Hackers are abusing the Ethereum blockchain to hide and control a new Node.js backdoor called EtherRAT, using a stealthy technique known as EtherHiding to make their command‑and‑control (C2) infrastructure difficult to disrupt.
EtherRAT, previously profiled by Sysdig and linked to North Korean “Contagious Interview” activity, is a Node.js backdoor that lets attackers run arbitrary commands, harvest credentials and cryptocurrency wallets, and perform deep host fingerprinting.
TRU also observed overlaps between EtherRAT and the Tsundere Malware‑as‑a‑Service botnet, including similar OS fingerprinting commands, CIS language checks, delivery via IT support scams and ClickFix, and extensive use of the free Obfuscator.io JavaScript obfuscator.
In March 2026, eSentire’s Threat Response Unit (TRU) detected EtherRAT inside a retail customer’s environment, marking a live intrusion that combined social engineering, Windows living‑off‑the‑land binaries, and blockchain‑based C2 resolution.
Ethereum-Based EtherRAT
EtherRAT, followed by a C2-delivered module we’ve dubbed “SYS_INFO” that performs extensive host fingerprinting – information the threat actors use to support target selection and decisions for follow-on payloads.
TRU most often sees Microsoft Teams‑based IT support scams followed by QuickAssist for interactive remote access.
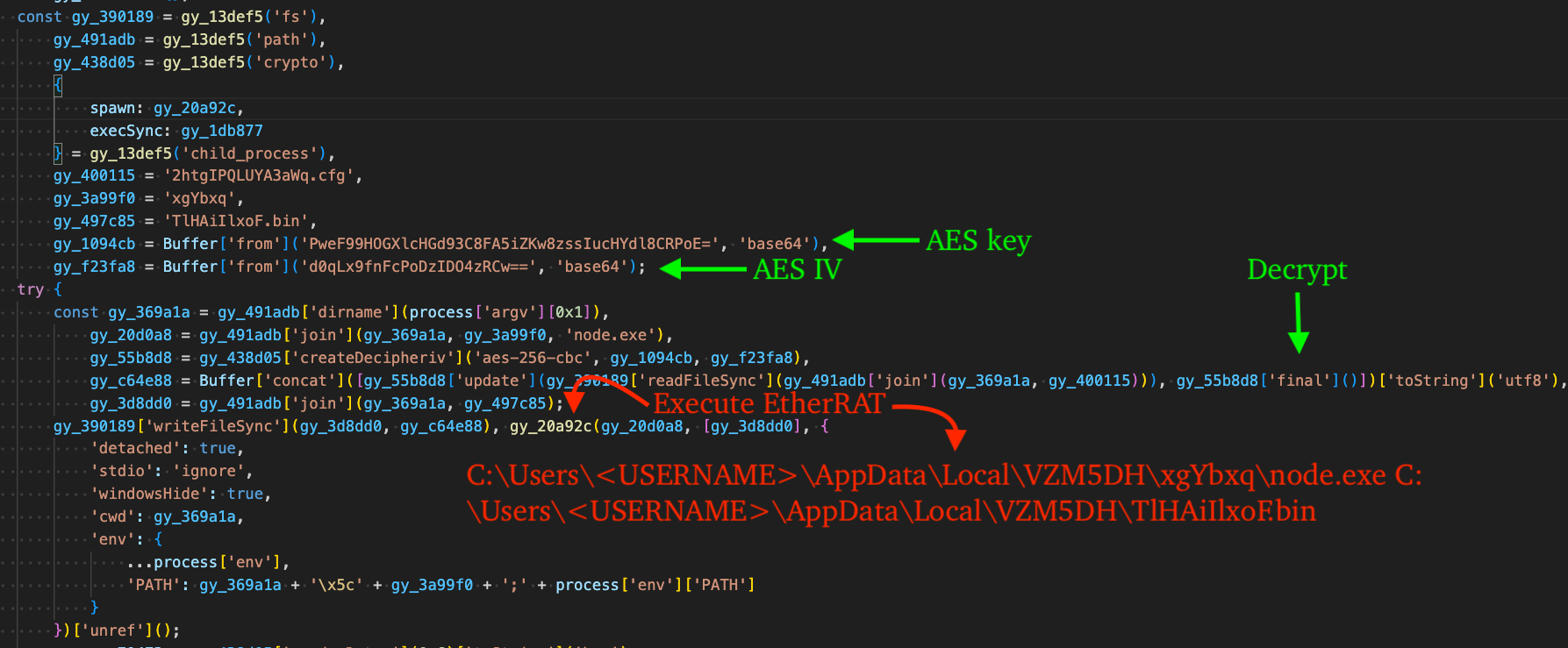
A second, heavily Obfuscator.io‑protected stage decrypts and launches the EtherRAT payload stored in “2htgIPQLUYA3aWq.cfg”, writes the obfuscated implant as “TLHA1IlxoF.bin”, and executes it via child_process.spawn(), then establishes persistence via a randomly named HKCU Run key using reg.exe.
