EvilTokens is a new Phishing-as-a-Service (PhaaS) platform that turns stolen Microsoft 365 tokens and AI into an end‑to‑end factory for Business Email Compromise (BEC) at scale.
By combining device-code phishing, custom tooling, and large language models, it enables low- to mid-skill threat actors to run highly tailored BEC operations in minutes rather than days.
First seen on Telegram in mid‑February 2026, EvilTokens is sold by an operator using the handle “eviltokensadmin” in private channels focused on AiTM phishing and BEC fraud.
The operator uses multiple Telegram resources: a main account for support, a channel for product updates and tutorials, and several bots for payments, affiliate management, landing page deployment (e.g., to Cloudflare Workers), and anti‑bot services.
EvilTokens offers three core products: a “B2B sender” for 600 USD, an “Office 365 capture link” for 1,500 USD, and an SMTP sender for 1,000 USD.
On 3 March 2026, Sekoia’s TDR first identified EvilTokens through its PhaaS offering, which was advertised by eviltokensadmin in a private Telegram channel.
The Office 365 capture link is the actual device code phishing kit, with a one‑time fee granting lifetime panel access and an additional monthly 500 USD license for the phishing page code and backend API key.
Payments are processed via NOWPayments, letting affiliates top up balances with multiple cryptocurrencies through the Telegram bot.
EvilTokens Uses Stolen Microsoft 365
To help affiliates operate at scale, the EvilTokens admin also sells a custom browser called “Portal Browser” or “ET Browser”, marketed via machinemind‑market[.]com.
This browser lets attackers open many Microsoft 365 accounts in parallel using stolen OAuth tokens, allegedly supporting Microsoft Admin, Azure, OneDrive, SharePoint, and Teams, while automatically refreshing tokens to maintain access.
EvilTokens was designed to support structured BEC fraud teams and may also enable the management of token sales directly within the PhaaS interface.
Sekoia assesses that this browser reflects strong expertise in Microsoft OAuth token management and was likely built first for the operator’s own BEC operations before being commercialised.
This move fits a broader criminal pattern where bespoke tools are repackaged into as‑a‑service offerings such as PhaaS, MaaS and other “kits‑for‑rent” ecosystems.
Code leaked in two public GitHub repositories appears to belong to an EvilTokens affiliate who uploaded the phishing kit to Railway.app for hosting.
The PHP‑based front end renders phishing pages mimicking DocuSign or Outlook and forwards traffic to a central backend via specific endpoints that start and monitor Microsoft device code flows, and register target emails for redirection.
Anti‑bot checks rely on User‑Agent filtering and a time‑based SHA256 token that acts as a lightweight safeguard.
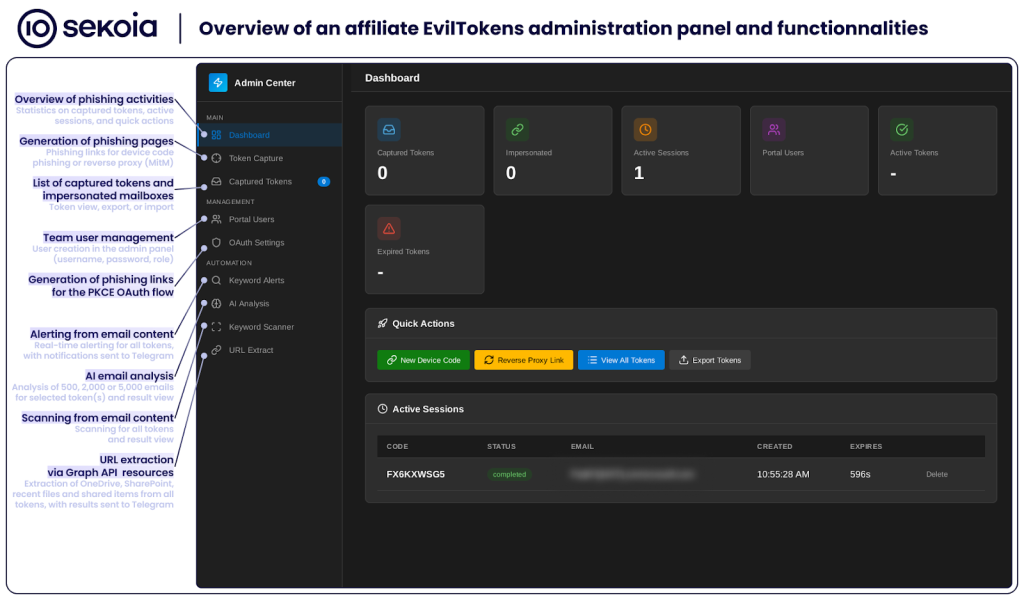
By pivoting from these repositories, researchers accessed a clean affiliate administration panel tied to the backend domain.
The panel allows affiliates to monitor hijacked sessions, view harvested access and refresh tokens, add and manage users for team operations, and search or exfiltrate mailbox content using built‑in collection features.
