A newly disclosed vulnerability in the widely used Android library EngageSDK has raised serious concerns across the cryptocurrency ecosystem, potentially exposing millions of users to data theft and unauthorized access.
Security researchers identified a critical “intent redirection” vulnerability in EngageSDK, a third-party Android SDK commonly used for push notifications and in-app messaging.
The issue allows malicious applications installed on the same device to bypass Android’s sandbox protections and interact with sensitive components of other apps.
This weakness is particularly alarming because many affected applications are cryptocurrency wallets. Researchers estimate that over 30 million wallet installations and more than 50 million total app installs were exposed through vulnerable versions of the SDK.
Although there is no confirmed evidence of active exploitation, the nature of the vulnerability means attackers could potentially access personally identifiable information (PII), user credentials, and even financial data.
How the Attack Works
Android isolates apps using a sandbox model, assigning each app a unique identity and restricting access to its private data. However, apps can communicate using “intents,” which are messaging objects used to trigger actions across components.
The EngageSDK vulnerability abuses this mechanism.
- A malicious app sends a crafted intent containing a specially designed URI.
- The vulnerable app processes this intent using EngageSDK’s exported activity (MTCommonActivity).
- The SDK then unknowingly redirects the intent with its own permissions.
- This allows the attacker to access protected components or data inside the target app.
For example, a rogue app could trick a crypto wallet into granting read and write access to its internal storage, exposing wallet data or authentication tokens without user awareness.
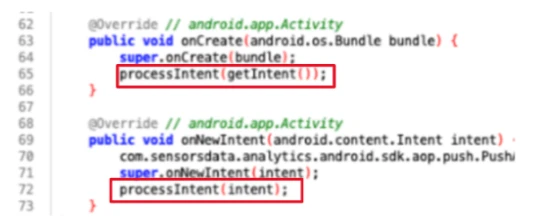
The vulnerability originates from an exported activity automatically added by the SDK during the build process. Because this component appears only in the merged Android manifest, many developers fail to notice it during development.
More critically, the SDK processes untrusted input and constructs a new intent using unsafe flags, such as those granting persistent read/write permissions.
The processPlatformMessage() method instantiates a JSON object using the uri string supplied as an argument to this method.
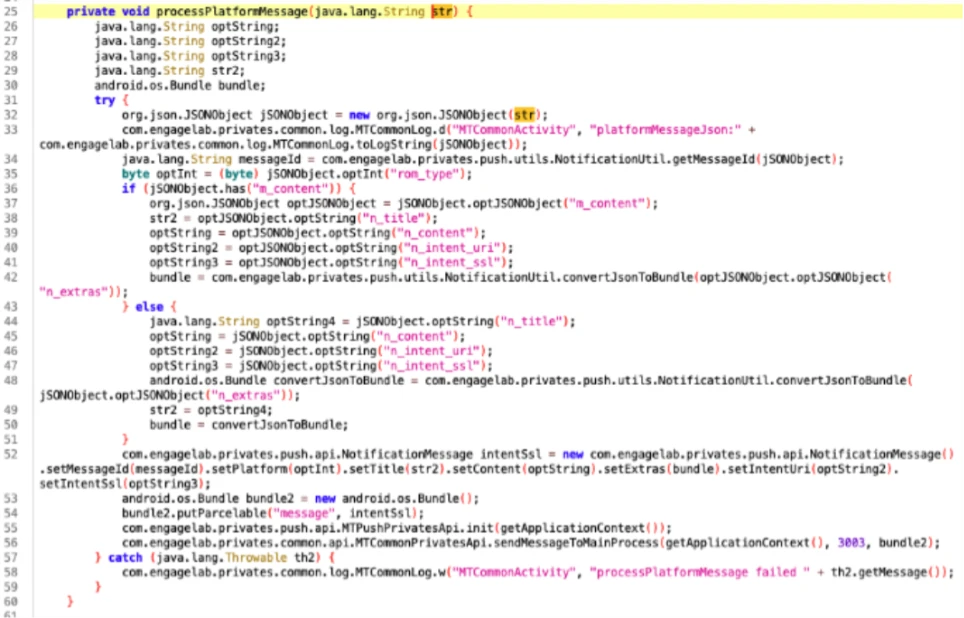
Instead of sending a harmless implicit intent, the SDK generates an explicit one targeting sensitive components, effectively enabling privilege escalation.
Patch and Disclosure
Microsoft researchers discovered the issue in EngageSDK version 4.5.4 and reported it in April 2025 under coordinated vulnerability disclosure practices. The vulnerability was later fixed in version 5.2.1, released on November 3, 2025.
The patch turns off the vulnerable component by marking it as non-exported, preventing external apps from invoking it.
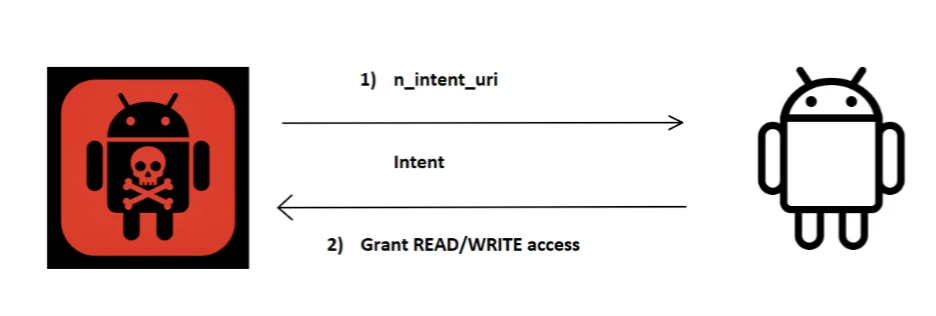
Exploitation starts when a malicious app creates an intent object with a crafted URI in the extra field. The vulnerable app then processes this URI, creating and sending an intent using its own identity and permissions.
Google has since removed affected apps from the Play Store, and Android has introduced additional runtime protections to mitigate exploitation risks on user devices.
This incident highlights a growing risk in mobile app development: third-party SDK dependencies. Even well-secured applications can become vulnerable if integrated libraries introduce hidden or insecure components.
In high-value sectors like cryptocurrency, such weaknesses can have large-scale consequences. A single flawed SDK can silently expand the attack surface across millions of devices.
Developers should immediately update to EngageSDK version 5.2.1 or later and audit their applications for unintended exported components. Reviewing the merged Android manifest is essential to identify hidden risks introduced by dependencies.
Users are currently protected through Google Play enforcement and Android security updates, but keeping apps updated remains critical.
This case serves as a reminder that supply chain security is now a central challenge in mobile ecosystems, where a single overlooked vulnerability can ripple across millions of users.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.




