- Top Enterprise Patches Deployed
- Most Deployed Enterprise Patches (last 12 months)
- Compare Your Environment
- Why Third-Party Patch Automation Became Essential
- Most Common Automated Patches
- Applications with the Longest Patch Delays
- When a Patch Exists, but Deployment is Complex
- Most Commonly Delayed Patches
- When No Vendor Patches Are Available
- Top 5 Qualys TRU Vulnerabilities Addressed Permanent Fixes (last 12 months)
- Remediation Beyond Patching
- Most Common Qualys, Out-of-The-Box Remediation Scripts Used
- What These Trends Mean for Security Teams
- Frequently Asked Questions (FAQs)
Executive Summary
In the last 12 months, enterprises deployed millions of patches, yet many organizations remain exposed due to delayed remediation and unpatched third-party software.
Key benchmarks from global enterprise environments:
Over 8 million Google Chrome patches were deployed.
Visual C++ and .NET remained among the most delayed in patching.
The average mean time to remediation (MTTR) for complex apps stretched to 5 months and 10 days.
Automated third-party patching became a critical strategy for organizations.
When patches were unavailable, mitigations and remediation scripts played a vital role in reducing exposure.
Security teams can use these benchmarks to evaluate whether their remediation strategies are effectively minimizing risk.
Security teams measure progress in many ways: vulnerability counts, patch cycles, risk scores. But the true measure of security maturity is risk reduction at scale.
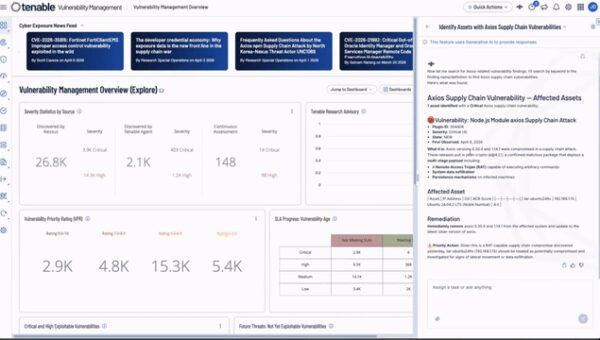
Over the last 12 months, organizations across global enterprise environments deployed patches, mitigations, and remediation workflows at massive scale. By analyzing anonymized remediation activity, several patterns emerged that reveal where security teams focused their efforts and where exposure often persisted.
The data below reflects global enterprise remediation trends. The real question is: how does your organization compare?
Top Enterprise Patches Deployed
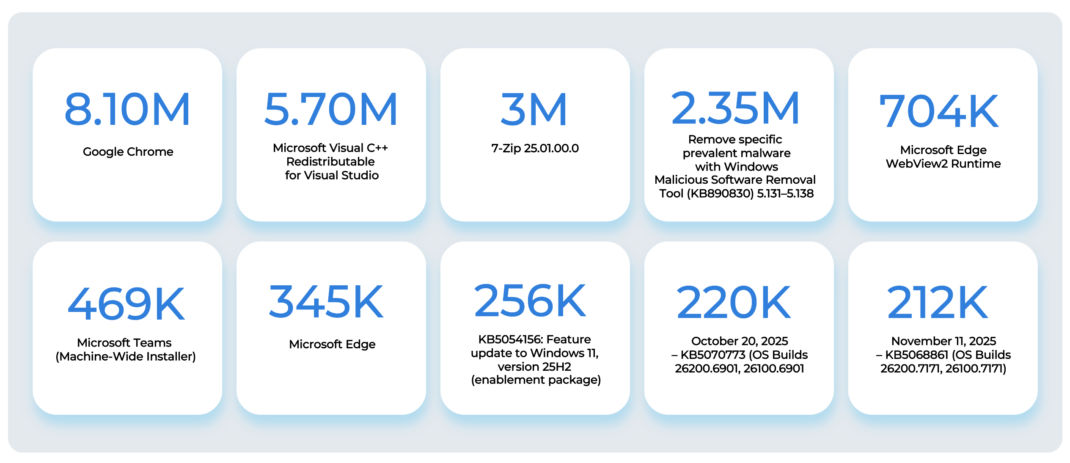
Patch deployment activity often reveals which technologies represent the largest operational risk. Across enterprise environments in the last 12 months, the following patches were deployed most frequently.
Most Deployed Enterprise Patches (last 12 months)
These deployment patterns highlight where remediation activity was concentrated globally.
Compare Your Environment
If you are a Qualys Patch customer, you can find these patches in our patch catalog by searching for
“patch.title:'Name of the Patch'“Why Third-Party Patch Automation Became Essential
Third-party applications represent a large and constantly changing part of the enterprise attack surface. Unlike operating systems, they update frequently, making them difficult to manage through manual patching processes.
To keep pace, many organizations have adopted zero-touch patch automation for widely used, low-risk applications.
