EvilTokens is a new Phishing-as-a-Service (PhaaS) platform that industrialises Microsoft account takeover by abusing the OAuth device code flow rather than traditional credential phishing.
The service sells a turnkey Microsoft device code phishing kit that has been in active use since mid‑February 2026 and was quickly adopted by groups specialising in Adversary‑in‑the‑Middle phishing and Business Email Compromise.
Beyond simple token theft, EvilTokens bundles features such as access “weaponisation”, email harvesting, reconnaissance, a built‑in webmail interface, and AI‑driven automation to streamline BEC workflows.
In March 2026, Sekoia’s Threat Detection & Research (TDR) team identified EvilTokens while monitoring phishing-focused cybercrime communities.
The operation is run via fully featured Telegram bots, and the operators plan to extend their phishing pages to Gmail and Okta in future versions.
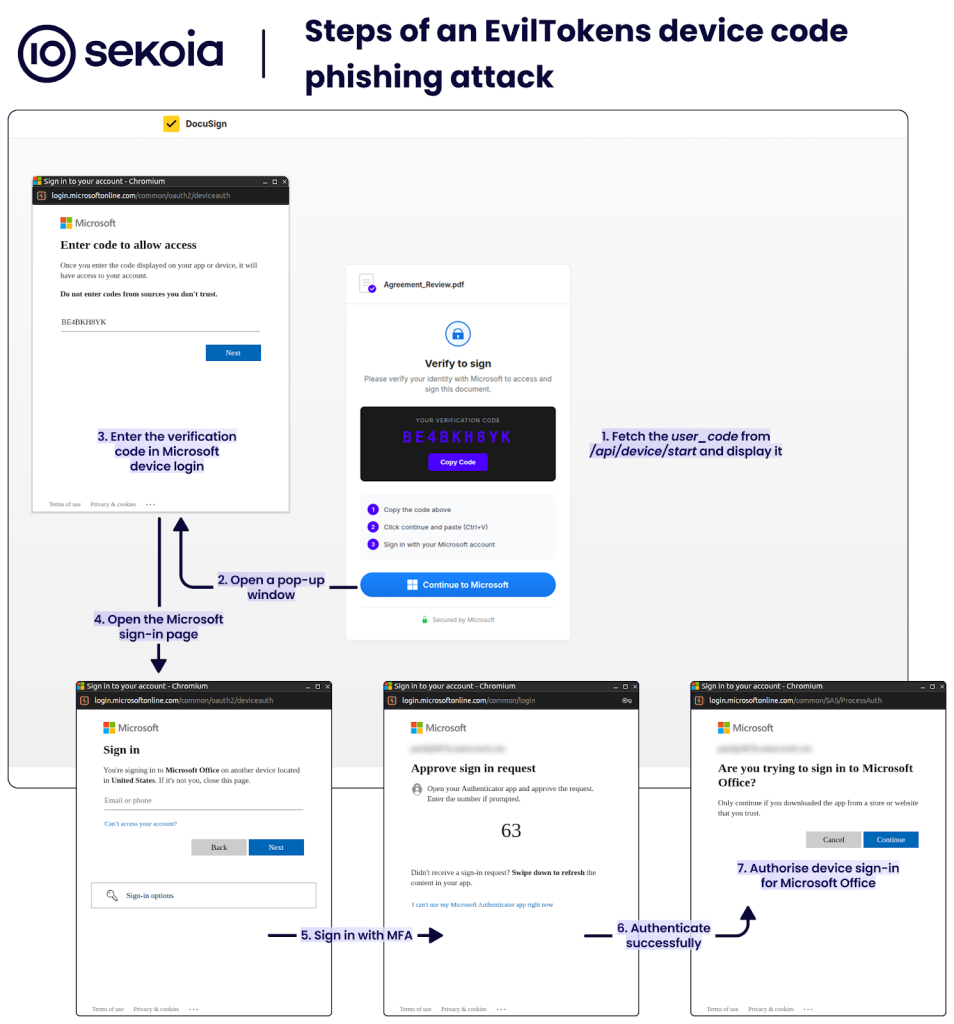
How device code phishing works
EvilTokens targets Microsoft 365 by abusing the OAuth 2.0 Device Authorisation Grant, a flow originally designed for devices like smart TVs and printers that cannot display full login experiences.
In the legitimate flow, a device calls /oauth2/v2.0/devicecode to obtain a device_code and a human‑readable user_code, the user visits microsoft.com/devicelogin to enter that code, and Microsoft then issues an access_token and refresh_token via the tenant’s /oauth2/v2.0/token endpoint.