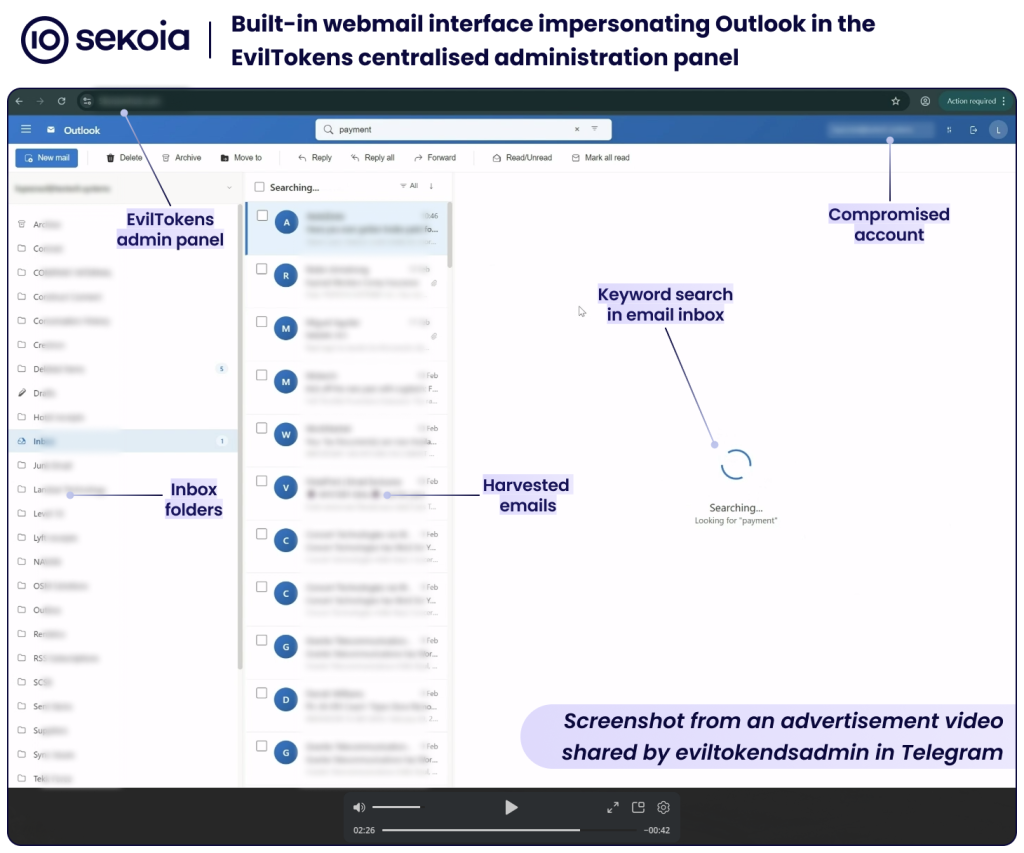
A webmail interface that imitates Outlook uses tokens directly, avoiding cookies or session replay and streamlining BEC operations for less technical actors.
AI‑driven BEC analysis pipeline
EvilTokens’ most disruptive capability is its AI‑driven pipeline for post‑compromise analysis and BEC planning.
Once victims complete the Microsoft device code flow, the backend captures tokens, exchanges them for wider access (including Primary Refresh Tokens), and runs Microsoft Graph API queries to map forwarding rules, finance‑related folders, key roles, meetings and organisational structures.
All this reconnaissance is compiled into a detailed report that is prepended to a series of large language model prompts.
In stage one, up to 5,000 emails are ingested via the Groq API using the llama‑3.1‑8b‑instant model to identify financial exposure, risky payment threads and key contacts.
In stage two, the results feed a second prompt, powered by llama‑3.3‑70b‑versatile, which synthesises a risk report, proposes attack scenarios and generates three tailored BEC email drafts ready to be sent from compromised accounts.
The pipeline also uses OpenAI gpt‑4o‑mini to auto‑translate non‑English emails into English, further lowering language barriers for operators.
Final outputs stats on stolen data, BEC scores, reconnaissance summaries and full HTML reports are pushed back to the attacker’s Telegram bot, alongside cookies derived from tokens for one‑click browser access that bypasses passwords and MFA.
By fully automating the path from initial phishing to mailbox intelligence and pre‑written BEC lures, EvilTokens sharply reduces attacker dwell time and the window defenders have to react.
It lowers the skills required for impactful BEC campaigns, enabling a wider range of threat actors to run convincing, context‑rich fraud against Microsoft 365 tenants.
Sekoia’s Threat Detection & Research team believes EvilTokens is the first PhaaS to integrate such AI‑augmented post‑compromise tooling, marking a significant evolution in the BEC ecosystem.
Organisations facing EvilTokens‑driven intrusions should expect more realistic, better‑timed BEC attempts and must strengthen token protection, Graph API monitoring, and mailbox anomaly detection to keep pace with this new wave of AI‑enabled fraud.
Follow us on Google News, LinkedIn, and X to Get Instant Updates and Set GBH as a Preferred Source in Google.






