Researchers spotted a new version of the RustBucket Apple macOS malware that supports enhanced capabilities.
Researchers from the Elastic Security Labs have spotted a new variant of the RustBucket Apple macOS malware.
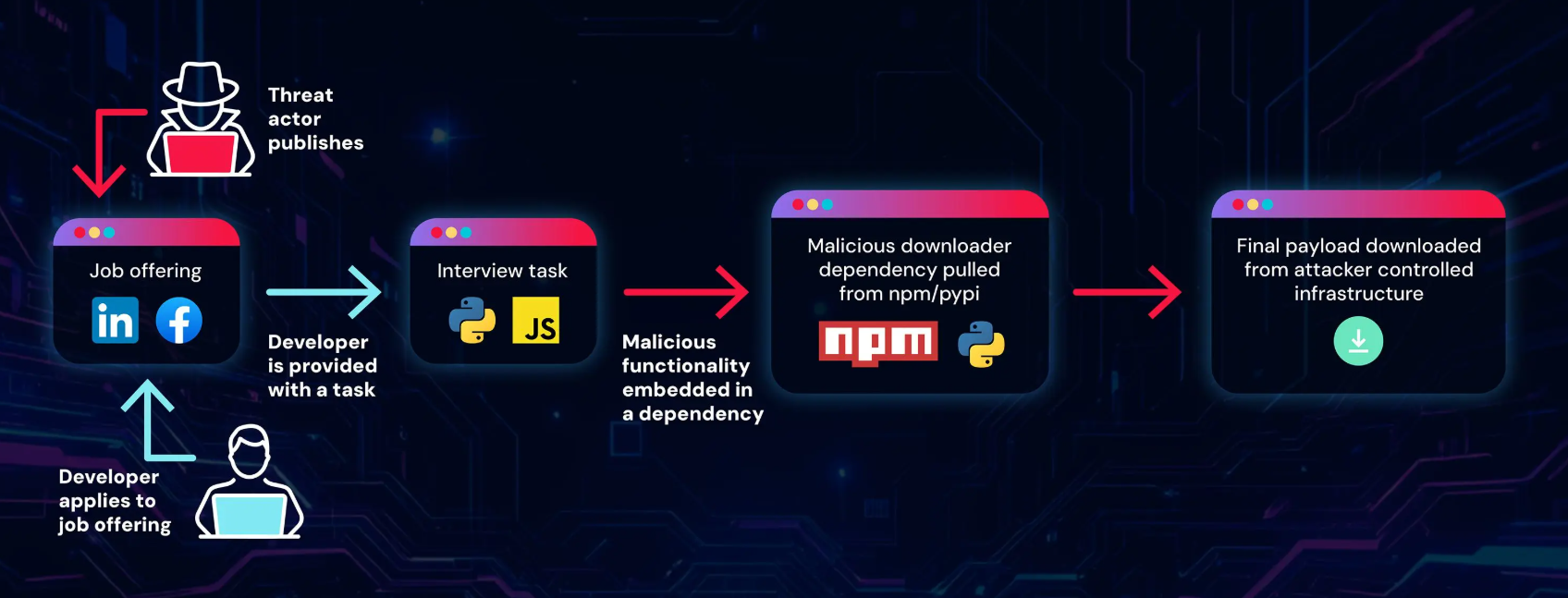
In April, the security firm Jamf observed the North Korea-linked BlueNoroff APT group using a new macOS malware, dubbed RustBucket.
The group BlueNoroff is considered a group that operates under the control of the notorious North Korea-linked Lazarus APT group.
The RustBucket malware allows operators to download and execute various payloads. The attribution to the BlueNoroff APT is due to the similarities in the findings that emerged from Kaspersky’s analysis published in December 2022. The similarities include malicious tooling on macOS that closely aligns with TTPs of those employed in the campaign.
The first-stage malware was contained within an unsigned application named Internal PDF Viewer.app. Experts believe the app can only be executed by manually overriding the Gatekeeper security measure.
The stage-one simply executes various do shell script commands to download the second stage malware from the C2 using curl. The malicious code extracts the contents of the zip file to the /Users/Shared/ directory and executes a stage-two application which is also named Internal PDF Viewer.app.
The second stage malware doesn’t use AppleScript, it masquerades as a legitimate Apple bundle identifier and is signed with an ad-hoc signature.
“When the Internal PDF Viewer application is launched, the user is presented with a PDF viewing application where they can select and open PDF documents. The application, although basic, does actually operate as a functional PDF viewer.” reads the analysis published by Jamf. “A task that isn’t overly difficult using Apple’s well-built PDFKit Framework.”
The stage-two malware communicates with the C2 server to fetch the stage-three payload, which is an ad-hoc signed trojan written in the Rust language. The trojan can run on both ARM and x86 architectures.
Upon executing, the malware collects system information, including the process listing, current time and whether or not it’s running within a VM.
This third-stage payload allows the attacker to carry out a broad range of malicious activities on the system.
The attribution to the BlueNoroff APt group is first based on the domain cloud[.]dnx[.]capital used in the stage-one dropper. The use of the domain was previously reported by experts from Proofpoint.
The new variant discovered by Elastic Security Labs is more evasive, at the time of its discovery the malicious code was undetected by VirusTotal, and has improved capabilities to maintain persistence.
“Our research has identified a persistence capability not previously seen in the RUSTBUCKET family of malware, leading us to believe that this family is under active development. Additionally, at the time of publication, this new variant has zero detections on VirusTotal and is leveraging a dynamic network infrastructure methodology for command and control.” reads the report published by Elastic Security Labs.

The analysis of the attack chain for the new variant revealed that during Stage 1, the process starts executing an AppleScript utilizing the “/usr/bin/osascript” command. The AppleScript downloads the Stage 2 binary from the C2 using cURL.
The second-stage malware is a binary compiled in Swift (.pd), it downloads the main component from the command-and-control (C2) server. The malware is a Rust binary that gathers info of the infected system (Computer name, List of active processes, Current timestamp, Installation timestamp, System boot time, and Status of all running processes within the system) and downloads and runs additional malicious code.
Upon execution, the malware uses the downAndExec function to prepare a POST HTTP request and utilizes specific macOS APIs for various operations.
The Stage 3 malware is written to disk and utilizes NSTask to start its execution.
The threat actor behind the malware, tracked by Elastic Security Labs as REF9135, targeted a cryptocurrency company providing services to businesses such as payroll and business-to-business transactions. The profile of the victim is aligned with the one of organizations targeted by the North Korea-linked BlueNorOff APT group.
The report includes indicators of compromise and the Yara rule for the detection of the threat.
Follow me on Twitter: @securityaffairs and Facebook and Mastodon
Pierluigi Paganini
(SecurityAffairs – hacking, Malware)