Device code phishing exploits this split authentication model: the attacker initiates the device code request, then tricks the victim into entering the attacker’s user_code on the real Microsoft page.
Once the victim completes sign‑in and MFA, the attacker silently polls the token endpoint and harvests valid access and refresh tokens for the chosen Microsoft service.
These tokens enable both immediate access and long‑term persistence. Short‑lived access tokens usually remain valid for roughly an hour, letting attackers read mail, files or Teams data right after the phish.
Refresh tokens are rolling 90‑day tokens that can silently mint new access tokens without further prompts, giving adversaries durable, MFA‑resilient access unless the tokens are revoked.
In more advanced scenarios, a stolen refresh token can be used to register a new device in Entra ID and obtain a Primary Refresh Token, enabling seamless single sign‑on and lateral movement across other Microsoft 365 applications.
EvilTokens provides affiliates with self‑hosted phishing templates that impersonate familiar services such as Adobe Acrobat Sign, DocuSign, OneDrive, SharePoint, voicemail portals and password expiry alerts.
Each page displays a verification code, step‑by‑step instructions, and a “Continue to Microsoft” button that opens the genuine Microsoft device login page in a pop‑up, relying on the brand decoy to make users ignore the warning about untrusted codes.
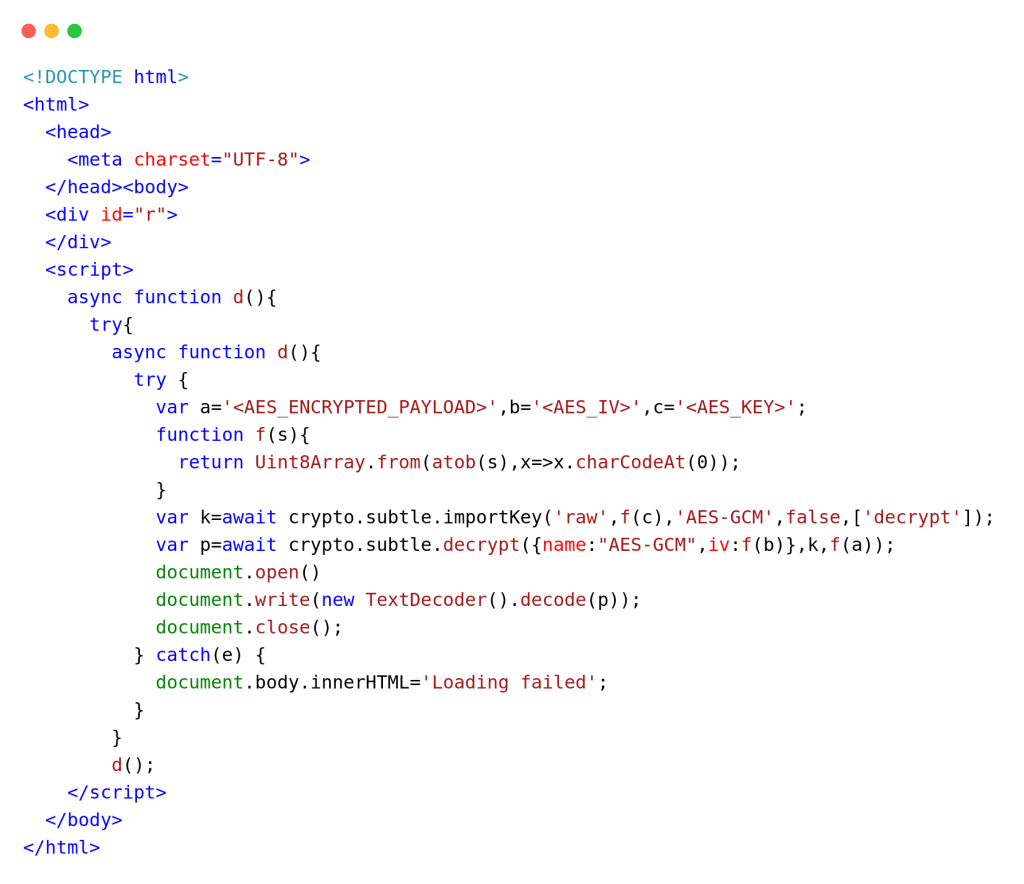
Under the hood, the HTML is reduced to an empty container and a script that fetches base64‑encoded content, decrypts it with AES‑GCM via the Web Crypto API, and injects the result, complicating static detection and analysis.
A single backend JavaScript handles the entire attack chain, from device code initiation to post‑compromise exploitation.
REST endpoints such as /api/device/start and /api/device/status/:sessionId proxy calls to Microsoft’s device and token APIs, store captured access and refresh tokens, notify operators via Telegram, and automatically attempt conversion of refresh tokens into Primary Refresh Tokens.
