Two significant threat campaigns from March 2026, one abusing Microsoft’s OAuth authentication flow to silently hijack enterprise accounts, and another deploying the AMOS infostealer against macOS users who work with AI development tools like Claude Code.
The EvilTokens campaign represents a significant evolution in phishing tactics because it completely bypasses the need to steal passwords.
Rather than cloning a fake login page, attackers abuse Microsoft’s OAuth 2.0 Device Code flow, a legitimate authentication method originally designed for input-limited devices like smart TVs, to trick victims into authorizing attackers’ sessions through Microsoft’s own infrastructure.
The attack is deceptively simple. Victims receive phishing emails directing them to enter a device verification code at microsoft[.]com/devicelogin, a real Microsoft page.
Reduce the risk of delayed detection. Help your team investigate faster and respond earlier with ANY.RUN.
.webp)
After the user completes their login and satisfies MFA, Microsoft issues OAuth access and refresh tokens directly to the attacker, making MFA protections entirely ineffective. The victim never submits credentials to a fake site, rendering most traditional phishing detection methods useless.
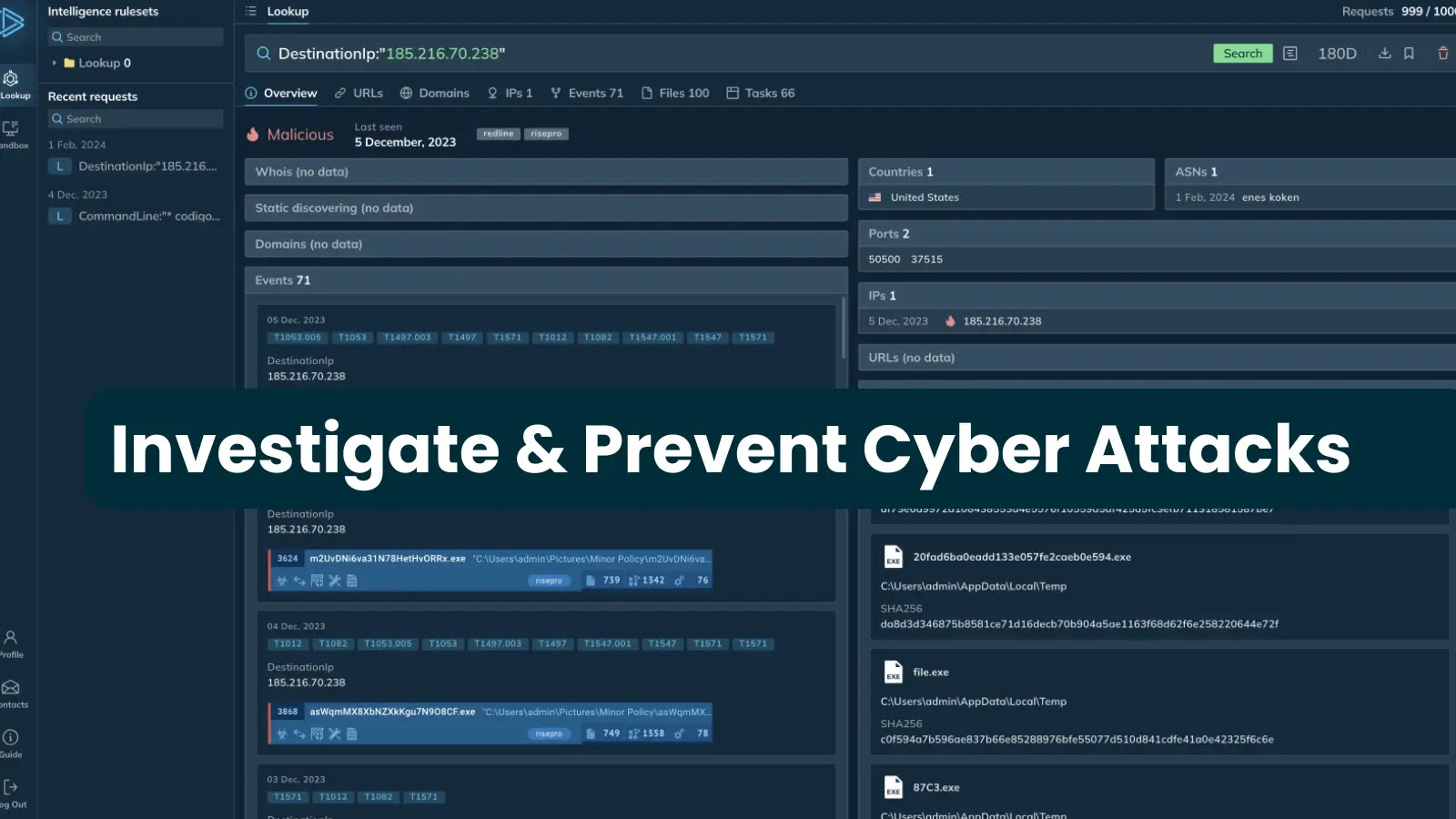
ANY.RUN analysts detected over 180 phishing URLs in a single week tied to EvilTokens activity, with targeting concentrated across Technology, Education, Manufacturing, and Government sectors, particularly in the United States and India.
