
Don’t make random HTTP requests.

Source link
Related Articles
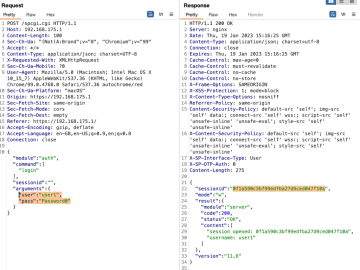
All Mix →Leaking Remote Memory Contents (CVE-2023-22897) – RCE Security
Table of Contents Requirements for Successful Exploitation Leaking Memory Contents Root-Cause Analysis Vendor Response While my last finding affecting SecurePoint’s UTM was quite interesting already,…
Cross handling Cookies in Zest
Table of Contents Background knowledge Node Client Problem Assign Cookie Step by Step Get cookie from Client Use variable Run Conclusion 오늘은 Zest 스크립트에서 Headless…
Spoutible Enhances Platform Security through Partnership with Wallarm
Table of Contents "Wallarm is already integrated at Spoutible, enhancing API security while reinforcing the company’s overall security posture." Christopher Bouzy, CEO Spoutible Elevating API…
My Preferred Definition of Security
Table of Contents Risk Summary Links There is much debate in the information security world regarding the proper definition of security. I have seen dozens…
Real Hacking | Daniel Miessler
/. is running a story on the upcoming OpenBSD Hackathon, and I thought it important to point out what the term “Hack” means — not…
[tl;dr sec] #296 – AI Automates CVE -> Exploit, Apple Defeats Memory Corruption, Moar NPM Backdoors
Table of Contents AI auto-generating exploits from CVEs for $3, not actually but Memory Integrity Enforcement makes it harder, surprisingly NPM packages were backdoored Bardcore…


![[tl;dr sec] #296 - AI Automates CVE -> Exploit, Apple Defeats Memory Corruption, Moar NPM Backdoors](https://image.cybernoz.com/wp-content/uploads/2025/09/tldr-sec-296-AI-Automates-CVE-Exploit-Apple.png)