Additional APIs support reconnaissance with Microsoft Graph, Azure subscription enumeration, generation of x‑ms‑RefreshTokenCredential cookies for one‑click browser SSO hijacking, and creation of OWA sessions and related cookies.
Sekoia notes that the backend is cleanly structured and may have been heavily AI‑generated, reflecting how modern tooling lowers the barrier to building complex token‑abuse pipelines.
Global campaigns and victimology
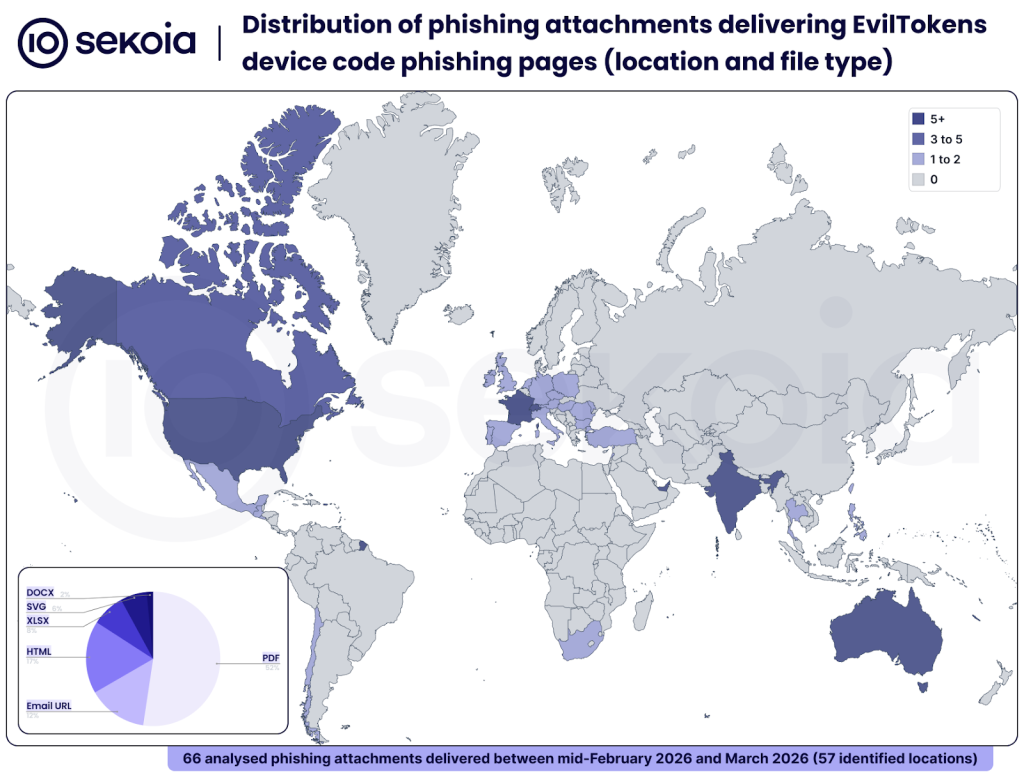
Sekoia’s telemetry shows EvilTokens is already used in broad phishing campaigns distributing PDF, HTML, XLSX, SVG and DOCX attachments that embed QR codes or links to device code phishing pages.
Lures primarily target finance, HR, logistics and sales staff with themes such as investment decks, meeting invitations, shipping notifications, payroll changes and “secure document” notifications, closely mirroring the templates offered by the platform.
By 19 March 2026, analysts had catalogued dozens of distinct lure documents and observed victims across the Americas, Europe, the Middle East, Asia and Oceania, with the United States, Australia, Canada, France, India, Switzerland and the UAE among the most affected countries.
Infrastructure analysis suggests more than 1,000 domains host EvilTokens pages, including many Cloudflare Workers subdomains matching predictable patterns tied to brands like Adobe, DocuSign, OneDrive and SharePoint.
On the content side, Sekoia has released a YARA rule that matches the characteristic AES‑GCM decryption logic inside the phishing HTML.
Defenders have several concrete hunting opportunities. At the network level, EvilTokens pages repeatedly call /api/device/start and /api/device/status/
Queries on urlscan.io and urlquery using these URL and header patterns have already surfaced hundreds of EvilTokens‑related URLs.
Given the rapid adoption, automation features and ability to bypass traditional username‑password phishing controls, Sekoia assesses EvilTokens will be a major competitor in the phishing and BEC ecosystem, with further reporting promised on its Telegram‑based orchestration and AI‑augmented fraud tools.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.