DesckVB RAT is emerging as a highly active and stealthy malware threat in 2026, leveraging layered obfuscation and fileless execution techniques to bypass traditional security defenses.
The attack chain begins with a malicious JavaScript file that hides its true intent through complex encoding and code replication.
This script copies its own logic into PowerShell and text files, then drops a PowerShell payload into the public directory at “C:UsersPublic.”
Once executed, the script uses the command “powershell -ExecutionPolicy Bypass” to run without restriction, a common tactic to evade security controls.
Security researchers have identified that this Remote Access Trojan (RAT) primarily uses heavily obfuscated JavaScript as its initial infection vector, making early detection significantly more difficult.
Before proceeding, the PowerShell script checks for internet connectivity by attempting to reach Google.
How DesckVB RAT Hides Its Activity
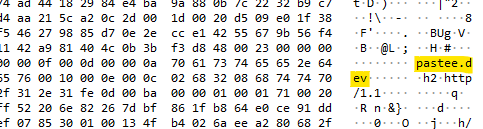
It then initiates communication with external infrastructure, including the domain andrefelipedonascime1768785037020.1552093.meusitehostgator.com.br and a Pastee link.
Notably, the Pastee URL is concealed using Base64 encoding combined with string reversal. When decoded and corrected, it resolves to a live payload-hosting link, highlighting a classic obfuscation method used to avoid static analysis.
The next stage introduces a fileless .NET loader. Instead of writing files to disk, the malware loads a .NET assembly directly into memory using reflection and in-memory execution.
This significantly reduces its forensic footprint and helps it evade antivirus detection. The loader leverages InstallUtil.exe, a legitimate .NET Framework utility, to execute malicious code a well-known “living-off-the-land” technique.
The payload delivered from the attacker-controlled domain includes a DLL named ClassLibrary3.dll, which is executed entirely in memory.
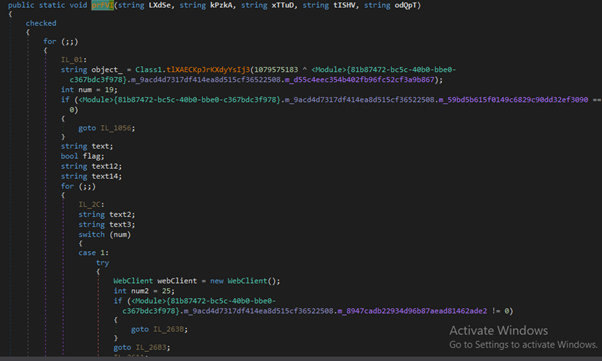
Within it, a method called prFVI handles network communication using a WebClient object, likely to retrieve additional payloads or instructions from a command-and-control (C2) server.
At the core of the attack is an obfuscated .NET routine responsible for process creation and injection.
Stealth Tactics in Modern Malware
Using Windows API calls such as CreateProcessA, the malware spawns a new process in a controlled or suspended state, then injects malicious code into it. This allows the final payload, identified as Microsoft.exe, to run under the guise of a legitimate process.
.NET routine where a method is being invoked with encoded parameters, including a reference to “ps1” (PowerShell), indicating preparation for a PowerShell-based payload.
Runtime analysis reveals that the malware decrypts an embedded configuration stored as encoded string arrays.
These configurations include C2 details such as the domain manikandan83.mysynology.net and port 7535. Additional modules, including a keylogger and antivirus detection component, are also loaded into memory, enabling data theft and system monitoring.
Overall, DesckVB RAT demonstrates a sophisticated, multi-stage infection chain that combines obfuscation, fileless execution, and encrypted communication.
Network analysis shows that infected systems establish encrypted HTTPS connections to external servers, blending malicious traffic with normal web activity.
TLS handshakes and encrypted payload exchanges make inspection difficult, while captured traffic indicates active communication with C2 infrastructure.
Observed data includes module names like “DetectAV” and “Ping,” suggesting the malware continuously monitors system defenses and maintains connectivity with its operators.
Its ability to operate entirely in memory and use legitimate tools makes it a significant threat to modern enterprise environments.
Indicators of Compromise (IOCs)
| MD5/File name | Details |
| 220e11c678bcba151545ce19398e08b8802103bfbbc11696f3301ea8fa38190c | JS File |
| 138f29a9190acad9c392cc6fe37104b8 | okfIt.ps1 |
| andrefelipedonascime1768785037020[.]1552093[.]meusitehostgator[.]com[.]br pastee.dev | Malicious Domain |
| f040a81be4d3b3584b79036d77794c16 | ClassLibrary3.dll |
| fd684ea48cb97714d4f8a0c741cf862b | ClassLibrary1.dll |
| f17ed8c5c54bae6c74d0d793d7c7a72a | Microsoft.exe |
| manikandan83.mysynology.net | Malicious IP: 45.156.87.226 |
| a624f6cb9ccd4106f91e58049163c757 | Keylogger.dll |
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.