DPRK-linked operators are maintaining a relentless focus on the crypto sector, with activity accelerating rather than slowing in the year since the record-breaking Bybit breach.
On 21 February 2025, threat actors linked to North Korea stole around 1.46 billion dollars in cryptoassets from Dubai-based exchange Bybit, in what remains the largest confirmed crypto theft to date.
By August 2025, over $ 1 billion of the Bybit haul had already been laundered using refund addresses, worthless tokens, and a diversified mix of crypto-mixing services, much of it routed through suspected Chinese OTC brokers.
The majority of stolen Bybit funds are now assessed as processed, but instead of marking an end point, the incident signalled an inflection in North Korea’s financially motivated cyber operations.
Elliptic was among the first to attribute the exploit to DPRK operators, an assessment later backed by US law enforcement.
Elliptic’s subsequent tracking shows that DPRK-linked actors went on to steal a record 2 billion dollars in cryptocurrency during 2025, bringing their known cumulative crypto haul to more than 6 billion dollars.
These proceeds are widely believed to help fund North Korea’s nuclear and missile programmes and have turned crypto exploitation into a strategic revenue stream for the regime.
Early 2026 indicators are equally stark, with Elliptic recording roughly twice as many exploits in January 2026 as during the same month a year earlier, underscoring an ongoing operational tempo.
Social Engineering at Scale
Across Bybit and newer incidents, social engineering remains the primary initial access vector, despite the technical complexity of the subsequent theft and laundering operations.
DPRK operators increasingly invest in convincing personas, outreach messages and pretexts, and are assessed to be using AI tools to refine language, remove obvious localisation tells and scale their engagement.
Two named campaigns, DangerousPassword and Contagious Interview, continue to generate steady revenue for DPRK-linked clusters.
This shifts the risk beyond exchanges to include individual developers, contractors and anyone with privileged access to wallets, infrastructure or signing keys.
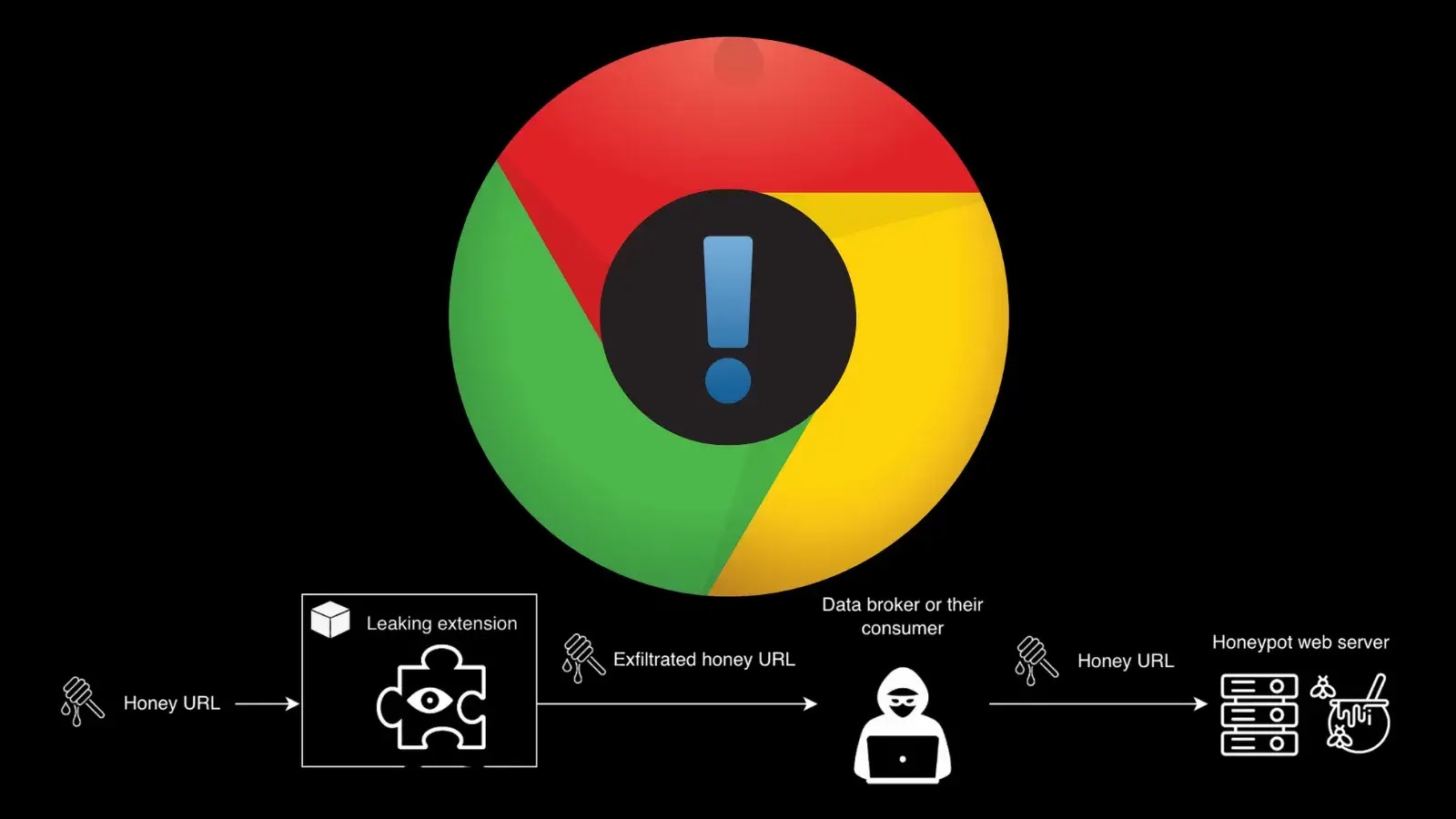
DangerousPassword leverages compromised social media accounts to contact targets using a weak real-world pretext and move them onto Zoom or Microsoft Teams calls.