The intrusion chain starts with a multi‑stage Node.js loader. The first stage decrypts an encrypted stager from “aeJ8aMT9ogQtKEb.dat” using AES‑256‑CBC and executes the next script in memory with Node’s internal module._compile(), keeping payloads largely off disk in early stages.
To make detection harder, the persistence command proxies node.exe execution through conhost.exe with an undocumented –headless argument, further blending into normal Windows process activity.
In the retail case, the attackers used a ClickFix command that abuses Indirect Command Execution (MITRE ATT&CK T1202), chaining pcalua.exe to start mshta.exe and retrieve a malicious “shep.hta” file from a compromised site, while using caret characters to obfuscate the command line and bypass some command‑line restrictions.
Once executed, the HTA drops and runs the multi‑stage Node.js loader, ultimately deploying EtherRAT and preparing the host for blockchain‑resolved C2 communications.
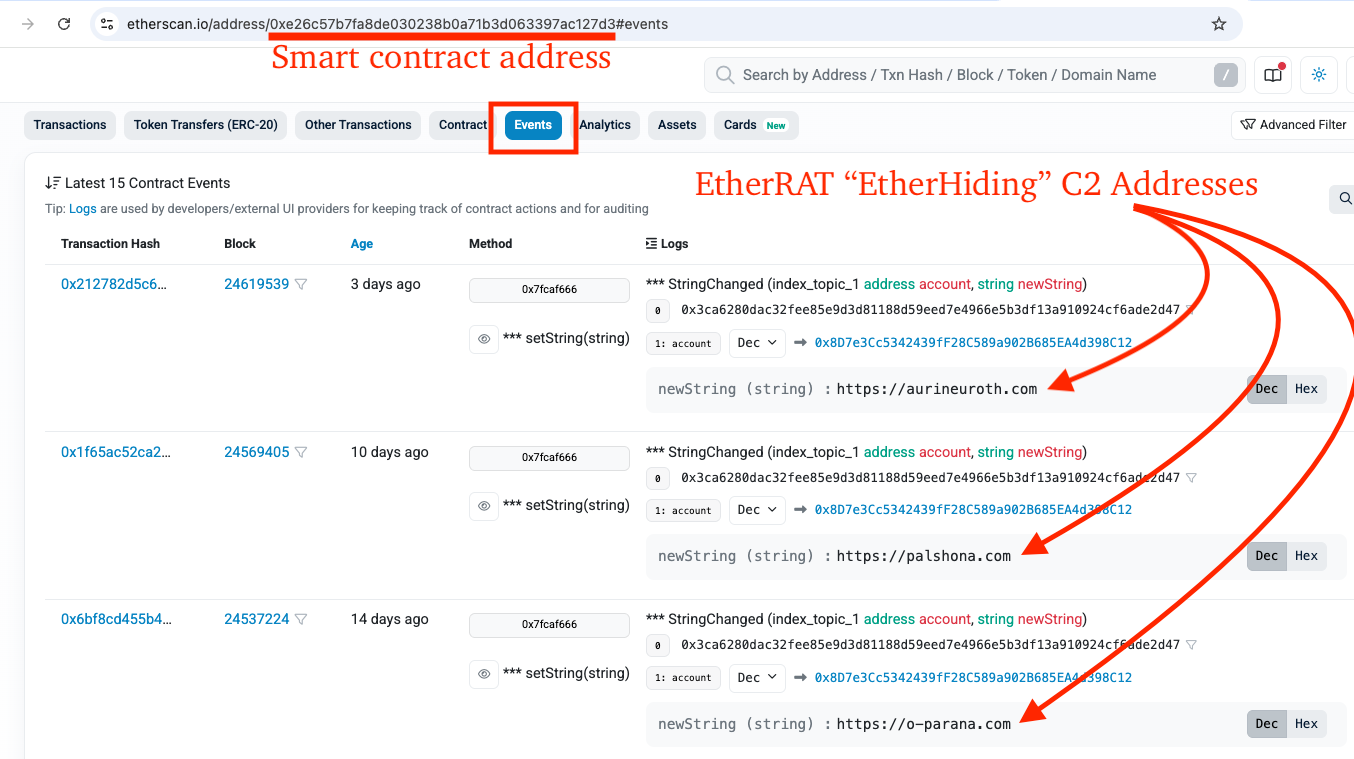
Instead of hard‑coding C2 domains, EtherRAT uses EtherHiding to retrieve C2 addresses from an Ethereum smart contract, turning the blockchain into resilient C2 infrastructure.
