored to highly skilled Russian professionals living abroad and referencing ruble‑denominated investments, underscoring a clear financial motivation.
Subject lines mixed personalised phrases such as fake application confirmations and gaming opportunities with standard Jira notification formats, likely generated by automation rules, to further normalise the emails within environments where Jira alerts are routinely trusted.
Crucially, the attackers exploited the fact that Atlassian’s email workflows automatically apply valid SPF and DKIM authentication to Jira-generated messages, causing many filters to treat them as low risk.
Using Jira Automation and integrated email sending capabilities, they could broadcast to arbitrary external recipients without first onboarding them as users or triggering obvious invitation flows, which helped them maintain anonymity and avoid raising suspicion inside target organisations.
The email body was written in Cyrillic and the currency referenced was the ruble, further indicating that the campaign specifically targeted Russian-speaking recipients.
Organisations already using Jira, especially those with high email volumes and dense notification traffic, were disproportionately exposed because their users are accustomed to interacting with frequent, system-generated emails that appear functionally identical to the malicious messages.
Defensive Recommendations
These campaigns underscore how trusted SaaS platforms can be repurposed as high‑throughput delivery channels for spam, scams, and spear‑phishing, eroding traditional assumptions that vendor notifications are inherently safer than ordinary email.
Security teams should explicitly treat third‑party cloud-generated messages as potential threat vectors, enforcing policy controls, URL analysis, and user-awareness measures for atlassian.net and similar domains instead of blanket‑allowing them on the basis of reputation alone.
Proactive controls should include URL rewriting and detonation for TDS-style redirect chains, anomaly detection around unusual Jira-generated subject lines or sending patterns, and continuous monitoring for campaigns that blend standard SaaS notification formats with marketing or financial-lure content.
Enterprises are also encouraged to deploy advanced, identity‑aware email security solutions that specialise in protecting collaboration workflows, such as AI‑driven platforms that combine behavioral analysis, layered detection, and risk-based policies to spot abuse of reputable SaaS infrastructure.
Integrated threat intelligence on emerging SaaS‑abuse campaigns, including indicators for Keitaro-based TDS infrastructure and scam domains, can further enhance hunting and incident response by allowing defenders to sweep their environments for related messages, URLs, or sending patterns.
Ultimately, aligning email security, SaaS governance, and threat intelligence around the reality of cloud‑native spam and fraud operations is essential to mitigating similar Atlassian Cloud–based campaigns going forward.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.