Zero-touch patch automation refers to set-and-forget patch jobs that automatically deploy updates as soon as vendors release them without any manual intervention. Automation is primarily used for high-volume, low-risk applications that require frequent updates.
“With about 40 million of the 150 million patches deployed by Qualys in the last 12 months being autonomously deployed already, with no human in the loop, it’s clear that autonomous remediation is not the future, it’s already here!” – Sumedh Thakar, President & CEO at Qualys
Most Common Automated Patches

Together, these account for tens of millions of automated patch deployments.
For many teams, these applications now run in a “set-and-forget” update model, where patches deploy automatically when vendors release them.
Check your patch automation coverage. Are your most common applications patched automatically or do they still rely on manual update cycles?
Applications with the Longest Patch Delays
When a Patch Exists, but Deployment is Complex
Even when a security patch is available, patch management is often delayed due to application complexity and risk of disruption. Many systems are widely used across business-critical environments, requiring IT teams to validate compatibility, test for unintended impacts, and ensure production stability before deployment.
Because of this required testing and risk assessment, vulnerability remediation becomes a controlled process rather than a simple update.
Most Commonly Delayed Patches
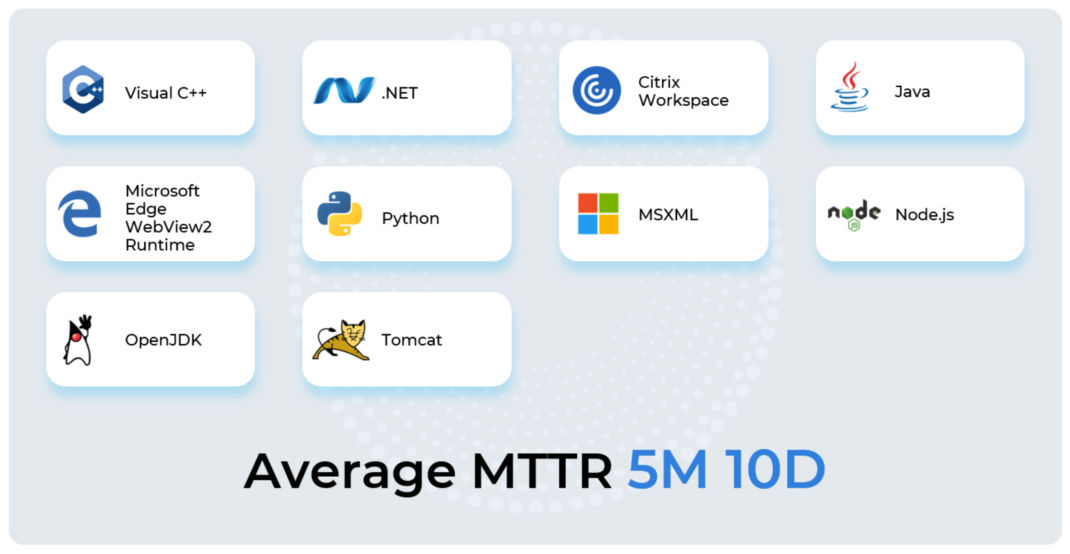
Across these applications, the average mean time to remediation (MTTR) was 5 months and 10 days.
This exposure window illustrates the operational complexity of enterprise patching.
Compare your vulnerability remediation timelines. How long did these applications remain vulnerable in your environment?
When No Vendor Patches Are Available
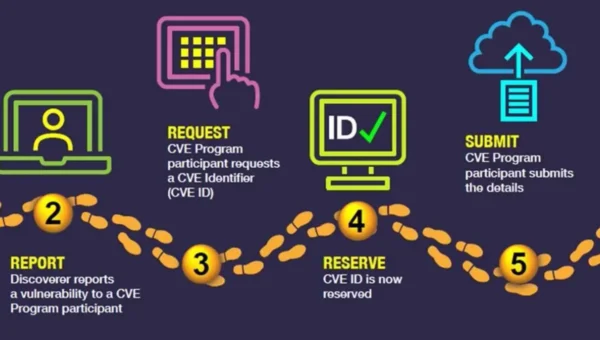
When no vendor patch exists, organizations must rely on vulnerability advisories and compensating controls instead of direct fixes. IT and security teams must interpret guidance, design custom mitigations, and validate changes across complex environments.
This makes vulnerability remediation a manual, risk-heavy process that often requires bespoke engineering effort. As a result, these exposures remain open significantly longer, driven by the lack of a direct remediation path and the need to avoid operational disruption.
Top 5 Qualys TRU Vulnerabilities Addressed Permanent Fixes (last 12 months)
Security teams can assess whether these vulnerabilities exist in their Qualys environment with a query such as:
vulnerabilities.vulnerability.qid:[378332,106247,383093,378941,90044]
or
vulnerabilities.qualysMitigableType:Fix
This exposure window illustrates the operational complexity of enterprise patching.