The scale and speed of the campaign is compounded by EvilTokens operating as a Phishing-as-a-Service (PhaaS) platform, sold through Telegram with built-in automation, email harvesting, reconnaissance capabilities, and AI-powered features.
In advanced post-compromise scenarios, attackers can leverage harvested refresh tokens to register an additional device in Microsoft Entra ID, then silently request a Primary Refresh Token (PRT) providing persistent, MFA-bypassing access to the full breadth of an organization’s Microsoft 365 applications.
Key network indicators to hunt for:
/api/device/startand/api/device/status/*in HTTP requests to non-Microsoft hostsX-Antibot-Tokenheader presence in suspicious authentication traffic- Domains including
singer-bodners-bau-at-s-account[.]workers[.]devanddibafef289[.]workers[.]dev
macOS ClickFix: Claude Code Users Hit with AMOS
In a parallel campaign targeting macOS environments, threat actors deployed a sophisticated ClickFix attack chain against developers using AI coding tools.
Attackers purchased Google Ads to redirect victims searching for Claude Code, Grok, n8n, NotebookLM, Gemini CLI, and Cursor to convincing fake documentation pages that instruct users to run a terminal command — a hallmark of the ClickFix social engineering technique.
.webp)
Once the obfuscated terminal command executes, the infection chain moves through multiple stages:
- Google Ads redirect sends the victim to a counterfeit Claude Code documentation page
- ClickFix lure instructs the user to paste and run a terminal command
- Encoded script is downloaded and executed in the background
- AMOS Stealer harvests browser credentials, saved passwords, macOS Keychain contents, and sensitive files
- Backdoor deployment via the
~/.mainhelpermodule establishes a persistent reverse shell over WebSocket with full PTY support.
The evolution of the ~/.mainhelper backdoor module is particularly alarming. Previously described as a limited implant, the updated variant now supports a fully interactive reverse shell, giving attackers real-time, hands-on access to the infected system long after the initial infection.
.webp)
Boost early threat detection and accelerate triage with cross-platform threat analysis trusted by 15K organizations worldwide.
For enterprise environments, this is catastrophic macOS endpoints often belong to developers who hold privileged access to internal repositories, cloud infrastructure, and business-critical credentials.
The multi-stage nature of the attack obfuscates scripts, encoded payloads, and the abuse of native macOS components, deliberately fragmenting the compromise into weak, isolated signals that can delay security team triage and escalation.
For the EvilTokens threat, organizations should audit Microsoft Entra ID sign-in logs for device code authentication flows originating from unfamiliar devices or locations, implement Conditional Access policies restricting the Device Code grant type, and regularly rotate OAuth tokens for high-privilege accounts.
For the macOS ClickFix/AMOS campaign, defenders should block execution of unsigned scripts from terminal prompts via MDM policy, monitor for outbound WebSocket connections from developer endpoints, and deploy endpoint detection tuned to ~/.mainhelper persistence mechanisms and AMOS behavioral patterns, including Keychain access and bulk credential file reads.
Both campaigns highlight a broader March 2026 trend: attackers are deliberately weaponizing trusted infrastructure and normal-looking workflows legitimate Microsoft pages, Google Ads, and authentic AI tool documentation to push detection signals below the threshold where security teams can act quickly enough to prevent escalation.
Expand your SOC’s cross-platform threat visibility with ANY.RUN. Reduce breach risk with early threat detection across Windows, macOS, Linux, and Android.