DarkSword exploit leak puts up to 270 million iPhones at risk, with hackers able to access data through Safari without user interaction or detection. Researchers say the exploit has been in use since late 2025.
A major new cybersecurity threat has emerged for iPhone users worldwide, as researchers have uncovered a new hacking tool called DarkSword. According to a joint investigation by Google, Lookout, and iVerify, hundreds of millions of people could be at risk if they have not updated their software recently. This situation is particularly serious because the malware often operates without the user ever knowing their device has been compromised
What is DarkSword?
DarkSword is an exploit chain; this means the hackers do not just use one trick to get into your phone; they use six different vulnerabilities in a row. By combining these flaws, they can bypass security to gain full control over the device. This approach allows them to attack from multiple angles, making it much harder for standard security features to block them.
The attack, as per Lookout’s report, often starts when a user visits a website using the Safari browser. This method is called a drive-by download, where you do not even have to click a download button to get infected, and simply visiting a compromised link is enough for the malware to begin its work.
Lookout has also tracked a suspected group called UNC6353 using watering hole attacks to hijack trusted sites, such as the Ukrainian News of Donbas and official court pages. They even found a potential infection at a food processing plant as recently as 12 February 2026, proving that even legitimate daily browsing can carry risks.
Further probing by Google Threat Intelligence Group revealed that in early November 2025, a hacking group known as UNC6748 used a fake website called snapshare.chat, designed to look like Snapchat, to trick users in Saudi Arabia, using hidden code to launch the attack automatically. Other impacted countries include Ukraine, China, Turkey, and Malaysia.
What can the hackers see?
Once DarkSword is inside a phone, it works with incredible speed. It can grab your data in just a few minutes and then erase its tracks so you never know it was there. The spyware targets almost everything on your device, including your private text messages, call records, and Wi-Fi passwords stored in the iOS keychain, and also attempts to steal your physical location, browser history, calendar entries, health data, and even digital crypto wallets.
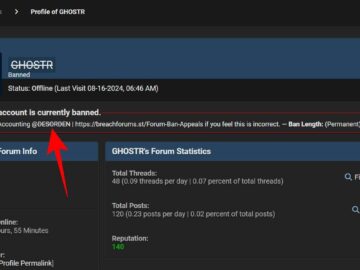
DarkSword exploit leaked publicly on GitHub
The risk has escalated further after a working version of the DarkSword exploit chain was publicly leaked on GitHub, lowering the barrier for misuse. Reports from multiple outlets confirm that the code is not just theoretical; it includes a usable exploit kit that can be deployed with minimal effort.
This means attackers no longer need advanced research capabilities to replicate the attack, as the technical groundwork has already been done. Security researchers, Matthias Frielingsdorf in particular, warn that such leaks often prompt rapid copycat activity, with lower-skilled actors targeting vulnerable devices at scale, increasing the likelihood of widespread opportunistic attacks against unpatched iPhones and iPads.
The research firm iVerify estimates that around 270 million devices are currently vulnerable. If your iPhone or iPad is running software between iOS 18.4 and 18.7, you are at risk. The danger has grown because a version of DarkSword was recently leaked on the site GitHub.
How to stay safe
Apple has confirmed that the newest software, iOS 26, is safe from these attacks. So, keeping your phone updated is the most vital step in staying secure. For those using older models, Apple released emergency updates on 11 March 2026 for iOS 15 and 16. If you cannot update to the latest version, Apple and Google advise turning on Lockdown Mode in your settings to provide extra protection against these threats.