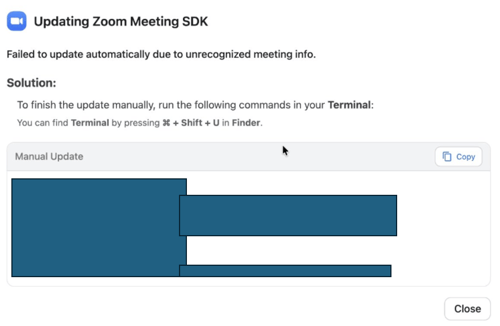
During the call, victims are presented with a fake audio error and instructed to run command-line code to install a supposed SDK, which actually deploys malware designed to harvest private keys, seed phrases and stored credentials, including those for further social media compromise.
Contagious Interview instead abuses fake job offers and “technical tests,” directing victims to download booby-trapped repositories from reputable platforms that install similar credential-stealing malware when executed.
From 1 January 2026 to the article’s publication, Elliptic estimates these two campaigns generated 37.5 million dollars for DPRK operators, with many victims using devices connected to employer infrastructure, thereby exposing entire organisations.
Running in parallel is a longer-term IT worker infiltration model, where DPRK nationals pose as freelance or remote developers on legitimate crypto projects.
These individuals often perform credible work while quietly seeking to compromise colleagues’ devices, plant backdoors or secure persistent access and insider knowledge.
To evade sanctions controls and basic KYC checks, operatives rely on fabricated identities, cloned or stolen accounts, invented work histories and “rented” laptops located in benign jurisdictions, sometimes referring additional DPRK operatives into the same organisation once embedded.
Activity around the Bittensor-linked project Tenexium suggests DPRK operators may now be progressing from infiltrating existing ecosystems to building and weaponising their own.
On 1 January 2026, Tenexium’s website went offline at the same time as roughly 2.5 million dollars in liquidity was drained from its treasury wallet.

The project, marketed as a decentralised spot margin trading protocol within the TAO ecosystem, had only been registered in late 2025, and both its main site and GitHub presence are now inaccessible, with no public explanation from the team.
Community reporting later identified suspected DPRK IT worker personas among Tenexium contributors, including one assessed with high confidence.
Using support for the TAO network in its analytics platform, Elliptic traced Tenexium-linked funds across chains and into centralised services, observing laundering patterns and cross-chain overlaps consistent with other DPRK-attributed exploits in its dataset.
Implications for Crypto Defenders
Twelve months after the Bybit exploit, DPRK’s crypto theft posture is best understood as a sustained, well-resourced campaign rather than isolated mega-heists.
The maturation of social engineering tradecraft, supported by AI-driven content generation, and the blending of developer infiltration with potentially DPRK-built projects expands the threat surface across the entire cryptoasset ecosystem.
Exchanges, DeFi protocols infrastructure providers and individual contributors must therefore treat human-facing social vectors and supply-chain entry points as critical security priorities, not secondary risks.
Elliptic continues to monitor DPRK-linked wallets and laundering routes across more than 60 supported blockchains, enabling exchanges and financial institutions to screen for and trace funds tied to Bybit and subsequent DPRK exploits.
For organisations in the sector, combining rigorous identity verification for remote hires, hardened developer workflows and continuous blockchain analytics will be essential to resist a DPRK threat that shows no sign of slowing.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.