An infostealer malware campaign has collected millions of logins from users of various gaming websites, including players that use cheats, pay-to-cheat services.
The details emerged after Zebleer, the developer of Phantom Overlay cheats for Call of Duty and Counter-Strike, apparently found an infostealer database.
“The DB for the stealer represents gaming related accounts much more than anything else,” Zebleer said, adding that “it’s the largest infostealer malware campaign targeting gamers/cheaters in history.”
According to the Phantom Overlay developer, the database contains credentials for several million gamers whose systems were infected in malware campaign.
| Service | Accounts |
| Battlenet | 3,662,647 |
| Activision | 561,183 |
| Elite PVPers | 117,366 |
| UnknownCheats | 572,831 |
| Phantom Overlay | 1,365 |
| BLOG | 67,152 |
| RN | 1,044 |
| ACD | 3,818 |
| AA | 21,564 |
| EO (two domains) | 85,360 |
| Iniuria | 14,181 |
| Gamesense | 18,465 |
The cheat developer also notes that the domain with the highest number of stolen accounts is Discord, which stands at 14 million entries in the database.
Although it has not been confirmed how the malware was distributed to such a large number of users, Zebleer says that some free or cheap software advertised to Call of Duty gamers packs an infostealer.
BleepingComputer has reached out to Zebleer for additional details about the database but has not received a reply by publishing time.
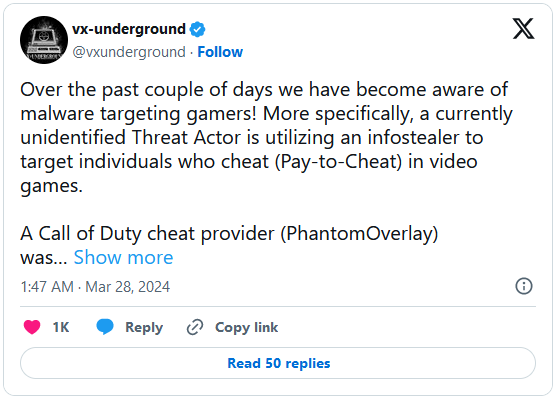
In a separate post, cybersecurity research group vx-underground, says that multiple users have been reporting that their Electrum BTC wallets were compromised as a result of malware activity on the computer.
In the post, vx-underground says that the gaming forum Elite PVPers confirmed that more than 40,000 valid accounts were compromised.
It appears that the credentials are not present in other publicly available databases with stolen account logins.
Although the number of logins in the database indicates a significant impact on the gaming community, it is unclear how many of the accounts are valid or duplicates.
Activision Blizzard recommends 2FA
Reportedly, Activision Blizzard is coordinating with cheat developers to limit the campaign’s impact and provide security instructions to holders of compromised accounts.
BleepingComputer has reached out to Activision Blizzard for a comment and a spokesperson said that its “servers remain secure and uncompromised.”
“There have been claims that some player credentials across the broader industry could be compromised from malware from downloading or using unauthorized software. Activision Blizzard servers remain secure and uncompromised,” Activision Blizzard told BleepingComputer.
“If players believe they may have clicked on a suspicious link or if they want to ensure their account is protected, they can change their password and follow recommended best practices,” the company added, referring to two-factor authentication (2FA).
It is worth mentioning that Activision Blizzard does not have much control on the situation because their visibility is limited as far as the game resources its players use. At this point, the company can get a list of the stolen credentials and force a password reset an affected accounts.
To ensure the protection of their account and make it more difficult for hackers to profit even when credentials are stolen, users are recommended to enable two-factor authentication.