Recording Slides Supplemental Demo Video:

Source link
Related Articles
All Mix →Manipulating data with Django migrations
How to update Django models and manipulate existing data using migrations. Growing, successful applications are a lovely problem to have. As a product develops, it…
Taking The Guesswork Out of Vulnerability Reporting
In today’s world, the majority of security vulnerabilities are introduced by software engineers. To build the most secure code, we must acknowledge the reality that…
Synthetics Recorder: Code injection when recording website with malicious content
Elastic disclosed a bug submitted by dee-see: https://hackerone.com/reports/1636382 – Bounty: $4895 Source link
Reading RFCs for bug bounty hunters
Table of Contents Why?! Before you dive in The Security Considerations section Reviewing past versions of an RFC Errata exist Conclusion Update (Dec, 2022) Yesterday,…
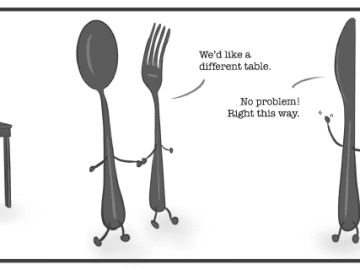
A New Take on an Old Saying · rez0
Table of Contents The Impact of Digital Influencers The Modern Life Hack: Imitation for Advancement Don’t Over-Consume People You Don’t Want to Become The saying…
Liberal and Conservative
Conservatives long for the world of Leave it to Beaver, Christmas Story, and Babe Ruth. A world of everyone looking the same, talking the same,…