Does Cybersecurity Require Programming?

Source link
Related Articles
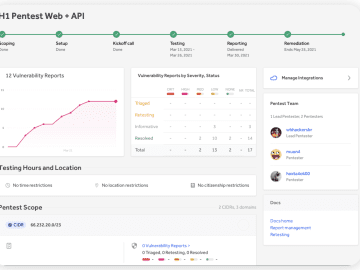
All Mix →How HackerOne Positively Influences Zebra’s Software Development Life Cycle
HackerOne’s Platform Catches Everything Organizations can ensure that security testing is a continuous process by combining regular pentests with bug bounty and VDPs. Some companies…
Geek Battles: A Call for Perspective
Table of Contents The Classics The Linux Case Humans are funny Hardcore Insecurity Why It’s Not Important Objectivity and Perspective Who commands more respect? “Linux…
Use Hackerone’s Enhanced Pentest as a Service to Streamline Security Testing
Table of Contents New capabilities improve pentesting to increase attack resistance Plan, Track Progress, and Launch Quickly Scope, Setup, and Launch on Your Own Timeline…
Hacking Razer Pay Ewallet App
Table of Contents Introduction TL;DR Background Deleting other user’s bank account Frida to the rescue Rinse and repeat Final thoughts Introduction This write-up is about…
Can LLMs Create New Things? · Joseph Thacker
Table of Contents Clarifying the Question No Systemic Constraint for Novelty Provably Creative? Comparison to Humans AI Art The Reason it’s Hard Novelty How-To 1)…
My Gaming Idea | Daniel Miessler
Table of Contents Isn’t Everyone Doing That Already? More On The Model FPS Casual Why I’m not pursuing it Conclusion [ July 27, 2006 ]…