Check your vulnerability exposure. Have these vulnerabilities been fixed in your environment?
Remediation Beyond Patching
Modern exposure management extends beyond patch deployment. Event after patching, residual risks can remain. Over the last 12 months, organizations have increasingly used remediation scripts to eliminate these risks.
Most Common Qualys, Out-of-The-Box Remediation Scripts Used
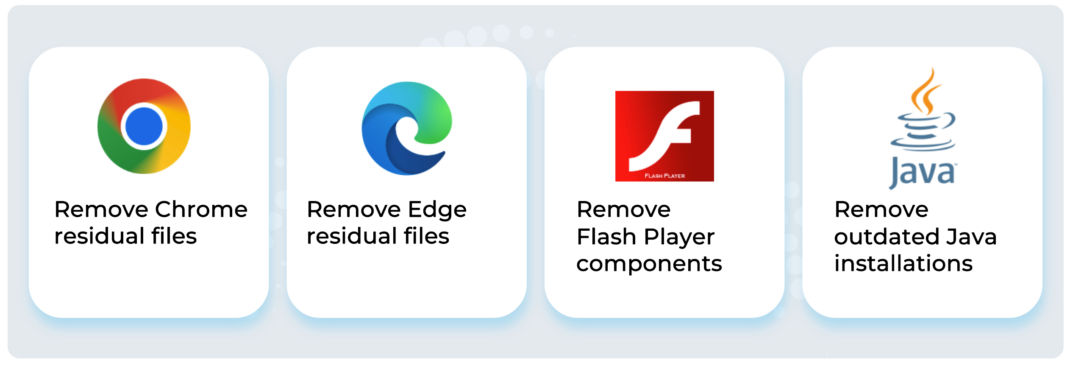
These scripts help ensure that remediation fully eliminates exposure rather than partially reducing it.
What These Trends Mean for Security Teams
Enterprise remediation is no longer just about applying patches. It’s about understanding how quickly risk can be reduced across complex environments.
That means looking beyond vulnerability counts and asking deeper operational questions:
- Which applications are driving the highest patch volumes in the environment?
- How do remediation timelines compare with industry averages?
- Are vulnerabilities without available patches being effectively mitigated?
- Is there sufficient visibility into hidden exposure, such as user-installed software?
Answering these questions helps security teams move from reactive patching to measurable exposure reduction.
The organizations making the most progress aren’t simply fixing vulnerabilities as they appear. They’re continuously evaluating how remediation performs across their environment, and where improvements can reduce exposure faster.
The trends from the last 12 months highlight that organizations that reduce risk most effectively are those that: deploy patches quickly, automate third-party updates, mitigate vulnerabilities without available patches, and continuously measure remediation performance. By benchmarking your remediation activity against global trends, you can identify where exposure persists and where improvements will have the greatest impact.
Start your free trial to benchmark your remediation performance and identify where to reduce risk faster.
Frequently Asked Questions (FAQs)
Which applications required the most patching in the last 12 months?
Everyday applications and browsers drove the highest patch volumes across global enterprises. Google Chrome led the way with over 8 million deployments, followed closely by Microsoft components like Visual C++ Redistributable and Edge. If these applications dominate your deployment activity, your organization aligns well with global enterprise benchmarks.
How does zero-touch patch automation reduce enterprise risk?
Zero-touch automation eliminates the manual workload required to update high-frequency third-party applications like Chrome, 7-Zip, and Zoom. It drastically shortens remediation timelines and guarantees consistent patch coverage. By adopting a “set-and-forget” model, you empower your IT teams to focus on critical, complex security threats instead of routine maintenance.
What is the global benchmark for Mean Time to Remediation (MTTR)?
In 2025, the average MTTR for complex enterprise applications reached 5 months and 10 days. Technologies like Java, .NET, and Citrix Workspace App frequently experience delayed patching due to compatibility testing and rigid uptime requirements. Measure your own MTTR against this benchmark to determine if your exposure window is wider than necessary.
How can we handle vulnerabilities when no patch is available?
When vendors have not released a fix, or an application reaches end-of-life, you must rely on permanent mitigations. Organizations successfully deployed specific remediation fixes to address severe exposures in the last 12 months, including vulnerabilities actively exploited and listed on the CISA KEV catalog. Deploying these mitigations is a strict compliance requirement to secure your infrastructure.
How can I evaluate and improve my organization’s remediation strategy?
You need clear visibility into your patch deployment timelines, automation coverage, and unmanaged endpoints. Use Qualys to query your environment directly and compare your performance against the 2025 benchmarks. Qualys TruRisk Eliminate provides a comprehensive solution to eliminate risks effectively. Launch your assessment today to centralize your patch management and automate your workflows!