Recording Slides Supplemental Demo Video:

Source link
Related Articles
All Mix →The AI Coin-sorter Analogy | Daniel Miessler
I’ve had this analogy in my mind for a while for AI. Specifically, neural nets. Imagine a coin sorter with a flat surface the size…
How Long Does Pentesting Take? [5 Factors of Pentesting Speed]
Table of Contents Security Testing Alternatives The Problem With Pentest Speed Measuring Pentest Method Speed Security Testing Speed Evaluation Matrix The Power of PTaaS With…
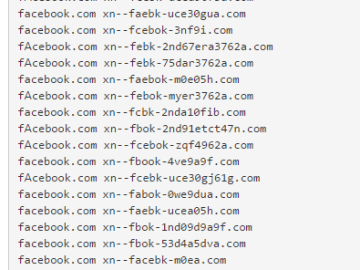
Punicoder – discover domains that are phishing you – honoki
So we’re seeing homograph attacks again. Examples show how ‘apple.com’ and ‘epic.com’ can be mimicked by the use of Internationalized Domain Names (IDN) consisting entirely…
Newly added security tests, August 28, 2017: vBulletin and WordPress vulnerabilities
To help you keep up with the latest vulnerabilities, we add new security tests to Detectify on a regular basis. The latest additions to the…
EASM in 2023 – Blog Detectify
Table of Contents It’s nearing the end of 2023, and we’ve recently published a report, “State of EASM 2023”, offering insights into the state of…
Why I Hate Anthropic and You Should Too
All the best influencers hate Anthropic right now, and for good reason. They ruined everything, and they’re worthy of every bit of hate they get.…