In TRU’s investigation, the smart contract at 0xe26c57b7fa8de030238b0a71b3d063397ac127d3 appeared repeatedly across cases in retail, business services, software, and finance, with attackers using the contract’s setString function to add and rotate C2 endpoints continually.
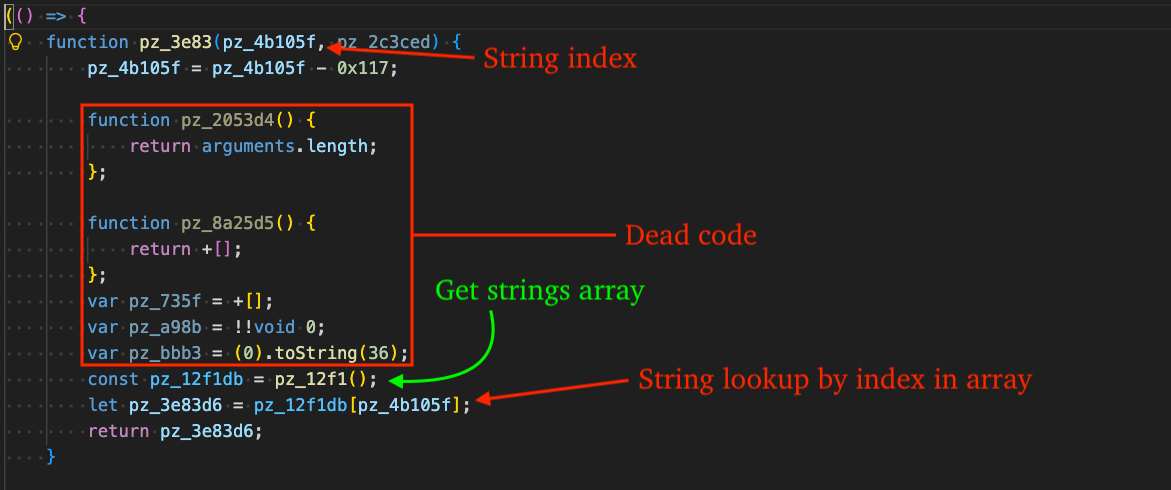
Several statements of “dead code”, effectively breaking the existing pattern matching in the isBasicStringArrayWrapper function.
EtherRAT queries multiple public Ethereum RPC endpoints in parallel and chooses the most common C2 value returned, enabling attackers to reassert control over long‑dormant infections by paying only small gas fees to update the contract state.
Mitigations
After resolving the C2, EtherRAT builds beacon URLs that mimic routine CDN traffic, using HTTPS, a common “/api/” path, random hex segments, UUIDs, and benign‑looking extensions like .png, .css, or .ico, with randomized query parameters such as id, token, or b.
From these endpoints, the C2 can push additional code modules, including a “SYS_INFO” module that performs extensive host fingerprinting: public IP, hardware and OS details, GPU name, AV presence, domain settings, admin status, and machine identifiers, while self‑destructing on systems configured with CIS languages.
EtherRAT can also enable debug logging to %APPDATA%svchost.log and supports a reobfuscation routine that uploads its current source code to the C2, receives a differently obfuscated but functionally identical copy, overwrites itself, and restarts, frustrating static detection signatures.
Blocking unneeded crypto‑network RPC providers, deploying NGAV or EDR capable of detecting Node.js malware and LOLBin abuse, and partnering with 24/7 MDR services provide essential coverage against advanced threats that now hide their infrastructure on public blockchains.
TRU’s analysts isolated the affected host, contained the intrusion, and are rolling out updated detection content across endpoint, log, and network telemetry in their managed detection and response (MDR) stacks.
Organizations should disable mshta.exe and pcalua.exe where possible, restrict the Run prompt, and invest in phishing and security awareness programs that simulate IT support scams and tools like ClickFix and QuickAssist to harden users against social engineering.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.