By Alan Stewart-Brown, VP EMEA, Opengear
Disruption in financial services rarely follows a clean script. A misconfiguration, a spike in malicious traffic, or a poorly timed change can cascade across platforms and teams, particularly where systems and suppliers are tightly coupled. When that chain reaction starts, the challenge is rarely identifying the fault. It is retaining enough control to limit the damage and restore services before the situation compounds.
That is precisely the environment DORA was designed to address. The EU’s Digital Operational Resilience Act has applied since January 2025, and its expectations are clear: Firms must manage IT risk systematically, test resilience under realistic conditions, handle incidents with discipline, and govern the third parties that underpin critical functions. Non-compliance carries real consequences, including supervisory measures, financial penalties, and remediation orders.
DORA raises the standard for incident detection, regulatory reporting, and supplier oversight. It expects resilience testing to reflect genuine stress scenarios, with cybersecurity and IT operations aligned and accountable at board level. The goal is not infrastructure that never fails. It is organisations that remain in command when failure arrives.
Progress Is Real, but Uneven
More than a year in, maturity across the sector remains inconsistent. Some institutions have made meaningful investments in continuity and cyber response. Others are still laying foundations, often with limited specialist resource and limited tolerance for extended disruption.
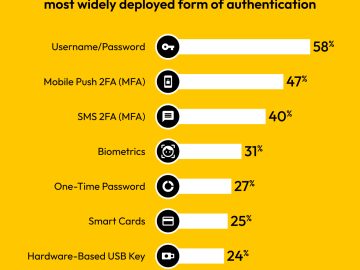
Even where frameworks exist on paper, confidence tends to erode when firms test response under realistic constraints, when access is restricted and several dependencies fail simultaneously. A 2025 Censuswide survey found that 96% of EMEA financial services organisations believed they still needed to improve resilience to meet DORA requirements. Governance documents matter, but resilience only becomes real when firms can act consistently across a complex mix of systems, services, and suppliers under pressure.
When Access Fails, Incidents Escalate
In a major incident, visibility is rarely the problem. Teams can see what is happening. What becomes difficult is control, particularly when the usual routes into the environment are unavailable or unsafe to use.
A network fault can sever connectivity to key sites. A cyber incident may trigger containment measures that deliberately reduce access. Identity services can become unstable, blocking privileged access at exactly the moment it is needed. Engineers may understand the fault clearly and still be unable to reach the controls required to isolate affected components, stabilise essential services, and begin recovery.
This is where many resilience programmes have a gap. Backup and disaster recovery protect data and workloads, but they do not ensure that teams can administer infrastructure while an incident is unfolding. If the production network is also the path engineers use to reach and configure devices, a severe outage can eliminate both the service and the means of restoring it. Time is lost not through lack of expertise, but because the route to apply the fix is gone.
Supply Chain Disruption Adds Complexity
Financial services firms depend on shared platforms and external providers, from cloud infrastructure to outsourced applications, connectivity services, and specialist networks. When disruption originates in the supply chain, the firm must still contain impact and maintain essential services, often while coordinating with third parties managing the same issue across multiple clients.
Verizon’s 2025 Data Breach Investigations Report noted that third-party involvement in breaches had doubled to 30%. Plans that assume a firm can always resolve the root cause internally are increasingly misaligned with how incidents actually unfold.
DORA reflects this by raising expectations for third-party oversight and pushing firms to connect governance with operational outcomes: understanding which providers support critical functions, what failure looks like in practice, and what the firm can actually do when an external dependency is under stress. Contract clauses matter, but the more pressing question is operational. What can the firm do, in real time, to reduce impact and restore safe service when a provider is impaired?
Keeping Control During Recovery
This brings DORA back to a practical test: Can the organisation retain operational control during severe disruption, including when the primary network is out of action or locked down for containment?
Separating management access from the production network directly supports this. An independent management plane, commonly described as out-of-band management, provides a dedicated route to critical infrastructure even when the primary network is impaired, unstable, or deliberately segmented. That matters because containment often requires reducing connectivity, which can simultaneously block the route engineers need to effect repairs.
Independent access allows teams to reach network equipment and supporting systems, restore known-good configurations, roll back changes, and re-establish minimum safe connectivity without waiting for the production network to recover first. It also supports controlled intervention during high-risk routine activities such as software updates, configuration changes, and migrations.
Dependency mapping, realistic resilience testing, and clear governance structures remain essential to meeting DORA’s requirements. What independent access adds is a practical means of staying in control when the main route into the environment has become part of the problem.
After more than a year of application, DORA’s expectations are not softening. Firms that design their infrastructure to maintain access, limit impact, and restore services safely reduce both operational risk during incidents and regulatory risk in the aftermath.
Alan Stewart-Brown is VP EMEA at Opengear, focused on operational resilience and secure infrastructure operations across regulated industries. He works with financial services and critical infrastructure organisations on incident readiness, continuity planning, and maintaining controlled access during outages and cyber events.
Going to DTX Manchester in April? Stop by Opengear’s booth #C101 and Schedule Opengear’s Alan Barnett’s speaking session:
‘Staying in Control When It Matters Most: Building Operational Resilience with Smart Out-of-Band Infrastructure’
Alan Barnett, Sales Engineering Manager, EMEA
Wednesday, 29 April | 15:25–15:50
Modern Infrastructure and Connected Experiences Stage