Windows Management Instrumentation (WMI) is a critical utility built into the Windows operating system designed to help administrators monitor status and automate routine tasks.
However, cybercriminals have increasingly weaponized this legitimate infrastructure to maintain persistent access to compromised networks.
Unlike traditional malware strategies that rely on visible startup folders or registry run keys, WMI abuse allows attackers to hide in plain sight.
By leveraging WMI Event Subscriptions, hackers can ensure their malicious payloads execute automatically without leaving obvious traces that standard antivirus scans typically flag.
The Mechanics of WMI Persistence
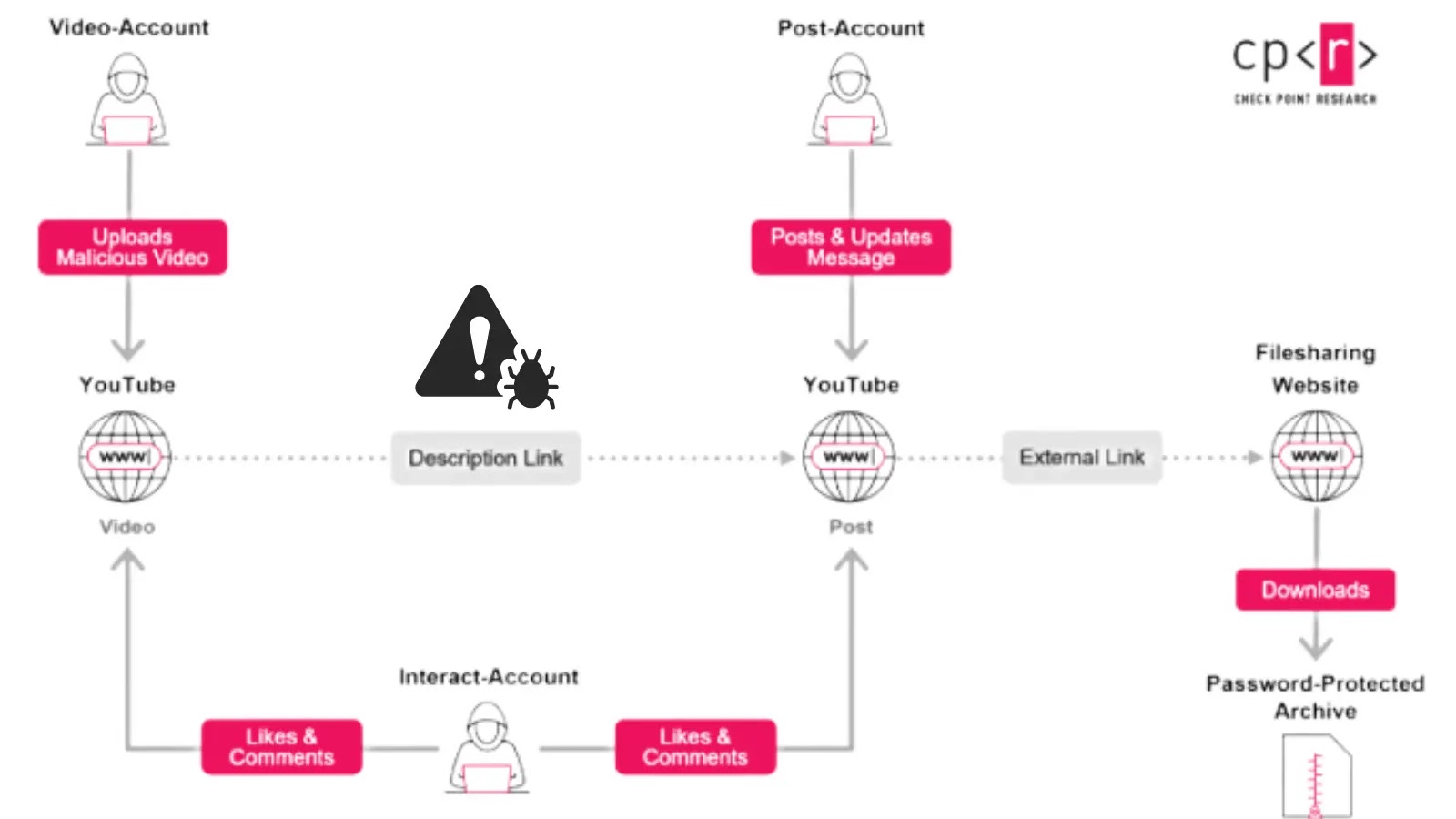
According to Winston Ighodaro, the core of this attack technique relies on abusing the event subscription feature within the WMI architecture.
Attackers configure specific triggers, technically known as Event Filters, which silently wait for standard system activities such as a user logging on, a specific uptime duration, or a system reboot.
When these pre-defined conditions are met, the system automatically triggers a Consumer action.
This action executes a malicious script or command directly from the WMI repository.
Because the malicious logic is embedded deep within the operating system’s management database rather than sitting as a standalone file in a startup folder, the attack operates stealthily.
This method avoids creating new services or scheduled tasks, making it ideal for long-term espionage campaigns.
Detecting WMI-based persistence requires proactive threat hunting using specific command-line tools, as the activity often blends in with normal system administration traffic.
Security teams and defenders typically use PowerShell to query the WMI namespace to inspect existing event filters, consumers, and bindings.
By listing these components, analysts can identify anomalies, such as a command line configured to launch a script every time a user logs in.
Defenders must regularly audit the WMI repository for unauthorized entries to ensure that a compromised system does not remain under attacker control even after standard remediation efforts.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.